What Is the Difference Between IDS and IPS? a 2026 Guide
What Is the Difference Between IDS and IPS?
You’re probably here because one exam objective keeps blurring together in your notes.
You read IDS detects and IPS prevents, nod along, then hit a practice question that adds inline, out-of-band, false positives, anomaly-based detection, or host-based vs network-based. Suddenly, the distinction feels less clear. That’s normal. This is one of those cybersecurity topics that seems simple at first, then gets tricky the moment an exam turns it into a scenario.
A classic Security+ style prompt sounds like this: a company wants to monitor suspicious activity on an internal segment without interrupting production traffic. Another asks which device is most likely to block legitimate packets if it’s tuned badly. A third describes a tool that can drop packets in real time and asks you to identify it. If you only memorized short definitions, those questions become guesswork.
The better approach is to learn what each system does, where it sits, how it detects threats, and why the exam writer chose it in that scenario. Once that clicks, "what is the difference between IDS and IPS" stops being a memorization problem and becomes a logic problem you can solve quickly.
IDS vs. IPS: Core Concepts for Your Certification Exam
A certification exam question might describe suspicious traffic reaching a server, then ask what the security device did next. Did it send an alert for an analyst to review, or did it block the traffic on the spot? That single difference decides whether the answer is IDS or IPS.
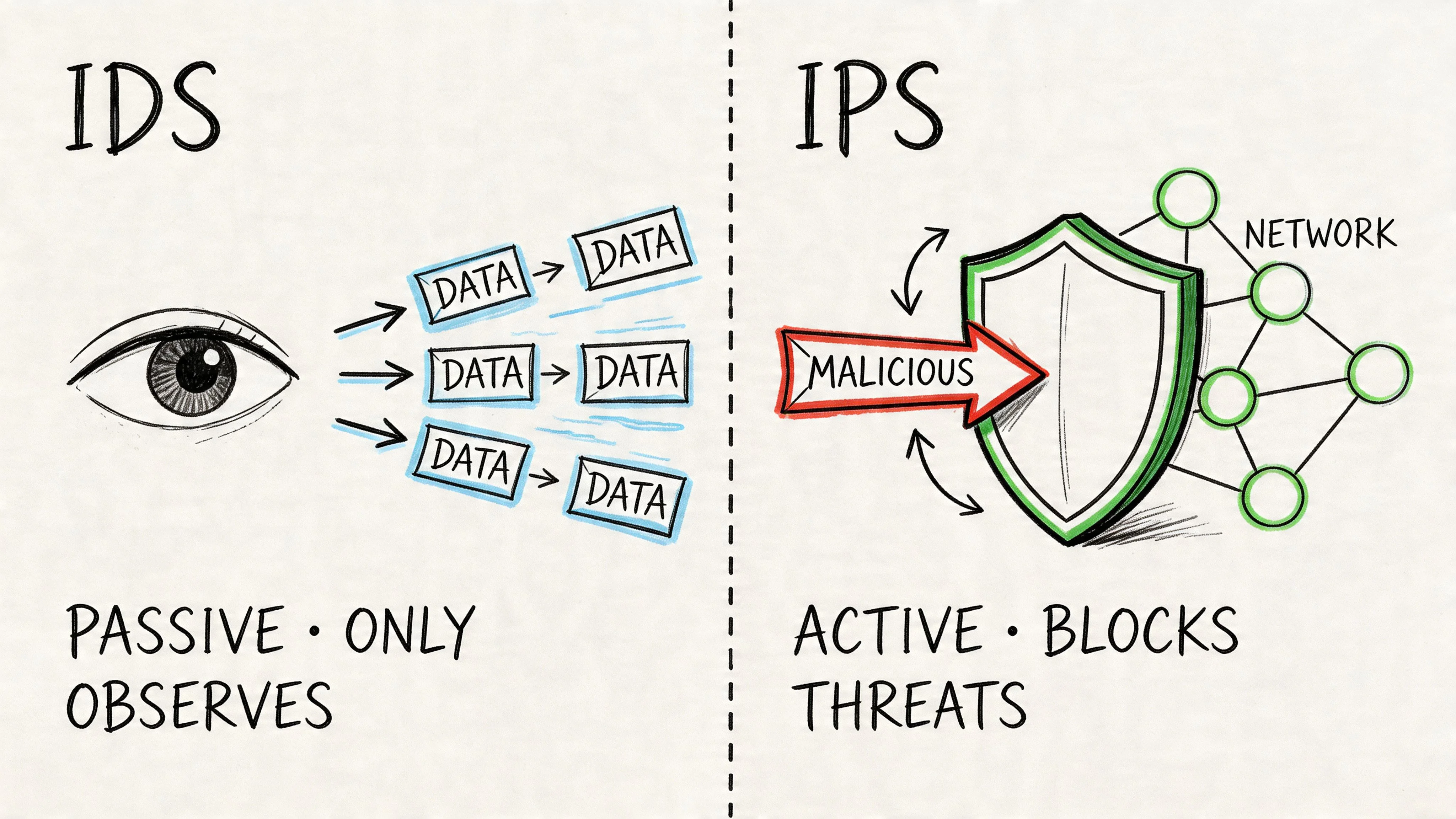
For exam prep, start with the shortest accurate rule you can remember. IDS detects and alerts. IPS detects and prevents. Security+ and CISSP questions often hide that distinction inside scenario wording, so train yourself to look for the action that happens after detection.
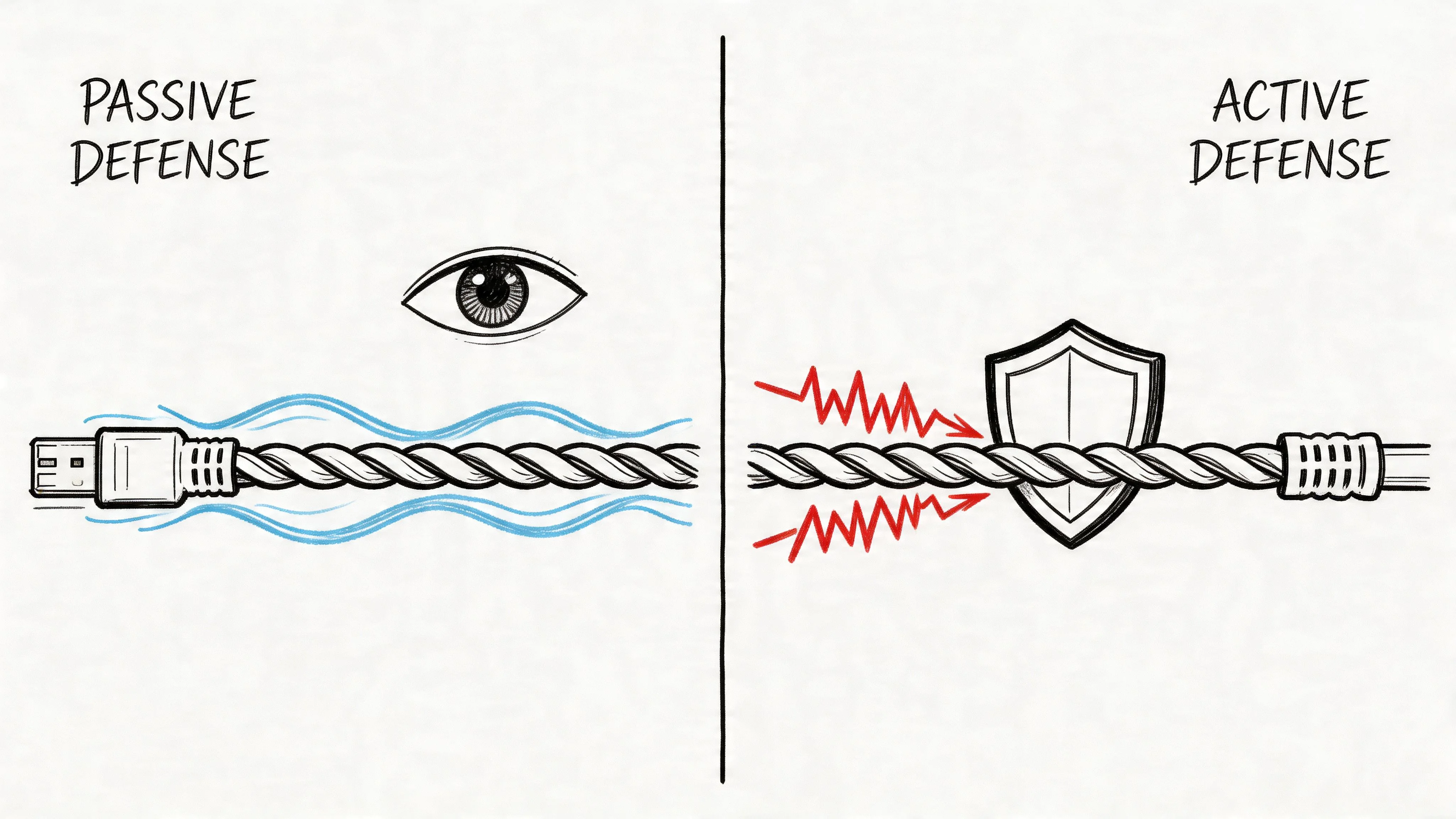
This topic trips people up because both technologies inspect traffic for signs of attack and may use similar detection approaches. The separation point is the response. An IDS usually gives visibility, logging, and evidence for investigation. An IPS is placed where it can take action immediately, which also means bad tuning can block legitimate traffic.
A useful classroom analogy is a smoke detector versus a sprinkler system. The smoke detector tells you there is a problem. The sprinkler system reacts on its own. On the exam, those two behaviors map directly to passive monitoring versus active prevention.
Exam mindset: Ask, “After the system identifies suspicious activity, who acts next? A person or the device?”
If a human analyst must review the alert and decide what to do, you are likely looking at an IDS. If the device can drop packets, reset connections, or stop malicious traffic in real time, you are likely looking at an IPS. This is why instructors often describe IPS as a superset of IDS capabilities.
Keep that framework in mind as you study. It helps you answer definition questions faster, but more critically, it helps you handle the scenario-based questions that CompTIA and CISSP prefer.
The Core Distinction: IDS vs. IPS in Action
Consider this exam scenario: A sensor identifies suspicious traffic headed toward a server. One answer says the system sends an alert to the SOC. Another says the system drops the packets before they arrive. That single difference decides whether the answer is IDS or IPS.
For Security+ and CISSP study, keep the distinction tied to the system’s response after detection. Both technologies inspect traffic and look for signs of attacks. The exam usually separates them by asking what happens next. Does the device report the event, or does it intervene?
What IDS does
An Intrusion Detection System identifies suspicious activity and generates an alert for a person or team to review. It may log the event, mark the traffic as suspicious, and preserve evidence for investigation. The key point is simple. The IDS does not automatically stop the traffic flow.
That is why exam writers connect IDS with words such as alert, monitor, observe, log, and notify. If the scenario describes a tool that detects hostile behavior but leaves the response to an analyst, the better answer is usually IDS.
This distinction matters in real incidents too. During events tied to Draytek security vulnerabilities, a detection-focused tool can help security teams spot suspicious behavior and start investigation quickly, even if another control handles the actual blocking.
What IPS does
An Intrusion Prevention System also detects suspicious or malicious traffic, but it is designed to take action automatically based on its rules and signatures. That action can include dropping packets, resetting a connection, or blocking traffic that matches an attack pattern.
For exam purposes, connect IPS with action words such as block, prevent, drop, terminate, and enforce. If the scenario says the security control reacts in real time without waiting for a human decision, the answer is usually IPS.
Students often confuse IPS with a firewall. A firewall mainly applies access control rules such as source, destination, port, and protocol. An IPS examines traffic for malicious behavior or content and then stops it based on that analysis. If you want to prepare for network security certifications, that distinction shows up often in product comparison questions.
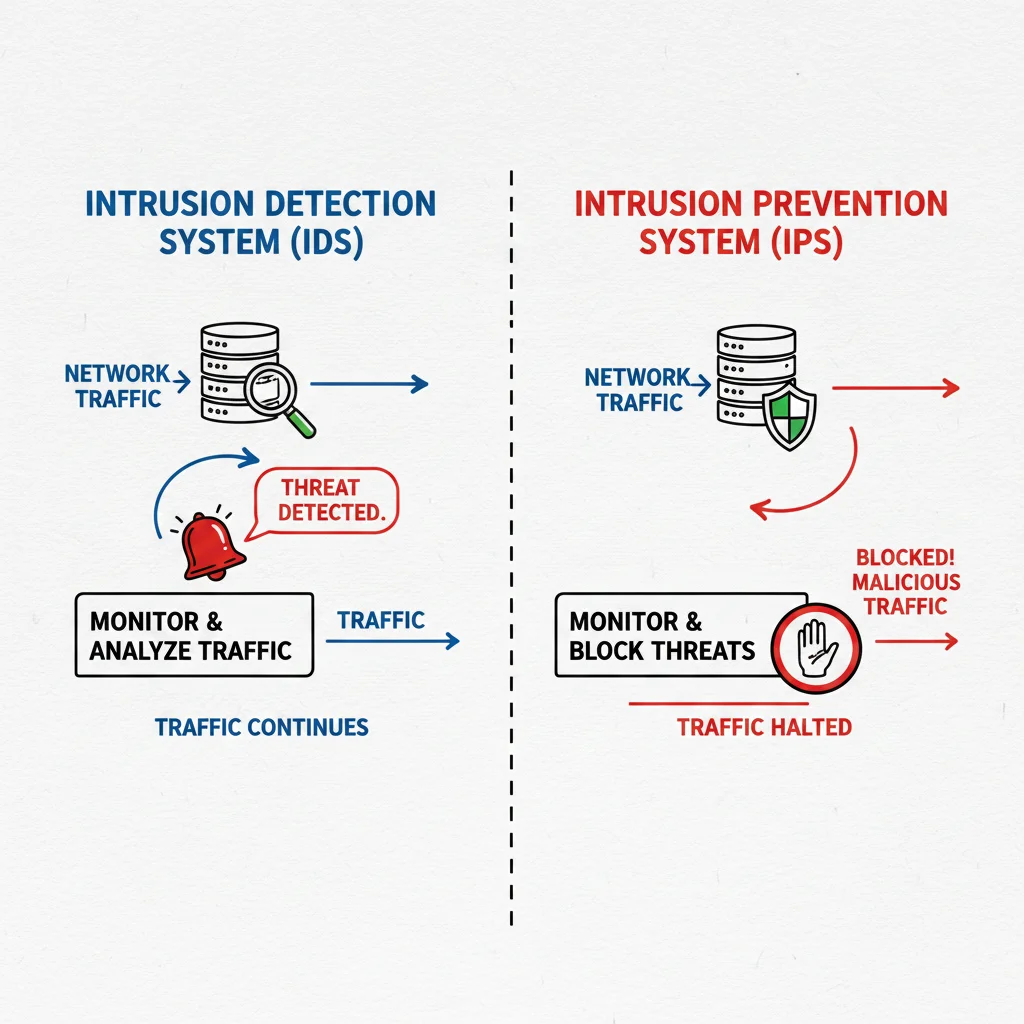
A quick visual walkthrough can help lock this in before you move on.
The sentence you should memorize
If you remember only one sentence, make it this:
IDS tells you there’s a problem. IPS tries to stop the problem.
Use that line as a test-taking shortcut. When a question feels wordy, strip it down to one checkpoint. After detection, who acts next: a human analyst or the device itself?
Detection and Deployment: How IDS and IPS Operate
A Security+ question gives you this setup: a company wants visibility into suspicious traffic but cannot risk adding delay to a busy production link. Another company wants malicious sessions stopped before they reach a server, even if that adds inspection overhead. If you miss the deployment clue, you miss the question.
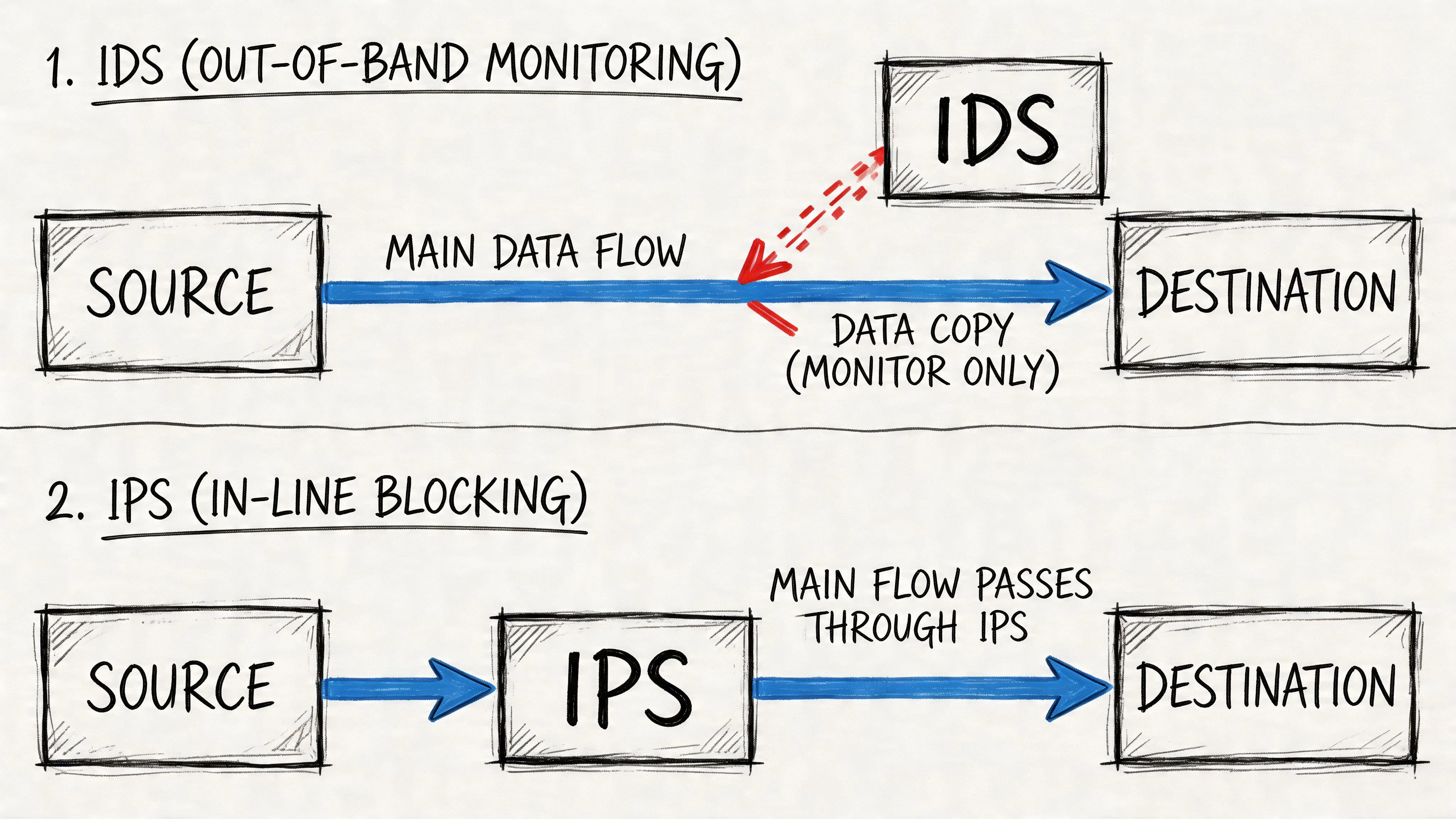
Out-of-band versus inline
Placement explains behavior.
An IDS is usually deployed out-of-band. It monitors a copy of traffic from a network tap or switch port mirror. A good classroom analogy is a security camera watching a hallway. The camera can record what happened and alert the guard, but it cannot physically stop someone from walking through the door.
That design gives IDS an exam-friendly advantage. Because it is not sitting directly in the traffic path, it usually has less impact on performance and less risk of interrupting legitimate sessions. The tradeoff is just as testable. Since it only observes traffic, it cannot directly block packets on its own.
An IPS is usually deployed inline. Traffic flows through it before reaching the destination. That makes it more like a badge checkpoint than a camera. If the device sees malicious traffic, it can drop the packet, reset the connection, or block the session before it continues.
For exam questions, connect deployment to consequences. Out-of-band points to visibility, lower disruption, and alerting. Inline points to enforcement, stronger immediate control, and the possibility of latency or accidental blocking if rules are too aggressive.
The three main detection methods
Another common exam trap is treating detection method and device type as if they are the same thing. They are not. IDS and IPS can both use the same detection methods. The difference is what happens after suspicious activity is identified.
Signature-based detection
This method compares traffic to known attack patterns. If a question mentions a known exploit, malware fingerprint, or rule update from a vendor, signature-based detection is the clue. On certification exams, the weakness is also testable. It is effective for known threats but weaker against brand-new attacks that do not match an existing signature.
Anomaly-based detection
This method compares current behavior to a baseline of normal activity. If a user suddenly transfers far more data than usual, or a host begins making unusual connections, anomaly detection may flag it. On the exam, this method is often linked to unknown threats, but also to false positives because unusual behavior is not always malicious.
Stateful protocol analysis
This method checks whether traffic follows the rules of a protocol. If the traffic claims to be using a protocol correctly but violates expected behavior, the system can identify that mismatch. Exam writers use this to test whether you can spot protocol misuse rather than just known signatures or statistical deviations.
Memorize the clue words. Known pattern means signature-based. Deviation from normal means anomaly-based. Protocol misuse means stateful protocol analysis.
Why history still shows up on certification exams
Security+ and CISSP questions sometimes ask why a control exists, not just what it does.
IDS came first because early defenders needed visibility into suspicious activity. As attacks became faster and more automated, organizations needed controls that could do more than alert after the fact. That pressure led to wider IPS adoption, especially in environments where stopping traffic immediately mattered more than keeping the monitoring tool completely passive.
For the test, the timeline matters less than the reason for the shift. Security teams wanted detection first. Then they needed prevention close to real time.
Real-world context students often miss
Deployment decisions become clearer when you tie them to actual incidents. A router or firewall vulnerability doesn't just create a patching problem. It creates a monitoring and containment problem too. The write-up on Draytek security vulnerabilities is a useful example of why teams need both visibility into suspicious behavior and a way to stop harmful traffic quickly.
To prepare for network security certifications, study deployment as a set of exam clues. If the scenario stresses monitoring, copies of traffic, and minimal interruption, lean toward IDS. If it stresses inline inspection, automatic blocking, and immediate containment, lean toward IPS.
IDS vs. IPS: A Side-by-Side Comparison
A certification exam rarely asks, “What does IDS stand for?” It asks which control fits a situation, what risk comes with that choice, and what tradeoff the security team is accepting. That is where a side-by-side comparison helps.
IDS vs. IPS Core Feature Comparison
| Attribute | Intrusion Detection System (IDS) | Intrusion Prevention System (IPS) |
|---|---|---|
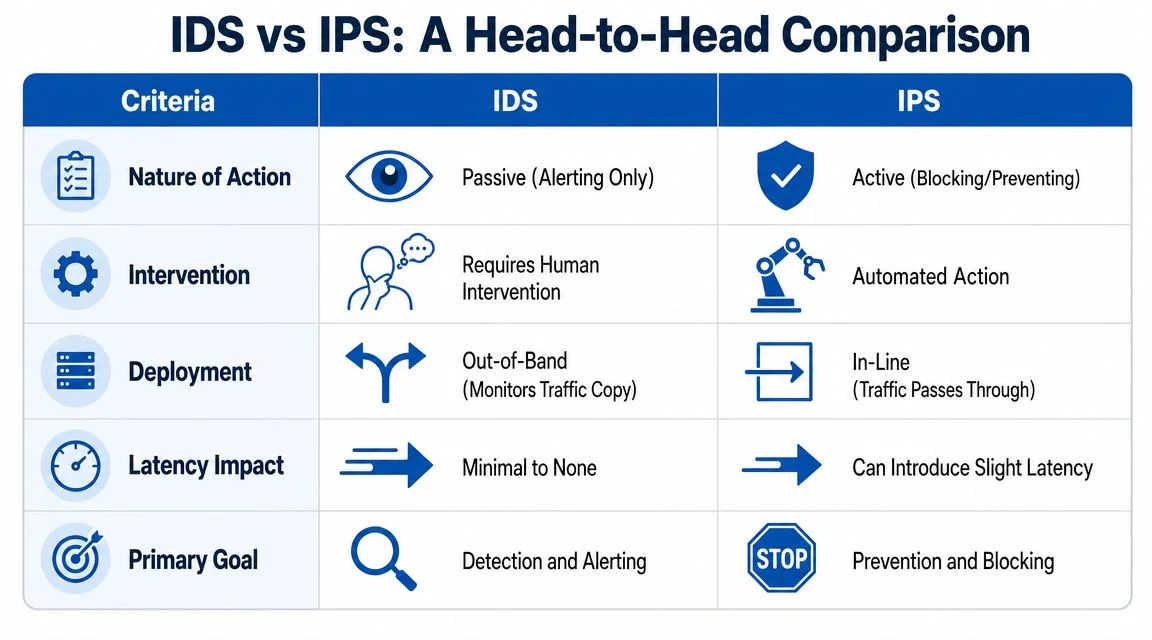
| Primary action | Detects suspicious activity and alerts | Detects suspicious activity and blocks or prevents |
| Response style | Human-driven follow-up | Automated enforcement |
| Usual placement | Out-of-band | Inline |
| Traffic impact | Minimal interference with normal traffic | Can affect traffic if misconfigured or overloaded |
| Main strength | Visibility, logging, investigation | Containment, immediate threat interruption |
| Main risk | Alert fatigue and delayed response | False positives that block legitimate traffic |
| Best exam clue | “Monitor,” “alert,” “log” | “Block,” “drop,” “prevent” |
Response and intervention
This is one of the highest-yield exam distinctions.
An IDS usually watches traffic and raises an alert for an analyst to review. An IPS sits in the path of traffic and can take action immediately, such as dropping packets, resetting connections, or blocking a session based on policy. For Security+ or CISSP-style questions, that difference often decides the answer faster than any vendor detail.
A simple way to remember it is this. IDS is like a smoke alarm. IPS is like a sprinkler system. Both react to danger, but only one acts on its own.
If the prompt says the organization wants a control that works without waiting for a person to respond, choose IPS. If the prompt says the team wants to observe suspicious behavior first and avoid automatic disruption, choose IDS.
False positives and why exam writers care
Students often understand “false positive” in theory but miss why it matters more for IPS.
With IDS, a false positive usually means an unnecessary alert. That creates extra work for analysts and can hide real threats in a pile of noise. With IPS, the same mistake can block legitimate traffic, interrupt business activity, or lock out users who did nothing wrong.
That is a favorite exam setup. If a question highlights a low tolerance for service interruption, production stability, or business continuity, IDS is often the safer choice.
A noisy IDS wastes analyst time. A noisy IPS can stop legitimate business traffic.
That sentence is short, but it captures a major testable difference.
Performance and reliability tradeoffs
Placement changes the risk.
Because IDS is commonly out-of-band, it usually observes a copy of traffic rather than sitting directly in the flow. That makes it useful for monitoring-heavy environments where teams want visibility with minimal effect on throughput. IPS has a harder job because it must inspect and decide in real time while traffic passes through it.
For the exam, watch for wording like “latency,” “throughput,” “bottleneck,” or “single point of failure.” Those clues usually point toward IPS concerns, not IDS concerns.
This tradeoff also shows up in real security programs built around implementing cybersecurity frameworks. Frameworks push teams to match the control to the business need, not just memorize the acronym.
Visibility, forensics, and layered defense
IDS usually gives stronger monitoring value for investigations, baselining, and threat hunting because its main job is observation. Analysts can review alerts, compare logs, and study suspicious patterns without the control interfering with traffic. IPS also logs events, but its first priority is enforcement.
On certification exams, this often appears as a “best control for forensic review” or “best option for monitoring without affecting operations” question. That wording points toward IDS. A prompt focused on stopping known malicious traffic before it reaches a target points toward IPS.
In real environments, many teams use both. Dupple's security tool analysis is a useful example of how monitoring and prevention tools often work together rather than replacing one another.
The exam shortcut
If you feel stuck between two answer choices, run this quick test:
- Need evidence, logs, and alerts without interrupting traffic? IDS
- Need automatic blocking or dropping of malicious traffic? IPS
- Need both monitoring and immediate containment? Use both, if the scenario allows layered controls
That shortcut will not solve every advanced architecture question. It will solve a large share of the foundational exam questions on this topic.
Deployment Scenarios: Choosing the Right Solution
The best way to lock this topic in is to stop thinking in product labels and start thinking in situations. Exam writers love scenarios because they reveal whether you understand the tradeoff, not just the acronym.
Compliance monitoring without disruption
A company needs to monitor access to sensitive systems and preserve logs for audit review. The security team wants visibility, but the business doesn’t want an automated control interrupting legitimate traffic during peak operations.
That’s a strong IDS scenario.
This is one reason IDS often appears in questions tied to compliance auditing. It supports monitoring and investigation without inserting an automated blocker into the transaction path. In a certification setting, if the prompt emphasizes oversight, recordkeeping, or observation without disruption, IDS is usually the better fit.
Internet-facing protection
A company exposes public services to the internet and wants to stop known malicious traffic before it reaches internal systems. Security staff don’t want to wait for an alert and then respond manually.
That points to IPS.
This is the classic perimeter defense use case. The exam usually signals it with words like “real-time,” “automated,” “immediate,” or “prevent malicious traffic from reaching the server.”
Internal threat monitoring
Some environments worry less about outside attackers and more about lateral movement, insider misuse, or malware spreading between internal segments. Here, teams often want broad visibility into suspicious behavior inside the network without risking disruption to internal workflows.
That’s where IDS sensors on internal segments make sense.
If you’re comparing monitoring options, resources such as Dupple's security tool analysis can help you think through where different monitoring technologies fit in a larger detection strategy.
The layered approach
Many organizations don’t choose one and ignore the other. They use IPS where immediate blocking matters most and IDS where visibility matters most.
That layered design often looks like this:
- At the perimeter: IPS enforces real-time blocking
- Inside critical segments: IDS watches for suspicious internal activity
- Around sensitive systems: both may be used as part of defense-in-depth
This is also where broader planning matters. If you’re thinking about where IDS and IPS belong in a larger security program, understanding implementing cybersecurity frameworks helps because the right deployment always depends on business risk, governance, and operational tolerance.
Choose IDS when the cost of blocking legitimate traffic is too high. Choose IPS when the cost of waiting is too high.
That single rule is surprisingly effective on scenario questions.
What students often pick incorrectly
Learners often choose IPS whenever they see the word “threat.” That’s too simplistic.
A prompt can describe a threat-heavy environment and still want IDS if the company’s priority is monitoring, auditing, or non-disruptive observation. The right answer depends on the required outcome after detection, not whether threats exist.
Tuning, Maintenance, and the Evolution of Hybrid Systems
A lot of students treat IDS and IPS like static boxes with fixed behavior. In practice, both require ongoing maintenance, and exam writers know that.
Tuning is part of the job
An IPS can only block safely if it’s tuned well. Security teams need to review what it flags, adjust rule sets, and account for legitimate business traffic that might resemble attack behavior. Otherwise, the IPS may do exactly what it was designed to do, just against the wrong traffic.
IDS also needs tuning. If it floods analysts with low-value alerts, they start ignoring important ones. That creates the opposite problem: the team has visibility on paper but poor response in reality.
A mature environment updates signatures, reviews baselines, and adjusts policies as applications and traffic patterns change. If a certification question asks what administrators should do after deployment, “ongoing tuning” is often part of the best answer.
Modern tools blur the line
The clean textbook split between IDS and IPS still matters for exams, but modern products often combine both capabilities. Next-generation firewalls and integrated security appliances can inspect, alert, and enforce in one platform.
That doesn’t erase the conceptual difference. It means you need to recognize the underlying function inside the broader product. If a next-generation firewall is only alerting on suspicious traffic, it’s behaving like IDS for that event. If it’s dropping packets or blocking connections automatically, it’s functioning as IPS.
AI-driven hybrids and exam nuance
Certification materials are increasingly touching on hybrid systems that use more adaptive analysis. The verified data notes that recent AI-driven IDS/IPS hybrids can show 40% fewer false positives in the certification-focused GeeksforGeeks summary.
You don’t need to become a machine learning specialist for Security+, but you should understand the exam takeaway: newer systems are trying to improve detection quality while reducing unnecessary alerts and accidental blocking.
The big lesson
Treat IDS and IPS as living controls, not checkboxes.
- Rules change because applications change.
- Baselines drift because user behavior changes.
- Threats evolve because attackers change tactics.
A student who understands that will do better on advanced exam questions than a student who memorized only a pair of definitions.
Mastering IDS and IPS for Your Certification Exam
You are sitting in a testing center. The question describes a hospital that needs visibility into suspicious traffic but cannot risk blocking patient-care applications. If you know the acronym only, you may hesitate. If you know the exam logic, the answer becomes clear.
Certification exams such as Security+ and CISSP usually test judgment, not memorization. The prompt often gives you a business priority first, such as uptime, visibility, automated response, or forensic evidence. Your job is to map that priority to the right control.
Common exam question patterns
These are the patterns that appear again and again on certification exams.
-
The monitoring without disruption question The organization wants to watch suspicious traffic, support investigations, or meet auditing requirements without interfering with production systems. Best answer: IDS.
-
The immediate enforcement question The organization wants malicious traffic stopped as it happens, without waiting for a human analyst to approve the action. Best answer: IPS.
-
The false positive risk question The prompt asks which control could accidentally block legitimate traffic and create an outage if tuned poorly. Best answer: IPS.
-
The layered defense question The prompt describes a need for visibility, alerting, and automatic protection in different parts of the environment. Best answer: a combined IDS and IPS strategy.
For exam purposes, remember the simple split. IDS watches and reports. IPS watches and acts. That single distinction solves many multiple-choice questions.
Quick practice prompts
Try these like mini exam drills.
A hospital wants to monitor suspicious internal traffic but refuses to risk blocking clinical application traffic during working hours.
Choose IDS. The deciding clue is uninterrupted service.
A retailer wants to stop known exploit traffic at the network edge the moment it appears.
Choose IPS. The deciding clue is automatic blocking.
A question asks which tool is more likely to disrupt service when it makes a false positive decision.
Choose IPS. It sits in the decision path and can block traffic.
Here is the study trick many candidates miss. Do not hunt for the acronym first. Hunt for the verb in the scenario first. Words like alert, monitor, observe, log, investigate point you toward IDS. Words like block, stop, prevent, drop, terminate point you toward IPS.
Study methods that work
Use more than one memory path so you can recall the concept under exam pressure.
- Draw the traffic path: Sketch a firewall, an inline IPS, and an out-of-band IDS. Then mark what each one can and cannot do when bad traffic appears.
- Use trigger-word flashcards: Put exam clues on one side and the likely answer on the other. “Investigate” suggests IDS. “Automatically block” suggests IPS.
- Focus on outcome: Ask what happens after detection. Does the tool alert someone, or does it stop the traffic itself?
- Separate detection technique from control type: Signature-based and anomaly-based analysis can show up in both IDS and IPS questions. The response behavior is what usually decides the answer.
A helpful analogy for test day is this: IDS works like a security camera and alarm. IPS works like a locked security gate with a guard who can shut it immediately. Both detect trouble. Only one is designed to intervene on the spot.
Common mistakes to avoid
Students preparing for Security+ and CISSP often miss questions for the same reasons:
-
Mixing up detection method and device role Signature-based detection does not automatically mean IDS. Anomaly-based detection does not automatically mean IPS.
-
Assuming prevention is always the better answer Automated blocking can create business risk in sensitive environments. Exams often reward the safer control when availability matters most.
-
Ignoring placement clues If the tool is inline, that points toward IPS behavior. If it is monitoring traffic out of band, that points toward IDS behavior.
-
Forgetting host-based versions HIDS, HIPS, NIDS, and NIPS follow the same core logic. The main difference is where they observe or control activity.
Your exam-day memory hook
Keep this three-part shortcut in mind:
- IDS = see and say
- IPS = see and stop
- Hybrid = see, stop, and support investigation
To go deeper and accelerate your career with Security+ prep, spend extra time on scenario questions instead of memorizing definitions in isolation. This topic rewards candidates who can identify the business need, spot the action word in the prompt, and choose the control that fits the situation.
MindMesh Academy helps certification candidates build that kind of exam judgment, not just memorize definitions. If you’re studying for Security+, CISSP, CCNA, or another IT certification, MindMesh Academy offers structured prep designed to help you understand the concepts well enough to apply them under exam pressure.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 18 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.