Puppet vs Ansible: Which Tool Wins in 2026 (puppet vs ansible)
Puppet vs Ansible: Which Tool Wins in 2026? A MindMesh Academy Analysis
IT professionals managing modern infrastructure must choose between Puppet and Ansible. This selection involves more than software; it defines a system management philosophy. The decision depends on whether your organization needs strict consistency and continuous state enforcement or prefers operational speed and fast, ad-hoc automation. MindMesh Academy knows that proficiency in these tools helps candidates prepare for the AWS Certified DevOps Engineer - Professional, Azure DevOps Engineer (AZ-400), and foundational ITIL certifications. Mastering these platforms ensures you are well-prepared for technical assessments and real-world deployment scenarios across various private and public cloud environments.
Puppet vs. Ansible: A Quick Decision Guide for IT Professionals
Selecting between these two automation platforms requires a clear understanding of their architectural differences and how these designs affect daily operations. Neither tool is universally superior; they are built to succeed in different environments. This distinction is a recurring theme in professional certification scenarios and practical systems engineering.
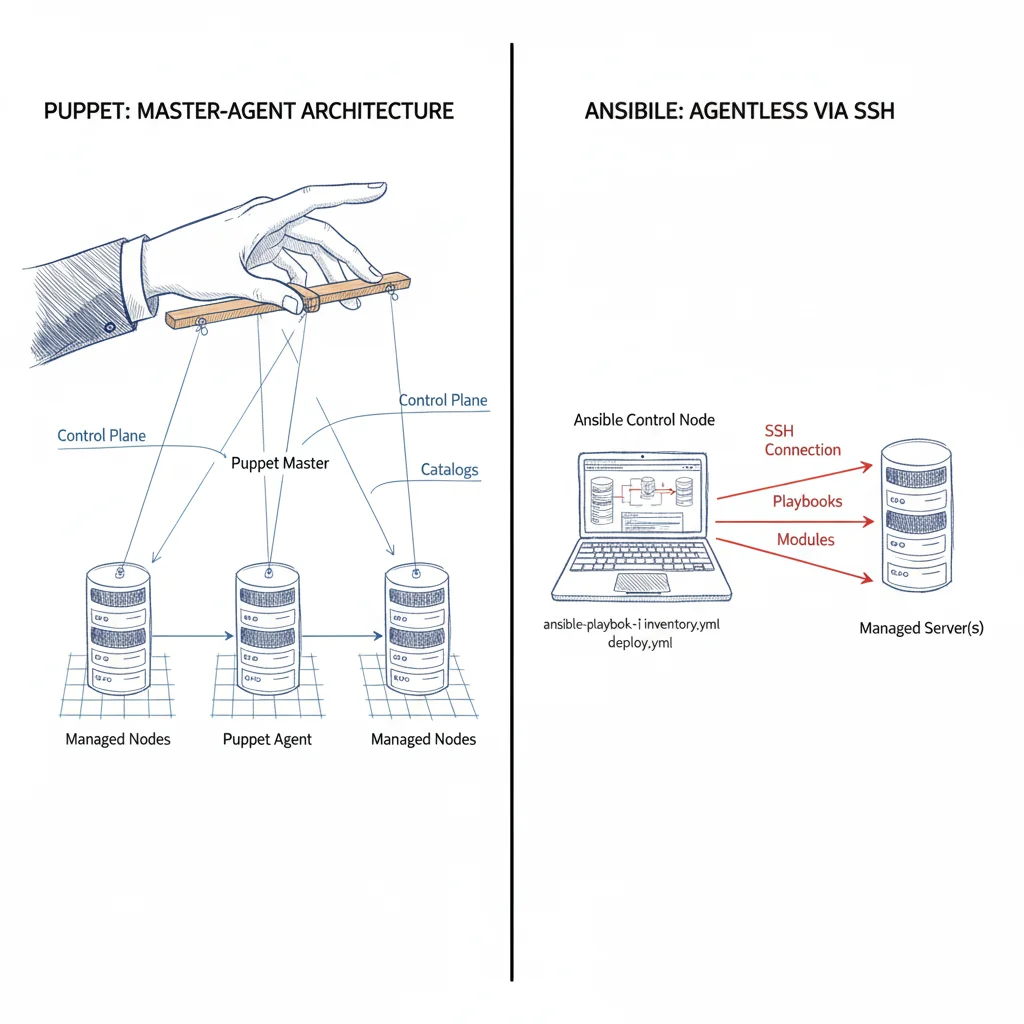
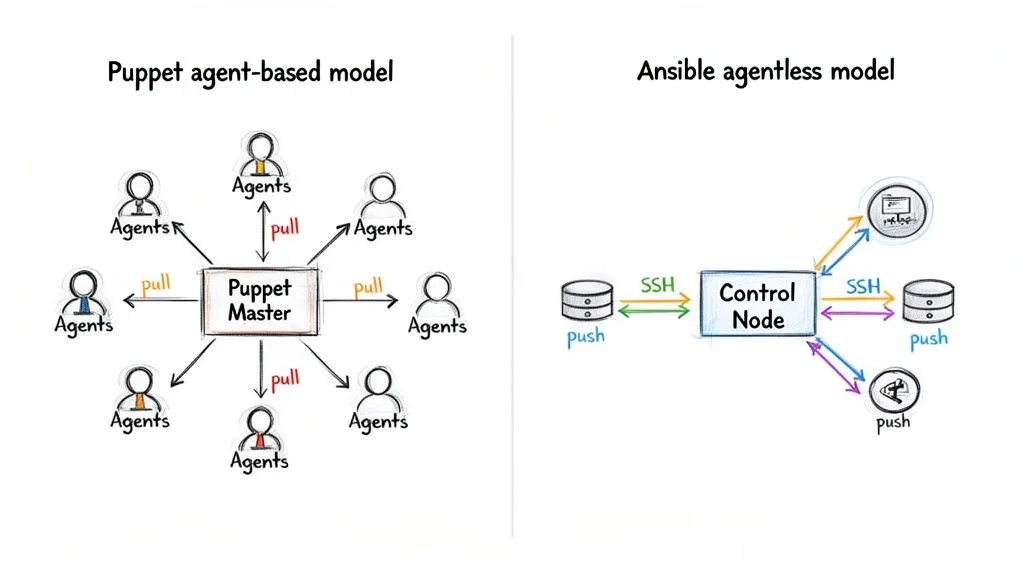
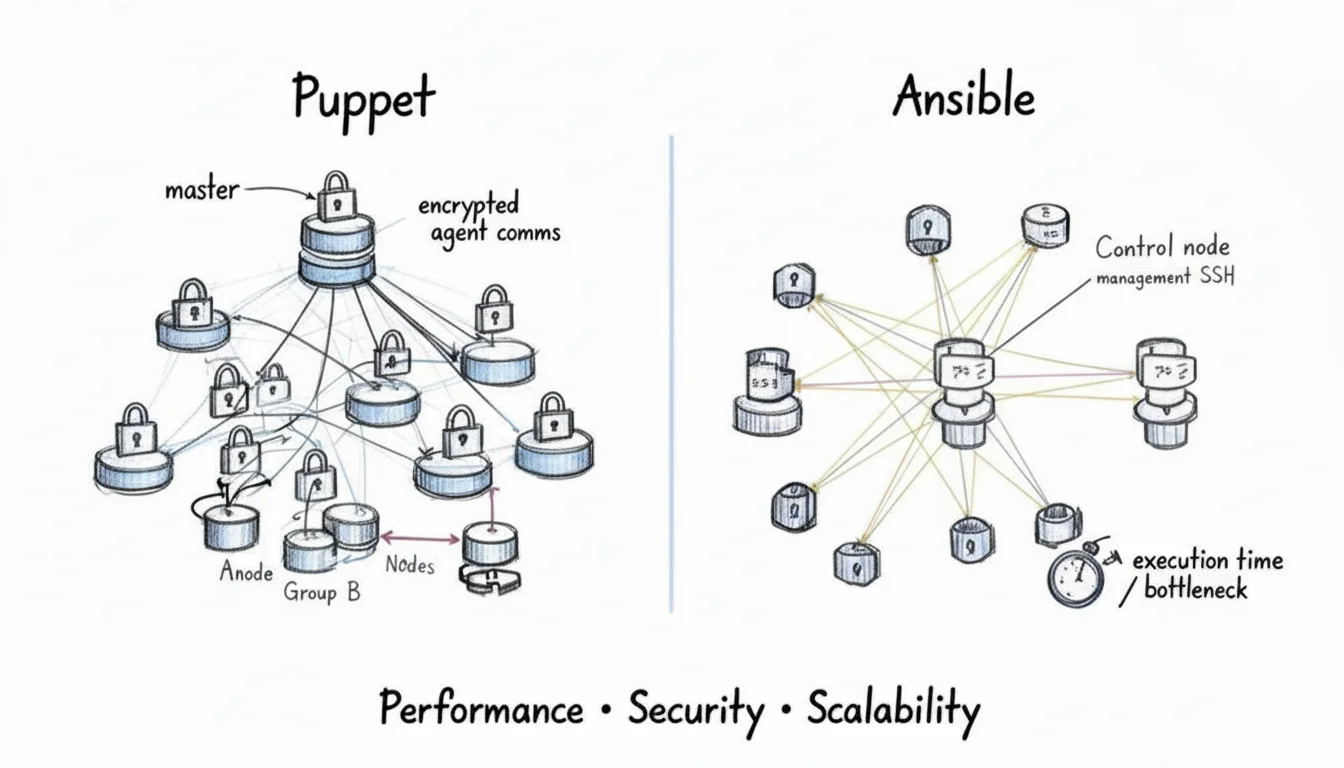
Puppet relies on a traditional client-server, or agent-based, architecture. You install a lightweight agent on every managed machine, known as a node. These agents check in with a central server, called the Puppet master, at regular intervals. The agent pulls down the configuration defined for that node and forces the machine's state to match the master's instructions. If any configuration drift occurs—such as a user changing a setting manually—the agent automatically resets it to the correct state. This mechanism makes Puppet a reliable choice for enforcing consistency across thousands of servers. It is a preferred solution for complex environments governed by strict PCI DSS or SOX compliance standards where auditability and state enforcement are required.
In contrast, Ansible operates with an agentless, push-based model. It does not require permanent software on your target nodes. Instead, it uses standard protocols such as SSH for Linux and Unix systems or WinRM for Windows machines to run tasks. It pushes configurations directly from a designated control node to the target servers. This architecture makes the initial setup fast. It is highly effective for dynamic cloud environments where you need to provision servers, deploy applications, or execute one-off commands without the burden of managing and updating agents. This flexibility aligns with modern DevOps workflows that prioritize speed and ease of use.
High-Level Comparison: Puppet vs. Ansible
To give you an immediate overview, this table summarizes the core differences between the two tools. This serves as a starting point for identifying which tool aligns best with your team's operational needs and existing infrastructure. These categories highlight common focus areas for technical certification exams.
| Criterion | Puppet | Ansible |
|---|---|---|
| Architecture | Agent-based (pull model) | Agentless (push model) |
| Language | Puppet DSL (Ruby-based), YAML | YAML, Jinja2 |
| Primary Use Case | Enforcing long-term desired state, compliance | Ad-hoc tasks, application deployment, orchestration |
| Learning Curve | Steeper, requires DSL familiarity | Lower, YAML-based, human-readable |
| State Management | Stateful, declarative, model-driven | Largely stateless, procedural, task-based |
While both tools are powerful, their core design philosophies dictate their relative strengths. The choice usually comes down to whether your infrastructure requires a system that continuously enforces a specific "golden state" through a declarative approach or one that excels at executing tasks and deployments efficiently using a procedural approach.
The Market Trend: Simplicity Meets Agility
In the current DevOps environment, industry trends often favor tools that offer speed and simplicity. Ansible has seen major growth, reaching a 31.7% market share by 2026, while Puppet holds a 14.6% market share. This data illustrates the popularity of agentless automation. For many teams, removing the task of installing, configuring, and maintaining agents across every node provides a clear operational advantage. It allows teams to scale across diverse and changing environments more quickly. This shift shows a preference for tools that reduce friction during provisioning and deployment.
The decision tree below shows the primary choice path. If your organization relies on strict, continuous state enforcement and compliance—common in highly regulated industries—Puppet is specifically designed for that challenge. For a wider range of tasks that require speed and flexibility, Ansible's design usually provides a stronger advantage for the engineering team.
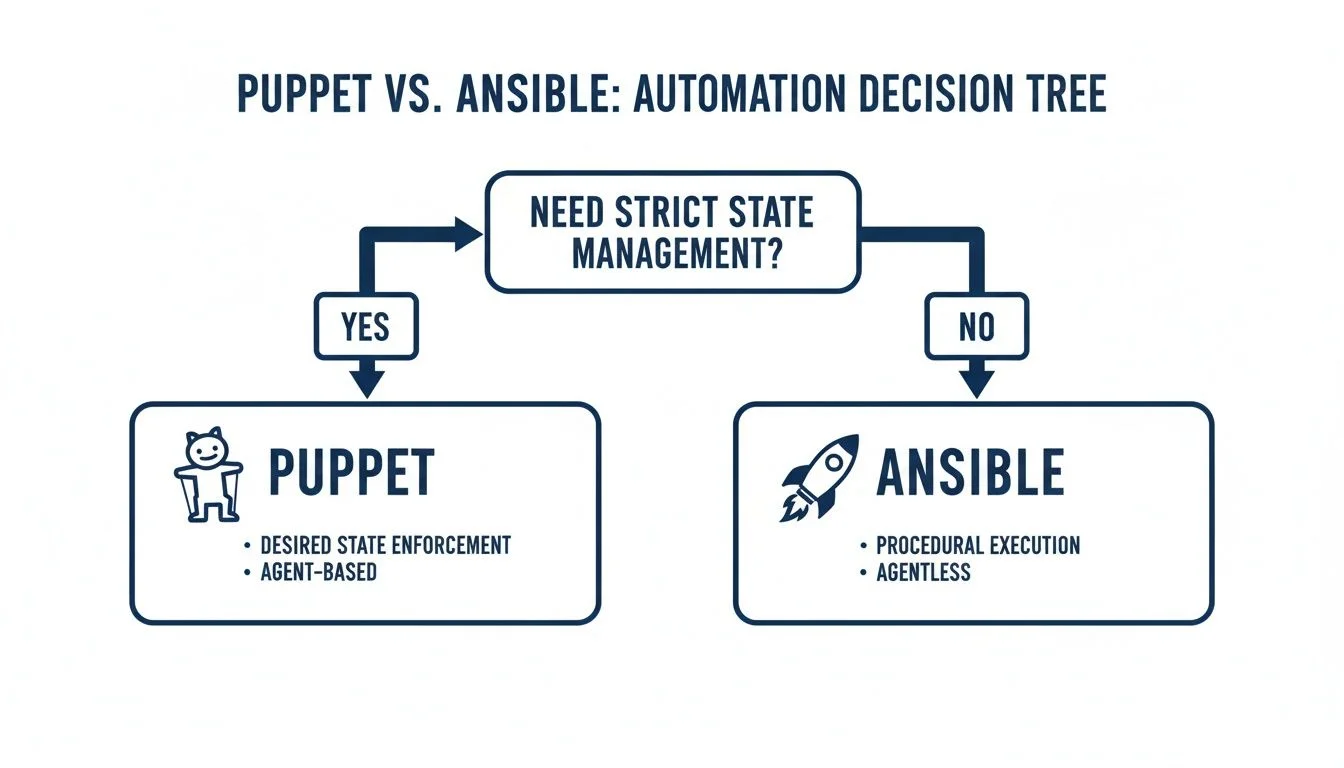
As illustrated, the critical decision point revolves around your specific need for strict, ongoing configuration state management. Once you define that requirement for your specific use case, the best tool for your environment typically becomes evident.
Understanding The Core Architectural Differences: Pull vs. Push
To understand the puppet vs ansible comparison, IT professionals must look beyond surface features to the architectural philosophies of each tool. These designs dictate how the software functions, where it performs best, and the trade-offs required for management. These concepts are essential for distributed systems, a topic often explored in certification programs like PMP and the AWS Certified Solutions Architect exams.
Puppet uses a client-server, agent-based design and a pull-oriented model. You configure a central Puppet master as the primary source of truth for the entire infrastructure. Every managed machine—a Puppet node—requires a lightweight Puppet agent to be installed locally to manage system resources.
Every 30 minutes (verify current defaults in Puppet documentation), agents connect to the master. The master compiles a "catalog"—a model-based map of the desired state that includes resources, classes, and dependencies. The agent pulls this catalog and compares it against the local system state, correcting any configuration drift. This reconciliation is a fundamental principle of declarative configuration management and ensures system idempotence, meaning repeated applications of the catalog result in the same state.
Puppet: A Centralized, State-Driven Model for Predictability
The master server functions as the central authority that defines the standards for your infrastructure through manifest files. Local agents act as supervisors, ensuring servers comply with those definitions. This persistent oversight is a major strength for maintaining long-term consistency and proving compliance in regulated industries where unauthorized changes must be caught quickly. It provides a reliable audit trail for changes across the server fleet.
Key characteristics of Puppet's model:
- Continuous Enforcement: Agents check in on a schedule to automatically correct drift and maintain a "golden state" without manual triggers.
- Centralized Control: All configuration logic stays on the master, providing a single point of reference for managing the entire infrastructure.
- Encrypted Communication: Master and agents use secure SSL/TLS for all traffic. This relies on a Public Key Infrastructure (PKI) to issue and verify certificates, a core topic in CompTIA Security+ and CISSP certifications.
This state-driven approach fits environments where predictability is essential, aligning with ITIL standards for change management and service operation.
Ansible: An Agentless, Push-Based Model for Agility
Ansible uses an agentless, push-based design. You do not need to install management software on the target machines. Instead, a central control node communicates with servers and network devices using an inventory file via SSH for Linux or WinRM for Windows.
When you run an Ansible playbook, the control node pushes tasks to target machines. It sends temporary Python modules that execute specific commands and are removed immediately after the task is done. This is a direct, imperative operation that leaves no permanent management software behind on the remote host.
The Puppet master functions like a central government passing laws and using local agents to ensure compliance. Ansible acts more like a field commander sending specific radio orders to troops in the field. Once the immediate task is done, the interaction ends and the troops wait for new instructions. There are no standing local orders; the focus is on the current mission. This approach is often better for rapid deployments and ad-hoc troubleshooting.
The agentless design simplifies the initial setup. You avoid the work of installing, configuring, and updating agent software across a large fleet of servers. This allows for faster onboarding of new systems and suits dynamic environments where provisioning new servers and running quick commands are frequent activities.
The Impact On Scalability And Enterprise Use
These architectures influence scalability. For large infrastructures with thousands of nodes, Puppet’s agent-based design has specific advantages. Since the agents handle the heavy execution work locally and in parallel, the master server focuses on compiling catalogs. This prevents the central server from becoming a bottleneck when many machines check in at once, though administrators must manage the "thundering herd" of simultaneous connections.
Founded in 2005 (verify company history on official site), Puppet has a mature suite of utilities like PuppetDB for data reporting and Bolt for orchestration. These are built to enforce repeatable states at a massive scale. For more detail, see Puppet's strengths in large environments on attuneops.io.
Reflection Prompt: How would the constant enforcement of a pull model help stability in a large environment compared to a push model? In what specific scenarios would the speed of Ansible still be the better choice for a systems engineer?
The choice in the puppet vs ansible comparison depends on a trade-off: do you need autonomous state enforcement or flexible task execution? This decision is central to the roles of a DevOps Architect or Platform Engineer, where choosing the right tool determines the long-term maintainability of the environment.
2. Language and Workflow: A Tale of Two Philosophies in Automation
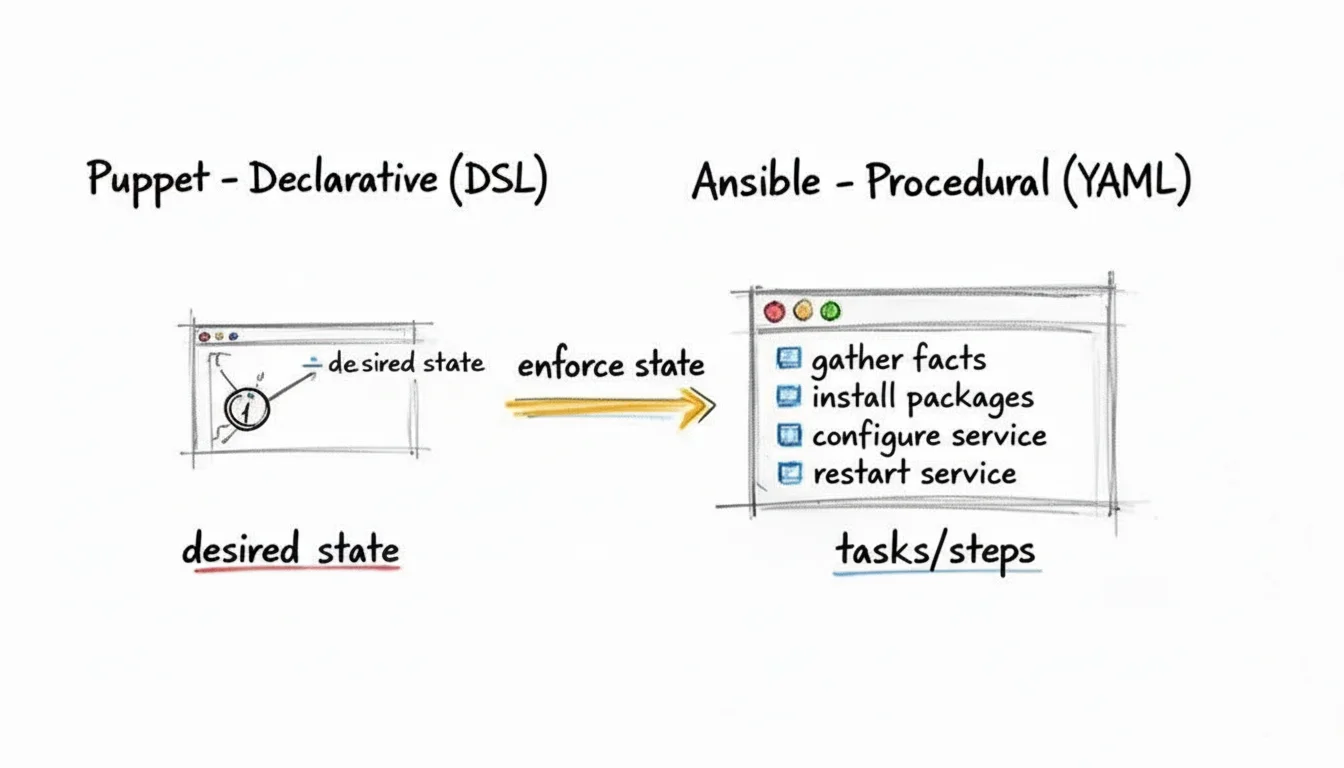
The architectural differences between Puppet and Ansible define how you write and manage your automation. These specific language and workflow choices come from two different philosophies. One relies on a structured, declarative approach to guarantee system state. The other prioritizes simplicity and procedural steps for fast task execution. Understanding these concepts is vital for anyone using Infrastructure as Code.
Puppet uses its own Puppet DSL (Domain Specific Language), which is a declarative language based on Ruby. When you write a Puppet manifest, you are not writing a script with a sequence of commands. Instead, you describe the final state of resources on a system. For example, you might state that a package must be installed or a service must be active. The Puppet agent then determines the best way to reach and maintain that state.
This model-driven approach is effective for enforcing consistency across an entire server fleet. You declare that a package must be installed, a service must be running, and a configuration file must have specific content. Puppet manages dependency resolution and execution order in the background to ensure these conditions are met. It checks the system regularly and corrects any changes that do not match the defined model to prevent configuration drift.
A Practical Comparison: Installing a Web Server
To clarify these differences, let's look at how each tool handles a common administrative task: installing the Nginx web server, ensuring the service is active, and deploying a basic homepage. This type of practical comparison helps when preparing for IT certifications by showing how declarative and imperative styles function in real scenarios.
Puppet's Declarative Manifest
With Puppet, you define resources and their desired states. Notice how the code describes the intended final system state rather than a list of steps.
# puppet/manifests/nginx.pp
class nginx {
# Declare that the 'nginx' package should be present
package { 'nginx':
ensure => 'installed',
}
# Declare that the 'nginx' service should be running and enabled
service { 'nginx':
ensure => 'running',
enable => true,
require => Package['nginx'], # Ensure the package is installed first
}
# Declare the state of the index file
file { '/var/www/html/index.html':
ensure => 'file',
content => '<h1>Welcome to our site, managed by Puppet!</h1>',
require => Package['nginx'], # Ensure Nginx is installed before placing the file
}
}
The require parameter sets up dependencies, but the manifest remains a model of the target state. Puppet interprets this model and enforces it to stop configuration drift and help with compliance. If you are new to the model-first concept, look at configuration management best practices. These provide a foundation for certifications like PMP or ITIL.
Ansible's Procedural Playbook
Ansible uses YAML for its procedural playbooks. An Ansible playbook is an ordered list of tasks that run in sequence on target machines. This is an imperative approach that is easy to read and follow.
# ansible/nginx-playbook.yml
---
- name: Install and configure Nginx web server
hosts: webservers
become: yes # Equivalent to 'sudo' for privilege escalation
tasks:
- name: Install the nginx package
ansible.builtin.package:
name: nginx
state: present
- name: Ensure the index.html file is in place
ansible.builtin.copy:
dest: /var/www/html/index.html
content: '<h1>Welcome to our site, managed by Ansible!</h1>'
- name: Ensure the nginx service is started and enabled
ansible.builtin.service:
name: nginx
state: started
enabled: yes
This playbook is logical from top to bottom. It runs tasks in the exact order you define. This makes it a good fit for application deployments, running one-off commands, and any workflow that follows a linear path. This is a common requirement in CI/CD pipelines.
The Workflow and Learning Curve Implications for Your Career
This fundamental split in philosophy has real consequences for daily operations and the learning curve. It affects how you grow as an IT professional.
Puppet’s DSL requires a mental shift to think about desired states rather than sequential commands. This creates a steeper learning curve at the start but pays off in large environments where continuous consistency is required. This model-driven discipline is useful for roles focused on enterprise architecture or compliance.
Ansible uses YAML and a procedural style, which makes the tool easy to learn for most users. Professionals who have experience with basic scripting can often understand an Ansible playbook after one look. This low barrier to entry explains why so many teams use it for fast orchestration and development projects, especially when they need to move quickly and do not require the continuous state enforcement that Puppet provides.
Key Takeaway:
- Puppet's workflow is designed for building a strong, self-healing model of your infrastructure. It is ideal for defining a "golden state" and making sure thousands of nodes do not change.
- Ansible's workflow excels at running tasks efficiently. This makes it a good tool for deploying new software versions, patching vulnerabilities, or setting up new server clusters for a project.
The choice between these two tools depends on what your organization values most. If you need strict, declarative control, Puppet is the better option. If you prefer procedural speed and high flexibility, Ansible is the right choice. Both skill sets are in high demand, but they often lead to different professional roles and environments.
Performance, Security, And Scalability Tradeoffs for Enterprise IT
When choosing between Puppet and Ansible, IT professionals must consider real-world trade-offs in performance, security, and scalability. These are not minor distinctions. They are fundamental architectural choices that shape the day-to-day operations and long-term viability of your infrastructure. Understanding these technical areas is essential for anyone aiming for advanced certifications such as the AWS Certified DevOps Engineer - Professional or the Azure DevOps Engineer (AZ-400). Each tool approaches the problem of configuration management from a different philosophy, leading to distinct results in high-pressure production environments.
Performance And Initial Setup Speed: Sprinter vs. Marathon Runner
When evaluating raw speed, you must look at two distinct metrics: the time required for initial setup and the efficiency of long-term execution. Ansible clearly leads in the first category. Its agentless architecture allows you to start configuring nodes almost immediately. All you need is standard SSH access for Linux or WinRM for Windows environments. You do not have to wait for a proprietary client to be packaged, distributed, and installed across your fleet.
This speed is a significant advantage for dynamic environments, rapid prototyping, and ad-hoc commands. If you need to patch a specific vulnerability across a hundred servers right now, Ansible can do it without preparation. It is also excellent for quickly spinning up test labs or ephemeral resources in a cloud environment. By removing the need for agent management, you eliminate a major friction point in adding new machines, which helps teams maintain agility within their CI/CD pipelines.
Puppet demands a greater upfront commitment. You must install the Puppet agent on every managed machine and establish a secure, certificate-based connection back to the Puppet master. This initial rollout requires careful planning, network configuration, and time. However, this effort represents an investment that pays dividends in sustained, long-term state management. Puppet is built to ensure that a server’s configuration does not drift over weeks or months, even if a local admin makes manual changes.
The Key Performance Trade-off: Ansible delivers immediate execution speed for specific, imperative tasks, making it a sprinter ideal for short bursts of activity. Puppet is more of a marathon runner. It is designed for consistent, background efficiency and continuous state enforcement over the long haul. This architectural design helps mitigate the "thundering herd" problem where a central server is overwhelmed by too many simultaneous push requests.
Once it is operational, Puppet’s pull-based model is remarkably efficient for large fleets. Agents check in with the master on a regular schedule, typically every 30 minutes. These check-ins are staggered, naturally distributing the configuration workload over time. This prevents the central server from being hammered by simultaneous connection requests, which is a common failure point when managing thousands of nodes with a push-based system. Puppet agents also use a compiled "catalog," which means the node knows exactly what its state should be without needing the master to guide every individual step of a task.
Security Models And Attack Surfaces: Centralized PKI vs. Distributed SSH/WinRM
The architectural differences between these tools create distinct security profiles. This is a critical consideration for any IT Security Specialist or DevOps Security Engineer. Neither tool is inherently less safe than the other, but they require different mindsets and maintenance practices.
Puppet uses a structured, self-contained security model based on a Public Key Infrastructure (PKI). Every agent receives a unique SSL certificate signed by the Puppet master's Certificate Authority (CA). All communication is encrypted over this dedicated channel. This creates a strong, centralized trust model. Because the Puppet master controls the certificates, it becomes a critical infrastructure component. You must secure it rigorously, as it holds the keys to the entire kingdom. This type of centralized security management is a major topic in the CISSP certification, where protecting the integrity of the configuration authority is vital.
Ansible’s security is built on existing, battle-tested protocols like SSH and WinRM. This is its greatest strength because most IT teams already know how to secure these protocols. However, it is also a significant responsibility. The security of your entire system depends on how well your team manages SSH keys, implements multi-factor authentication, and uses bastion hosts. If an attacker gains access to the Ansible control node or a shared private key, they can execute commands across every managed node in the inventory.
- Puppet Security: This model relies on a centralized, certificate-based trust system. Your priority is securing the Puppet master and its CA. It provides excellent identity verification because the master must sign every node’s certificate before the node can receive sensitive data.
- Ansible Security: This model depends on your existing SSH or WinRM security hygiene. Your team is responsible for managing keys, controlling access through sudo rules, and adhering to network policies. While there is no agent to attack, the management of administrative credentials across the network is a constant concern.
Scalability At The Enterprise Level: Handling Thousands of Nodes
When organizations grow to managing thousands or tens of thousands of nodes, scalability becomes the defining factor. Puppet was designed from its inception to handle this kind of scale. Its pull-based model and the ability to use "compile masters" allow it to distribute the heavy lifting of configuration management. If one Puppet master reaches its limit, you can add more compile masters behind a load balancer to handle the traffic from tens of thousands of agents. This ensures that the system remains responsive even as the fleet grows.
Ansible can manage large inventories, but its push-based model faces different constraints. The control node is limited by the number of concurrent SSH or WinRM connections it can maintain. Each connection consumes CPU and memory on the control node. While the Ansible Automation Platform (AAP) can distribute this work across multiple execution nodes, scaling to massive numbers—specifically beyond 500-1000 nodes per execution node—requires careful capacity planning. This is the kind of architectural challenge tested in PMP and Solutions Architect certifications, where resource allocation and bottleneck identification are key skills.
To help visualize how these tools perform in different scenarios, here is a breakdown of the situational trade-offs:
Situational Tradeoffs: Puppet vs Ansible for Scalability, Performance, and Security
| Dimension | Puppet Advantage | Ansible Advantage | Consideration for IT Professionals |
|---|---|---|---|
| Scalability | Massive Fleets (10,000+ nodes): The pull model and compile masters handle this scale efficiently, distributing load and ensuring state enforcement. | Dynamic Environments: The agentless design allows for rapid scale-up or scale-down without the overhead of managing agent certificates on short-lived nodes. | Puppet’s upfront work pays off at extreme scale for consistent state. Ansible requires more complex architecture (like AAP) to prevent push-model bottlenecks. |
| Performance | Sustained State Enforcement: Background agent runs provide low-impact configuration checks and auto-correction without needing manual triggers. | Time-to-First-Run: Unbeatable for immediate tasks. No agent means you can provision and configure a new server in seconds. | Do you need consistent background maintenance (Puppet) or high-speed execution for specific tasks (Ansible)? Your specific role often dictates the best choice. |
| Security | Self-Contained Trust: A dedicated PKI offers a strong, isolated security boundary for configuration traffic, which simplifies trust relationships. | Minimal Attack Surface: No permanently running agents on the managed nodes means fewer open ports and fewer processes for an attacker to exploit. | Puppet centralizes risk on the master server. Ansible’s security is tied to your key management and network access policies, creating a distributed responsibility. |
Reflection Prompt: Imagine you are designing the infrastructure for a highly regulated financial service that requires strict compliance auditing every 30 minutes. Which tool's security and scalability model would you choose to satisfy the auditors while maintaining a fleet of 5,000 servers? Connect your answer to the identity management principles found in the CISSP or AWS Certified DevOps Engineer - Professional curriculum.
The right choice depends on your specific operational pressures and long-term goals. A stable, large-scale enterprise might find the consistency and automated compliance of Puppet to be essential. Conversely, a fast-moving cloud-native startup might prefer the agility and low barrier to entry offered by Ansible. Both tools require you to follow solid Infrastructure as Code best practices for scalable DevOps to get the most out of your investment. These tradeoffs sit at the center of the puppet vs ansible debate. For anyone preparing for high-level certifications, understanding these architectural nuances is required. To see how these concepts appear on actual exams, review our detailed guide for the AWS Certified DevOps Engineer - Professional exam.
Choosing The Right Tool For Your Use Case: Scenarios for IT Professionals
High-level theory is useful, but the value of a tool appears when applied to actual business problems. The Puppet versus Ansible choice becomes clearer when you look at specific operational situations common in the tech industry. We can look at a few typical situations to show how their technical differences lead to practical advantages for different teams.
Scenario 1: The Startup Needing Fast Cloud Deployment
Consider a tech startup growing at a high rate. Their operations prioritize speed and constant iteration. The team needs to deploy applications to the cloud immediately. Their infrastructure changes frequently, with servers often created for short tests and then deleted hours later. In this environment, any delay in configuration adds up to lost time.
Recommendation: Choose Ansible. This is a practical decision for dynamic cloud-native environments.
Ansible uses an agentless, push-based model that works well for these fluid requirements. You do not spend time installing or managing agent software on temporary servers. A developer can write a simple YAML playbook to provision a virtual machine in AWS or Azure, deploy code, and run tests using one command. The tool is easy to learn, so the entire development team can contribute to infrastructure automation. This helps maintain a high speed in an agile DevOps setup where developers and operations staff share responsibilities.
Scenario 2: The Financial Institution Requiring Strict Compliance and Audit Trails
Next, look at a large financial institution. Their operations must follow strict regulations like PCI DSS, HIPAA, or SOX. They manage a large and mostly stable collection of servers. Every system must stay in a precise, auditable state at all times. Configuration drift—where a server's settings change over time—is a major regulatory and financial risk.
Recommendation: Puppet is the right choice here. It fits the needs of organizations focused on compliance and strict governance.
Puppet focuses on enforcing a desired state. Its agent-based model ensures every node checks in with the master server on a schedule. The agent reports its current state and automatically fixes any unauthorized changes or differences from the "golden state." This results in a self-healing system that stays in compliance without manual work.
For audit teams, this feature is very useful. Puppet provides detailed reporting, especially when you use PuppetDB to store historical data. This generates the exact audit trail needed to prove to regulators that every system is configured correctly and maintained in its approved state. The time spent learning Puppet’s domain-specific language (DSL) and setting up the master server is a small price to pay for long-term stability and high security. These technical goals align with the frameworks of ITIL Service Design and Service Operation.
Scenario 3: The Network Team Automating Device Configuration
Network engineers often manage hundreds of routers, switches, and firewalls from many different vendors. Their work is usually based on specific tasks. They might need to push out new Access Control Lists (ACLs), change VLAN settings, or update firmware across the entire network.
Recommendation: Ansible is built for network automation.
A major reason for this is that most network hardware cannot run third-party agents. This makes an agent-based tool impossible to use for these devices. Ansible avoids this problem by communicating over standard protocols like SSH, which almost every network device supports. The procedural, step-by-step workflow matches how network engineers think about and perform their work.
The Ansible community has also created a large collection of modules for vendors like Cisco, Juniper, and Arista. This allows network teams to use existing code to automate their hardware. For example, an engineer can update NTP settings across 500 switches in one day. This reduces the chance of human error and makes the network more efficient.
The Decision-Making Framework for IT Professionals
As these examples show, the choice is not about finding a tool that is better in every way. Instead, you must match the design of the tool to your team’s specific needs and business goals.
- If your priority is speed, flexibility, and managing multi-step tasks like application deployments in a changing environment, choose Ansible.
- If your priority is continuous compliance, long-term stability, and enforcing a specific state across a large, stable infrastructure, choose Puppet.
Think about the main goals of your business. Is it reaching the market quickly, meeting regulatory standards, or maintaining operational consistency? Once you identify these priorities, the choice between Puppet and Ansible becomes easier. Understanding these trade-offs is a vital skill for IT Leaders and Project Managers who make strategic technology decisions.
How Your Choice Impacts Your DevOps Career Path
Choosing between Puppet and Ansible is a strategic career move for IT professionals. The tool you master shapes the jobs you qualify for, the organizations that hire you, and the certifications that will advance your career.
Market demand dictates your professional trajectory. If you prefer cloud-native environments, startups, or teams building CI/CD pipelines, Ansible proficiency is a significant advantage. Its clear syntax and deployment speed are valued in roles such as Cloud Engineer, DevOps Engineer, or Site Reliability Engineer (SRE). Companies in these sectors often require tools that allow for rapid iteration and minimal configuration overhead.
Puppet expertise remains a strong asset in established enterprises, especially in finance, healthcare, government, and manufacturing. These organizations use Puppet's model-driven approach to enforce strict compliance, manage large legacy systems, and maintain clear audit trails. This makes Puppet skills useful for Systems Administrators, Platform Engineers, or Infrastructure Architects who manage long-lived server fleets.
Aligning Skills With Job Roles and Certifications
Hiring managers use tool proficiency to filter candidates based on specific infrastructure needs. A Systems Administrator or an engineer managing traditional IT infrastructure will find Puppet skills useful for maintaining a consistent state over long periods, often in line with ITIL standards. This approach ensures that server configurations do not drift from the baseline, which is a requirement for many security audits.
A DevOps Engineer focused on accelerating deployment pipelines and infrastructure provisioning in a cloud environment will find Ansible expertise is almost always required for roles like Azure DevOps Engineer or AWS DevOps Engineer. Knowing which tools are in demand for specialized roles like a Senior DevOps Security Engineer gives you a clear advantage when planning your professional development.
Mastering Ansible aligns you with agile, cloud-first companies that prioritize rapid deployments and dynamic infrastructure. Puppet knowledge makes you an asset in large enterprises that require rigorous compliance, control, and stability over complex, long-lived infrastructure.
This professional distinction is also reflected in industry certifications. The Red Hat Certified Engineer (EX294) credential (the current exam replacing EX407) validates your ability to automate tasks using Ansible. It focuses on practical skills such as writing playbooks, managing inventories, and securing sensitive data with Ansible Vault. These are the core competencies for modern automation roles. (Verify current pricing on the vendor site).
The Puppet Certified Professional certification confirms your ability to manage infrastructure as code using Puppet's declarative language. It covers the Puppet DSL, Hiera for data management, and building reusable modules. These skills are necessary for jobs demanding total state enforcement and granular control over every configuration item. (Verify current pricing on the vendor site).
- Choose Ansible for: Cloud automation, CI/CD pipeline engineering, and roles in agile startups. Red Hat certifications are frequently requested by companies using Red Hat technologies and cloud platforms to manage distributed systems.
- Choose Puppet for: Enterprise IT operations, compliance-heavy industries, and managing large-scale, stable infrastructure. The Puppet certification demonstrates proficiency in complex, declarative state management and long-term configuration stability.
Reflection Prompt: Given your career goals, which tool's learning curve and philosophy aligns with the roles and organizations you want to join? How might pursuing a specific certification, such as AZ-400 or Red Hat EX294, accelerate that path?
Acquiring skills in either tool is a smart move for your career. However, understanding both makes you versatile. For a broader view of how these tools integrate into DevOps, explore our study guide on Designing and Implementing Microsoft DevOps Solutions. Strategically choosing which tool to master first, based on your desired career path, is a decision that pays dividends.
Frequently Asked Questions About Puppet and Ansible for IT Professionals
When evaluating configuration management tools like Puppet and Ansible, certain questions arise frequently. Getting clear, practical answers to these FAQs is essential for making informed decisions for your projects, your team, and your professional growth.
Can You Use Puppet and Ansible Together?
You can certainly use them together, though the way teams do this has changed over time. Previously, a common workflow involved using Ansible for its speed during initial server provisioning and for running quick, ad-hoc commands across the fleet. Once the server reached an operational state, Puppet took over to manage ongoing configuration and enforce the desired state continuously. This specific approach of using Ansible for initial setup and Puppet for day-2 operations allowed organizations to use the strengths of both tools.
The distinction between these two platforms has decreased recently. Both products have broadened their feature sets. Puppet now provides task-running capabilities through Puppet Bolt, and it can even initiate existing Ansible playbooks from within the Puppet environment. Because of this overlap, many modern teams choose to standardize on one platform to reduce the complexity of their automation stack. However, a hybrid approach remains a practical choice for specialized use cases or while a team is in the middle of a migration.
Is Puppet Faster Than Ansible?
The answer to this question depends entirely on your specific goals and the environment you are managing.
-
Faster to Get Started / Ad-Hoc Tasks: Ansible is the clear leader for speed in these scenarios. Its agentless architecture and simple YAML syntax allow you to move from your first installation on a control node to executing an automation playbook in a matter of minutes. Since there is no software to install on the managed nodes—other than standard SSH or WinRM access—the setup time is minimal. This makes it the better choice for rapid provisioning or immediate, imperative tasks.
-
Faster at Scale / Sustained Enforcement: Puppet often performs better in large, complex environments that require constant state enforcement. Its pull-based agent architecture allows thousands of nodes to check in and verify their status independently and at different times. This prevents a central server from becoming a bottleneck. In contrast, a push-based tool like Ansible can face performance issues when trying to open thousands of simultaneous connections for a massive deployment. Puppet’s distributed model effectively avoids the "thundering herd" problem where a single controller becomes overwhelmed by too many tasks at once.
How Do They Handle Windows Environments?
Both Puppet and Ansible provide support for Windows, but they use different methods that align with their specific design philosophies. Understanding these methods is vital when you manage infrastructure with different operating systems.
Ansible maintains its agentless philosophy on Windows by using Windows Remote Management (WinRM). Since WinRM is the native Microsoft protocol for remote administration, Ansible uses the tools already built into the Windows operating system. You do not need to install extra software on the target Windows nodes, which keeps the setup simple and aligns with how many Windows administrators already operate.
Puppet uses a different method. It requires you to install a Puppet agent on every Windows machine you want to manage. This agent runs locally to enforce the desired state. This gives you the same model-driven, declarative management on Windows that Puppet provides for Linux. It is a consistent way to ensure your servers stay compliant over long periods.
When choosing between them for Windows, consider your primary objective. Ansible and WinRM work well for quick tasks and commands. Puppet and its agent-based model are better for maintaining a specific, compliant configuration over time, especially in environments where you need one solution to manage both Linux and Windows servers identically.
Which Has Better Community Support?
Both tools have large, active communities that provide significant support. You will find plenty of resources for either platform.
Ansible is a Red Hat project and has a very large user base. The community contributes to a massive collection of roles and modules found on Ansible Galaxy. If you encounter an automation challenge, you can almost always find a pre-made playbook or module that addresses it. This makes it easy to find answers and use the shared knowledge of other users to move projects forward quickly.
Puppet has a community that has been active for a long time and possesses deep technical knowledge. The Puppet Forge contains thousands of modules designed for enterprise use. Many of these modules are officially supported by Puppet Inc., while others are maintained by community members who test them for production use. This makes the Forge a reliable source for modules that can handle complex, high-stakes infrastructure tasks.
To help prepare for your next career move, you can view our CompTIA Network+ Study Guide.
At MindMesh Academy, we believe that mastering specific details of essential IT tools like Puppet and Ansible is what helps a professional advance. Our study guides and certification preparation materials provide the practical knowledge and strategy you need to be well-prepared for your exams and succeed in your daily work. Start your learning journey with us today!

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 18 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.