AWS CloudWatch vs CloudTrail A Complete Guide
AWS CloudWatch vs. CloudTrail: A Complete Guide for IT Professionals
IT professionals working with AWS often find the distinction between CloudWatch vs. CloudTrail confusing. These services are fundamental building blocks of the cloud platform. Understanding them is vital for passing AWS certification exams and creating stable, secure architectures.
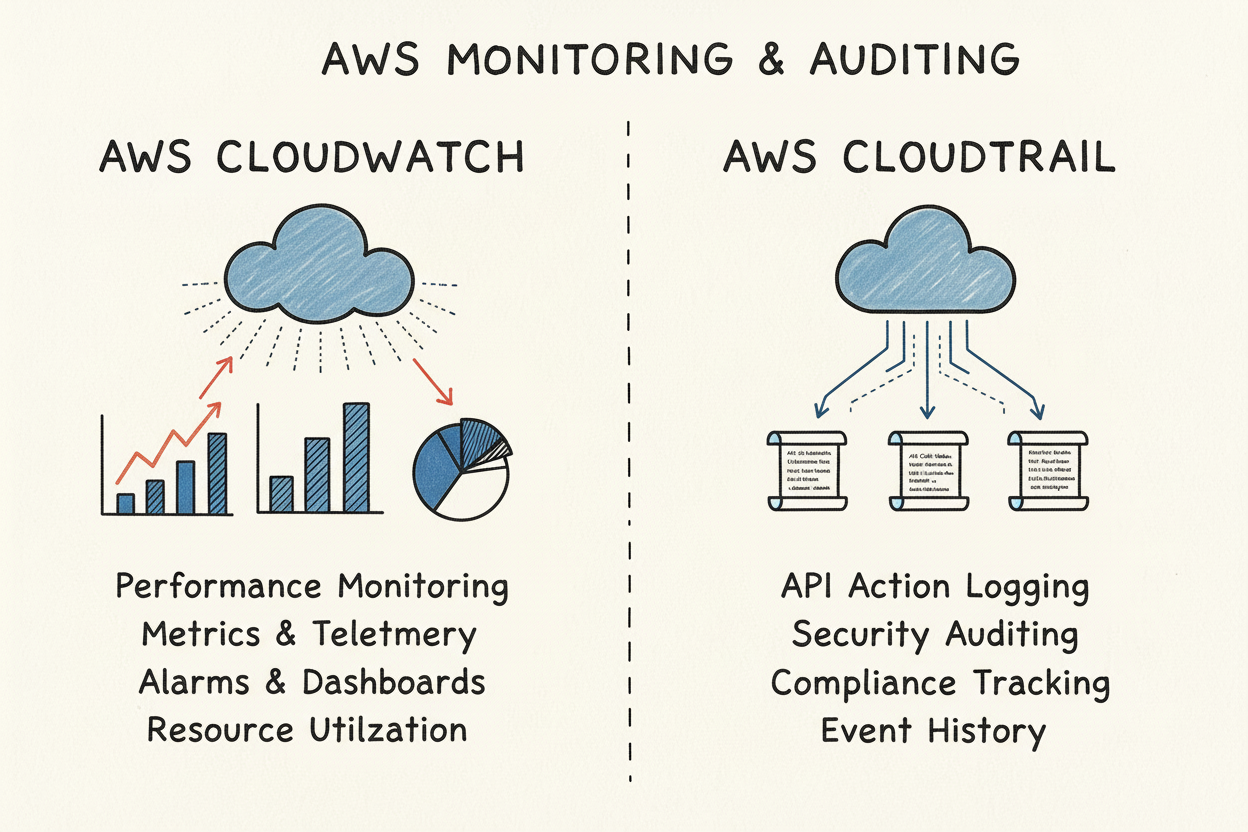
Compare your cloud environment to a high-performance vehicle. CloudWatch acts like a dashboard. It shows real-time metrics such as CPU use, network throughput, and how fast applications respond. It tracks how your system performs at any given moment. CloudTrail functions as the vehicle's black box recorder. It logs every action, every turn, and every stop. It documents who performed an action, what they did, and when it happened within your AWS account.
CloudWatch focuses on performance monitoring and observability. It tracks the health of applications and infrastructure. This tool helps you answer urgent operational questions. For instance, you might ask if an EC2 instance's CPU usage is too high. You might need to know why application response times are spiking. It provides the data needed to keep systems running smoothly and provides alerts when things go wrong.
CloudTrail handles security auditing, governance, and compliance. It records nearly every API call in an AWS account. This creates a history of actions taken by users, roles, or services. It is the primary tool for security forensics and change management. It helps identify who modified a security group or who deleted an S3 bucket. Without these logs, investigating an unauthorized change becomes nearly impossible. It ensures your account remains compliant with various internal and external regulations.
To summarize their core functions:
- CloudWatch monitors the state and performance of your resources.
- CloudTrail records the actions and changes made to your resources.
This division of labor reflects how AWS grew over the last decade. CloudWatch launched in 2009. At the time, developers needed better visibility into operational metrics to manage their workloads. CloudTrail arrived later in 2013. It was built specifically to meet the demand for security and auditing through API logging. Both services have evolved significantly since their release, but their primary purposes remain distinct in a modern architecture.
Knowing how these services work together is necessary for AWS exams. For more details on their roles within the security framework, see our guide to monitoring and logging.
CloudWatch vs. CloudTrail: At a Glance
This table compares the core purpose and function of each service. This distinction appears frequently in AWS certification exams.
| Aspect | AWS CloudWatch | AWS CloudTrail |
|---|---|---|
| Primary Purpose | Performance monitoring, operational health, and resource optimization. | Security auditing, governance, compliance, and change management tracking. |
| Data Collected | Metrics (e.g., CPU utilization, network I/O), application/system logs, traces, and events for operational insights. | API call history, user activity, and resource configuration changes. |
| Key Question Answered | "What is the current health and performance of my system?" (The what and how of operations) | "Who performed what action, when, and from where in my account?" (The who, what, when, and where of changes) |
| Common Use Cases | Application Performance Monitoring (APM), infrastructure health checks, auto-scaling triggers, operational alarms, and dashboarding. | Security incident investigation, compliance reporting (e.g., HIPAA, PCI DSS), change management audits, and forensic analysis. |
This overview outlines their specific roles.
Key Takeaway for Certification Exams: Remember the difference this way: CloudWatch provides performance and operational data. It covers the 'what' and 'how' of system health. CloudTrail focuses on activity and audit data. It covers the 'who' and 'when' of changes. A well-architected solution requires both to ensure security and uptime.
Learning this fundamental distinction is the first step toward building a secure cloud. It sets the stage for more advanced monitoring and governance strategies.
Comparing Critical Features: Monitoring and Auditing in AWS
AWS CloudWatch and CloudTrail provide distinct views of your cloud environment. While both services offer visibility into your infrastructure, they use different mechanisms for data collection, monitoring, and alerting. CloudWatch is designed to help you understand the health and performance of your applications and resources. CloudTrail is built to provide a history of API calls and user activity for security and compliance. Understanding these differences is necessary for passing the AWS Certified Cloud Practitioner (CLF-C02) or the AWS Certified Security - Specialty (SCS-C03) exams (verify current exam codes on the vendor site).
The primary difference lies in the type of data each service collects. CloudWatch functions as a performance monitoring tool. It tracks metrics, which are discrete, time-stamped data points such as CPU utilization, network I/O, API latency, and disk activity. It also aggregates logs from applications and operating systems to provide a view of how systems behave during execution. This helps you identify if a server is overloaded or if an application is running slowly.
CloudTrail takes a different approach by recording API events. Every action taken in your AWS account—whether it happens through the AWS Management Console, the Command Line Interface (CLI), or an AWS SDK—is saved as a log event. This creates a permanent audit trail for your account. It tells you exactly who made a change, what resource was affected, when the change happened, and the IP address used for the request. If a security group is modified or an S3 bucket is deleted, CloudTrail provides the evidence needed to investigate the change.
Data Collection and Granularity: What and How Quickly?
CloudWatch is built for high-frequency data collection to support operational responsiveness. Standard EC2 monitoring generates metrics every five minutes (verify current frequency on AWS documentation). If you require more immediate insights, you can enable detailed monitoring to collect data every one minute (verify current frequency on AWS documentation). This level of granularity is vital for detecting performance anomalies quickly and triggering automated responses like auto-scaling. Many AWS Solutions Architect exam questions focus on using these high-frequency metrics to optimize resource costs and application availability.
CloudTrail priorities the completeness and accuracy of its records over delivery speed. Typically, CloudTrail delivers an event to your Amazon S3 bucket within approximately 15 minutes of the API call (verify current delivery times on AWS documentation). While this is not as fast as CloudWatch metrics, it is sufficient for security forensics and compliance audits. In these scenarios, having a comprehensive and unchangeable record is more important than sub-minute delivery times. You can see how these logs are organized by reviewing how AWS CloudTrail log events are structured.
Reflection Point: Imagine a situation where a sudden spike in traffic requires immediate auto-scaling to prevent a website crash. In this scenario, CloudWatch’s one-minute granularity is much more useful than CloudTrail’s event logs. High-frequency metrics allow the system to scale out before performance degrades for the end users. This logic is a common theme in AWS Certified DevOps Engineer certification scenarios.
CloudWatch provides a continuous stream of performance telemetry that shows how your systems are running over time. CloudTrail provides a discrete, event-based record that shows what changes were made to your environment. Using both services together allows you to see that a performance drop occurred and then identify if a specific configuration change caused it.
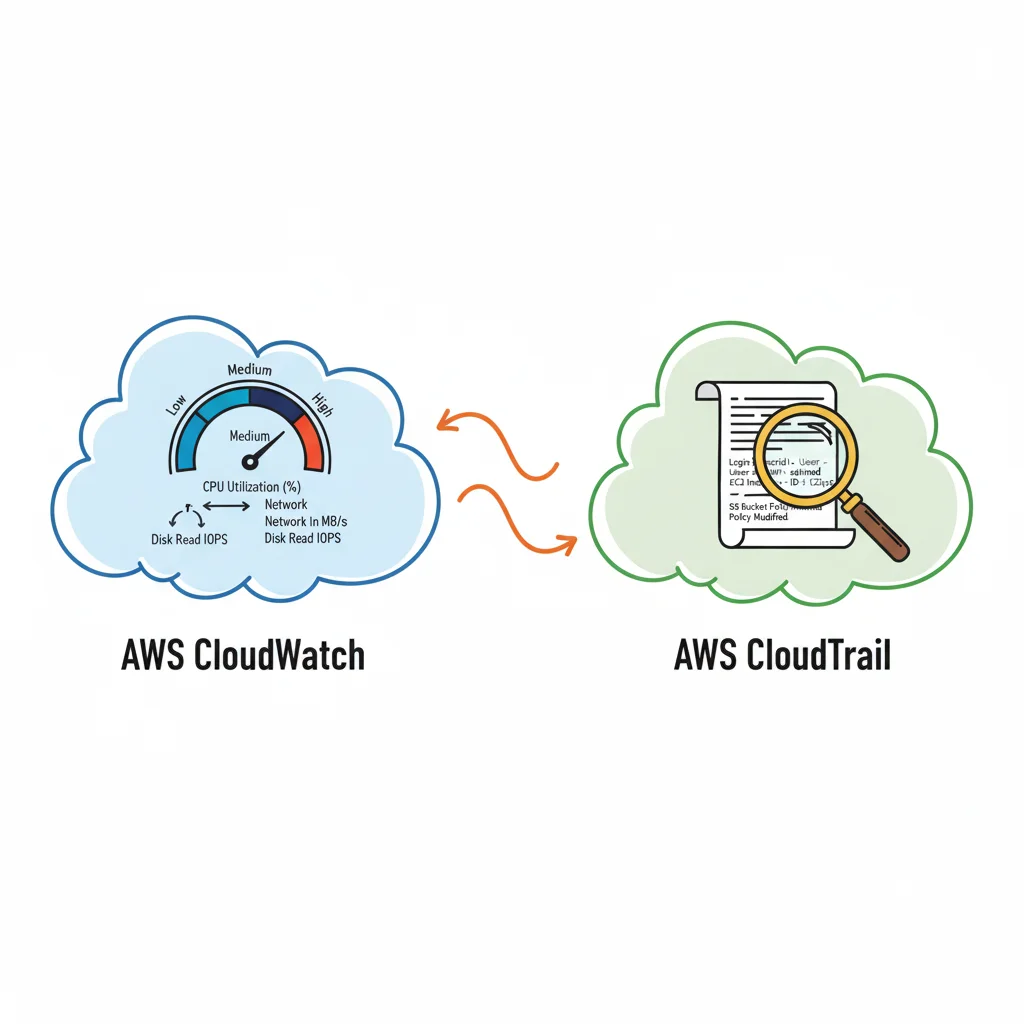
 Caption: This infographic illustrates the fundamental difference: CloudWatch aggregates performance data, while CloudTrail captures individual API actions for auditing and accountability.
Caption: This infographic illustrates the fundamental difference: CloudWatch aggregates performance data, while CloudTrail captures individual API actions for auditing and accountability.
Alerting Mechanisms and Triggers: Proactive vs. Reactive
The way these services handle alerts depends on their data types. CloudWatch Alarms are primarily driven by metrics. You define a threshold for a specific metric, such as "CPU Utilization greater than 80%" over a specific period. If the metric stays above that limit, the alarm moves into an "ALARM" state. This state change can trigger an action, such as sending a notification through the Simple Notification Service (SNS) or starting an AWS Lambda script to remediate the issue.
- CloudWatch Alarm Example (Certification Context): An exam question might describe a server experiencing a network surge. If the
NetworkInmetric stays above a set threshold for three consecutive five-minute periods, it could indicate a DDoS attack. A CloudWatch Alarm can detect this pattern and alert your security team or automatically trigger a script to update your firewall rules.
CloudTrail alerts are event-driven and usually work through Amazon EventBridge. You create rules that look for specific patterns or attributes within the CloudTrail log data. This allows you to react to specific user actions rather than just performance changes.
- CloudTrail Alert Example (Certification Context): A security team might need to know if anyone deletes a policy on an S3 bucket containing sensitive financial data. You can set up an EventBridge rule to monitor CloudTrail for the
DeleteBucketPolicyAPI call. If that specific call is made, the rule triggers an immediate alert. This type of proactive security monitoring is a major topic in AWS Certified Security - Specialty (SCS-C03) exams (verify current exam code on the vendor site).
Data Retention and Long-Term Storage: Balancing Cost and Compliance
Retention policies for these services are designed to help you balance storage costs with regulatory requirements. CloudWatch keeps metric data for specific amounts of time based on the granularity of the data:
- One-minute data points are kept for 15 days (verify current retention on AWS documentation).
- Five-minute data points are kept for 63 days (verify current retention on AWS documentation).
- One-hour data points are kept for 455 days, which is approximately 15 months (verify current retention on AWS documentation).
CloudWatch Logs offers more flexible control over retention. You can configure policies to keep logs for as little as one day or store them indefinitely. This allows you to discard temporary application logs while keeping critical system logs for long-term troubleshooting.
CloudTrail automatically provides the last 90 days of management event history through the Event History view at no extra cost (verify current history limits on AWS documentation). For longer-term storage, you must configure a "trail" to deliver events as log files to an Amazon S3 bucket. Once the data is in S3, you can manage the retention policy through S3 Lifecycle rules. This is necessary for meeting compliance standards that often require audit data to be stored for seven years or more. This integration is a central component of AWS security and compliance certifications.
Putting Theory into Practice: Real-World Scenarios for AWS Professionals
Understanding the individual features of CloudWatch and CloudTrail is a necessary start, but technical mastery depends on applying this knowledge to practical problems. This application is also a primary focus of AWS certification exams. Translating technical specs into effective monitoring and security strategies is how IT professionals provide value to their organizations.
Certain situations require the performance-focused data of CloudWatch. Other situations require the forensic history provided by CloudTrail. Most often, the clearest insights and most reliable solutions come from using both services together. This provides a complete account of the health and activity within an AWS environment.
When to Lean on CloudWatch: Operational Excellence
CloudWatch functions as the operational pulse monitor for your AWS resources. Its primary job is providing the real-time data needed to maintain the performance and efficiency of applications and infrastructure. Its strength is immediate health monitoring and automated response to changing conditions.
Consider these scenarios where CloudWatch is the correct tool:
- Application Performance Monitoring (APM) and Troubleshooting: An e-commerce application experiences a slowdown during a high-traffic sale. Using CloudWatch, you can examine metrics such as Application Load Balancer (ALB) latency, EC2
CPUUtilization, RDS database connections, and custom application metrics. If the data shows a spike inDatabaseConnectionsor highReadIOPS, the operations team can identify the database as the bottleneck. This allows them to resolve the issue in minutes by scaling the instance or optimizing queries. - Proactive Infrastructure Scaling with Auto Scaling: A media streaming service faces unpredictable spikes in viewership. To handle this, they set a CloudWatch Alarm on the average
CPUUtilizationof their EC2 fleet. When the average CPU exceeds 70% for five consecutive minutes, the alarm triggers an AWS Auto Scaling policy to launch new instances. This process ensures the service remains available and viewers have a consistent experience. This specific configuration is a common topic in Solutions Architect Professional exams. - Diagnosing Infrastructure Bottlenecks: When users report that a network feels slow, you can use CloudWatch to find the cause. By checking metrics like
NetworkInandNetworkOutfor specific instances, you can see if a network interface is reaching its limit. If an instance is consistently saturated, you might need to upgrade to a larger instance type or change the network configuration. For more details on these metrics, see our guide on Amazon CloudWatch for network metrics.
Where CloudTrail Shines: Security, Compliance, and Governance
CloudTrail provides a record of every action taken within an AWS account. This makes it the primary tool for security, compliance, and governance. It creates an audit log showing who performed an action, when they did it, and what the source IP address was. This information is vital for incident response and legal audits.
CloudTrail is the first point of reference in the following situations:
- Security Forensics and Incident Response: A developer finds that an S3 bucket containing customer data has been deleted. A security engineer uses CloudTrail to search for the
DeleteBucketAPI call. The log entry reveals the IAM user or role responsible, the source IP address, and the exact time of the deletion. This data allows for a fast response and helps identify whether the action was an accident or a security breach. This scenario often appears in AWS Security Specialty exam questions. - Compliance and Auditing: Organizations must often prove they follow standards like HIPAA, PCI DSS, or GDPR. These regulations require strict audit trails for data access. CloudTrail acts as the primary evidence source for these requirements. It logs every API call to services such as S3, DynamoDB, or IAM. Auditors use these records to verify that only authorized users accessed sensitive data.
- Tracking Down Unauthorized or Risky Changes: If an application goes down because of a configuration change made outside of a scheduled maintenance window, CloudTrail can find the cause. Reviewing the event history might show that someone modified a security group rule right before the outage started. Identifying the user who made the change helps the team fix the error and improve change management policies to prevent it from happening again.
Certification Focus: Exam questions often ask which service to use for specific tasks. If the goal is "root cause analysis of an outage caused by a configuration change," the answer is CloudTrail. If the goal is "monitoring application latency," the answer is CloudWatch. CloudWatch tells you if the system is healthy. CloudTrail tells you what people or services are doing to that system.
The Power of Synergy: A Combined Scenario for Comprehensive Insight
The most effective AWS strategies use CloudWatch and CloudTrail together. This integration connects operational performance issues to specific user actions. When you combine these services, you can perform a full root cause analysis that neither service can provide on its own.
This combined approach is best explained through a single incident:
- The Operational Anomaly (CloudWatch): A CloudWatch alarm triggers because the average API latency for a production application has tripled in the last 10 minutes. The team knows there is a performance problem, but they do not know why it started.
- The Security Investigation (CloudTrail): The operations team checks CloudTrail for any management events that occurred in that same 10-minute window. They look for events like
UpdateFunctionConfiguration,CreateDeployment, orAttachRolePolicy. - The Correlation and Discovery (Combined Insight): By matching the timestamps from CloudWatch with the logs in CloudTrail, the team sees that a developer deployed a new version of a Lambda function just before the latency increased.
- The Swift Resolution: Because the team correlated the performance data with the audit log, the root cause is obvious. They roll back the Lambda function to the previous version to fix the latency. The developer can then examine the new code in a development environment to find the bug.
This scenario shows why the comparison between these services is not about choosing one over the other. Instead, it is about using both to get a full picture of the environment. CloudWatch alerts you to the problem, and CloudTrail identifies the cause. Without this partnership, troubleshooting is much slower and relies on guesswork. This is a risk that production environments cannot afford, and it is a concept you must understand for AWS certification.
How They Fit into the Broader AWS Ecosystem: Designing Integrated Solutions
 Caption: This diagram visually represents how CloudWatch and CloudTrail integrate with other AWS services, demonstrating their foundational roles within the broader ecosystem for monitoring, security, and automation.
Caption: This diagram visually represents how CloudWatch and CloudTrail integrate with other AWS services, demonstrating their foundational roles within the broader ecosystem for monitoring, security, and automation.
AWS services do not function as isolated islands. The real strength of the platform lies in how these services communicate with one another. Success in building reliable systems—a topic central to professional certifications—requires a deep understanding of these interconnections. CloudWatch and CloudTrail demonstrate this perfectly. Each service acts as a distinct hub. CloudWatch serves as the primary operational trigger for your infrastructure. CloudTrail provides the audit records required for security and governance.
These integrations convert raw data into automated actions. CloudWatch links the internal performance of your resources to your management workflows. CloudTrail connects the identity, action, and timing of API calls to your security posture. Together, they support a stable and visible environment across your entire account.
CloudWatch as an Operational Automation Hub
CloudWatch is woven into the operational fabric of AWS. It serves as a central point for performance monitoring and automated responses. Because it collects metrics and logs from nearly every AWS service, it is positioned to trigger various automated workflows. This ensures your systems remain healthy and efficient.
Here are the most frequent integrations, which often appear in current AWS certification scenarios:
- AWS Auto Scaling: This represents a standard architectural pattern. A CloudWatch alarm tracks a specific metric, such as
CPUUtilization, for an EC2 instance or an Auto Scaling group. When the usage exceeds a set limit for a specific duration, the alarm moves into anALARMstate. This state change then prompts an Auto Scaling policy to launch more instances. If usage drops, it can trigger the removal of instances to control costs. This process is essential for anyone studying for the Solutions Architect exams. - Amazon SNS (Simple Notification Service): This integration provides an immediate alert system. When a metric crosses a threshold, the CloudWatch alarm sends a message to an SNS topic. You can configure this topic to notify staff via email or SMS. It can also push events into downstream applications or incident management systems. This ensures that the right people are informed about operational issues as they happen.
- AWS Lambda: This connection allows for highly specific custom automation. Instead of just sending an alert, a CloudWatch alarm can trigger a Lambda function to run custom code. This code might restart a frozen application, adjust a security group rule, or clean up temporary files. These proactive steps are vital for managing high-scale environments and are often tested in the current DevOps Engineer exam.
This tight integration makes CloudWatch more than a passive tool. It is an active engine that allows infrastructure to manage and heal itself.
Certification Insight: View CloudWatch as the "if" component in your automation logic. It continuously observes for a specific condition (if CPU usage is too high) and triggers a predefined response (then add another server). This pattern is required for building fault-tolerant and highly available architectures.
CloudTrail as a Foundational Security and Governance Feed
CloudTrail integrations focus on security, compliance, and governance. The service creates a permanent, unchangeable record of every action in your account. Other services consume this data to detect threats, analyze changes, and enforce corporate policies.
Its key integrations are built for auditing and are required knowledge for the AWS Security Specialty (SCS-C03) and Governance exams:
- Amazon S3 (Simple Storage Service): This is the most common destination for audit data. You can set up a trail to deliver every activity log to an S3 bucket for long-term storage. This provides a durable and highly available history of your account activity. Storing logs this way is a standard requirement for meeting compliance standards. It ensures that your data remains safe for years if an audit occurs.
- Amazon GuardDuty: This service provides threat detection by looking at patterns in your logs. It scans CloudTrail records to find signs of account takeover or compromised credentials. If someone attempts to launch instances in an unused region or makes unauthorized API calls, GuardDuty flags the activity. It uses these logs to provide a clearer picture of your security status without manual intervention.
- AWS Config: This service works with CloudTrail to track resource history. While CloudTrail records the person who initiated a change and when it happened, AWS Config captures the state of the resource itself. It shows you exactly how a security group or an S3 bucket configuration looked before and after an update. This combination is a powerful tool for troubleshooting and verifying that your resources meet organizational policies.
In the current version of the platform, CloudWatch has expanded its capability to pull metric data from nearly every service. This offers a total view across your entire stack. Newer features like Metric Streams allow real-time piping of this data to third-party platforms for hybrid or multi-cloud monitoring.
By combining CloudWatch alarm triggers with CloudTrail insights, you can create rapid, automated security responses. For example, you can disable a user's credentials the moment CloudTrail logs suspicious API activity. This direct flow of data makes CloudTrail the foundation of a proactive security strategy. The distinction in the AWS CloudWatch vs. CloudTrail comparison is clear: one drives operational automation, while the other fuels security and compliance analysis.
Decoding the Price Tags: CloudWatch vs. CloudTrail Costs for Smart Cloud Budgeting
Calculating the cost of AWS CloudWatch and CloudTrail is a vital skill for any IT professional managing a cloud budget. This subject appears frequently in the cost optimization sections of AWS certification exams. Both services are necessary for visibility, but their pricing models serve different technical goals. If you configure these tools with a clear strategy, you can find significant savings while still getting the technical insights you need.
CloudWatch uses a standard pay-as-you-go model. AWS provides a free tier to help you get started, but your bill grows based on the amount of data you send and which specific features you activate.
CloudTrail offers a more accessible starting point for auditing. AWS gives you one free management event trail in every region. For many users, this covers basic audit logging requirements. Costs mainly appear when you set up extra trails or start logging high-volume data events.
The CloudWatch Cost Breakdown: Key Drivers
Your CloudWatch invoice includes several different parts. The main things that drive up your bill are:
- Custom Metrics: You do not pay for standard metrics that AWS services send automatically, but you are charged for every custom metric you publish. This can become expensive if you track many application-level variables across hundreds of resources.
- Detailed Monitoring: Most AWS services send data at a 5-minute interval. If you turn on detailed monitoring for services like EC2, AWS tracks data at 1-minute intervals. This doubles the granularity but adds a per-instance fee. You should only use this for your most critical resources where performance timing is tight.
- Alarms: AWS charges a monthly fee for every alarm you create. High-resolution alarms that evaluate metrics at 10-second or 30-second intervals cost more than standard ones because they process more data points.
- API Requests: While these costs are usually low, they can grow if you use many CloudWatch dashboards or third-party integrations. Calls like
GetMetricDataandGetMetricWidgetImagecan add up if your team checks dashboards constantly or uses external monitoring tools. - Log Data Management: This is usually the biggest expense for CloudWatch users. AWS charges you to ingest data into CloudWatch Logs (per GB) and then charges you monthly to store that data (per GB-month). Users are often surprised by how quickly these costs grow if they do not manage their logs.
Pro-Tip for Certs and Real-World: Log ingestion is the most common cause of high CloudWatch bills. A single application with a "debug" level logging setting left on can generate terabytes of data and a massive bill. For your certification exams, remember that cost optimization usually involves setting smart retention dates and filtering your logs before they reach AWS.
CloudTrail Pricing and Long-Term Storage Considerations
CloudTrail has a simpler pricing model, but you need to think about long-term storage requirements. The first copy of management events delivered to S3 is free.
You will see charges for CloudTrail in these areas:
- Additional Trails: If you need more than one trail per region—perhaps for different compliance teams, separate departments, or sandbox environments—you pay for the extra events delivered.
- Data Events: This is the biggest cost driver for CloudTrail. These events track actions inside a resource, like
GetObjectorPutObjectin Amazon S3. They also track item-level actions in DynamoDB. Because these actions happen so often in busy accounts, AWS charges for them per million events. This adds up fast if you log everything in a high-traffic bucket. - S3 Storage: CloudTrail delivers logs to S3 for free, but you still pay the standard Amazon S3 rates to keep those files. If you keep logs for many years to meet legal or compliance rules, the storage bill will increase over time as your log history grows.
Real-World Strategies to Cut Costs Without Compromising Visibility
When you look at the AWS CloudWatch vs. CloudTrail cost balance, being proactive is the best way to save money. For CloudWatch, use standard 5-minute monitoring for your dev and test environments. Only use the faster 1-minute updates for production apps that need immediate attention during a failure. Be smart about your log retention. You do not need to keep every log group forever. Set a policy to delete old logs after 30 or 90 days unless you have a specific legal reason to keep them longer. You can also filter logs at the source so you only ingest the data you actually need.
With CloudTrail, be very specific about what you audit. Use event selectors to filter out the noise and only capture the API calls that matter for security or compliance. This is very important for data events. Instead of logging every S3 action in your account, pick the specific buckets or DynamoDB tables that are critical. These small changes reduce your data volume significantly while keeping your account secure. This approach follows the "Cost Optimization" pillar of the AWS Well-Architected Framework.
Making the Right Choice for Your AWS Strategy: A Unified Vision
When evaluating AWS CloudWatch vs. CloudTrail, the objective for IT professionals and those studying for AWS certifications is to use both services together to build a stable and observable cloud environment. These services are not competitors. They function like two specialized members of a team, each handling a distinct and specific role. CloudWatch serves as your real-time operational dashboard and first responder. Its primary mission involves monitoring the health, performance, and resource utilization of your systems. You rely on CloudWatch to maintain uptime, optimize how you use resources like CPU and memory, and respond to operational events. These events might include infrastructure bottlenecks or unexpected traffic surges that threaten your availability. It answers a specific question: "Is my application running optimally right now?"
CloudTrail serves a different purpose as your security auditor and compliance record-keeper. Its goal is to provide a complete and permanent record of every single action taken within an AWS account. This includes actions that occur via the AWS Management Console, Software Development Kits (SDKs), or command line tools. You use CloudTrail for security forensics, generating compliance reports for frameworks like HIPAA or PCI DSS, and enforcing governance policies across your organization. It answers a different but vital question: "Who changed what in my environment, and when did they do it?"
Embracing a Unified Monitoring and Auditing Approach
A professional AWS strategy requires using CloudWatch and CloudTrail together. CloudWatch offers operational metrics, while CloudTrail provides the security and audit context through detailed logs. Together, they form a visibility layer for operating a secure and compliant cloud environment. Consider an example where a CloudWatch alarm triggers because of a traffic spike on an EC2 instance. This alert provides the "what" and the "when" of the event. However, you need CloudTrail logs to identify the "who" and "why." The logs show whether a legitimate user started a new process, an application had a configuration error, or a malicious actor attempted unauthorized access. Using CloudWatch Logs to aggregate this data and CloudTrail to track the API calls creates a total picture of the incident.
Final Certification Insight: CloudWatch and CloudTrail are partners rather than competitors. A strong cloud strategy uses CloudWatch for proactive health monitoring and CloudTrail for accountability and security auditing. This combination protects and optimizes your AWS resources effectively across all service categories.
This partnership is essential as AWS services change over time. For example, AWS is currently modifying how certain user identity fields appear in CloudTrail logs for the IAM Identity Center. This update, effective July 14, 2025 (verify the exact implementation timeline on the AWS security blog), impacts how security teams track user activity across their various accounts. You can read the full details on these modifications to AWS CloudTrail event data. By using both tools from the start, you create a foundation that adapts to these updates, ensuring you maintain visibility and control over your AWS account. Integrating these logs into a central S3 bucket or using CloudTrail Lake further improves your ability to analyze long-term trends and security patterns.
Frequently Asked Questions for AWS CloudWatch vs. CloudTrail
IT professionals often have specific questions about how AWS CloudWatch and CloudTrail interact. Understanding these differences is key to managing cloud infrastructure or preparing for professional certifications. These services serve distinct roles, and knowing where they meet helps you build a more secure environment.
Some teams look for ways to simplify their toolset by using only one of these services. However, for anyone managing production workloads or studying for AWS exams, the answer is a firm no. Their functions are different. Trying to force one service to do the job of both will result in dangerous gaps in your security and operational oversight. You cannot monitor performance effectively with only an audit log, and you cannot audit security effectively with only performance metrics.
Can CloudWatch Replace CloudTrail for Auditing and Compliance?
No. CloudWatch tracks data points regarding API calls, such as how many calls were made, how many failed, or how long they took to process. However, it does not provide the specific, audit-level details that CloudTrail delivers for every action.
CloudTrail records the identity of the user making the request, the specific time of the action, the source IP address, and the exact parameters of the request. If you use only CloudWatch for auditing, you lose this context. You would be unable to perform security investigations or show compliance auditors exactly what happened during a security event. Forensic analysis requires a record of every individual action, and CloudTrail is the only AWS service that provides this level of detail. For any requirement that needs a permanent, unalterable record of account activity for legal or regulatory reasons, CloudTrail is the standard choice.
Do I Really Need to Use Both Services in a Production AWS Environment?
Yes. For any production environment on AWS, using both services is a requirement for a well-architected setup. If you use only one, you create a blind spot in either your performance monitoring or your security governance.
One way to look at this is by comparing the two to different monitoring tools. CloudWatch is like a health monitor that provides real-time data on how your systems are running. CloudTrail is like a security camera and an event log that records every action for auditing and accountability. A business needs both to stay safe and efficient.
Operating with only one service is like a pilot trying to fly a plane with a working airspeed indicator but no flight data recorder. You might know your current speed, but you have no record of where the plane has been, which crew member made changes to the autopilot, or how to investigate why an engine failed an hour ago. To troubleshoot effectively and maintain a safe environment, you need both the real-time data from CloudWatch and the historical record from CloudTrail.
How Do CloudWatch and CloudTrail Work Together to Enhance Security?
The real value of these services comes from how they work together to create automated responses. When you combine them, you can build systems that detect and stop threats in seconds. This is a central part of AWS security designs and is a frequent topic on the AWS Certified Security - Specialty (SCS-C03) exam (verify current exam details and pricing on the vendor site).
Here is a common example of how these services form an automated threat response:
- Suspicious Activity Recorded (CloudTrail): CloudTrail logs a sensitive API call. For example, a user might try to delete a production S3 bucket, disable an AWS Config rule, or even stop CloudTrail logging.
- Event Rule Match (Amazon EventBridge): This log entry is passed to Amazon EventBridge. A rule in EventBridge is set to watch for these specific unauthorized or high-risk actions.
- Alarm State Triggered (CloudWatch): The matching rule triggers a CloudWatch Alarm. This moves the alarm into an ALARM state instantly.
- Automated Remediation: The CloudWatch Alarm starts a pre-set action. This could involve sending an alert to the security team via SNS, starting a Lambda function to undo the change, or disabling the credentials of the user who performed the action.
This process creates a self-healing security system that responds to issues without waiting for a human to intervene.
Ready to master AWS and advance your career? MindMesh Academy provides study materials and learning techniques to help you pass your exams with confidence. Explore our detailed courses at AWS Security Specialty Practice Exams.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 18 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.