
Penetration Testing and Ethical Hacking: A 2026 Guide
Penetration Testing and Ethical Hacking: Understanding the Roles and Your Career Path
You might be reading this from one of three places. Perhaps you work in IT and hear that security is the next career move. You might be studying for a certification, trying to separate marketing language from actual practice. Or you're changing careers and want to know whether penetration testing and ethical hacking are real professions or just internet mythology with better branding.
This confusion is common. People use the terms loosely, job titles overlap, and the public image of hacking still swings between Hollywood fantasy and vague corporate jargon. It's simpler and more useful to understand the roles this way: Ethical hackers are security professionals who legally, safely, and with permission test whether systems can be broken into. Penetration testers are the specialists who run structured engagements to prove what an attacker could do.
If you are serious about this path, you need two things at once: technical clarity and a career map. Let's build both. MindMesh Academy aims to provide the clear, practical guidance you need to navigate this exciting field.
What Is Penetration Testing and Why It Matters
A company can appear secure on paper and still be exposed in practice. The firewall runs. Antivirus is installed. Staff assume updates are happening. Then come the odd lockouts, unexplained slowdowns, and alerts no one can fully explain. Leadership is left with the question that separates guesswork from security: Can an attacker get in, and what happens if they do?
Penetration testing answers that question by replacing assumptions with evidence.
A penetration test is an authorized security assessment where a professional attempts to exploit weaknesses in a target system under controlled conditions. The goal is not to cause damage. The goal is to show how a real attacker could gain access, move through the environment, or reach sensitive data before a criminal does.
Ethical hacking is the wider discipline around that work. It includes penetration testing, but it also covers broader security assessments, adversary simulation, and ways of examining how technology, people, and process failures create risk together.
A practical analogy helps. A penetration test works like hiring a skilled inspector to test whether your building's doors, windows, alarms, and maintenance routines hold up under pressure. Passing a checklist is one thing. Proving that a determined intruder cannot get through is another.
That difference matters because many breaches do not begin with exotic zero-day exploits. They begin with weaknesses an organization already owns but has not fixed. In 2024, Verizon reported that exploitation of vulnerabilities was one of the leading initial access paths. The report notes that vulnerability exploitation often involved known edge-device flaws, which explains why proactive testing remains a priority for security teams and executives, according to the 2024 Verizon Data Breach Investigations Report.
Penetration testing versus ethical hacking
This distinction confuses beginners because people use the terms loosely in job posts, course titles, and casual conversation. The easiest way to separate them is by scope and purpose.
- Penetration testing is a defined engagement with approved targets, a time window, a method, and a report that shows what was exploited and how to fix it.
- Ethical hacking is the broader practice of assessing security from an attacker's perspective across applications, networks, identities, cloud services, users, and business processes.
Another way to frame it is through the kind of question each one answers. Penetration testing asks, "Can this approved target be compromised, and what is the business impact?" Ethical hacking asks, "Where are the realistic paths an attacker could use across this environment, and how should we reduce that risk?"
If you are still sorting out the terminology, this explainer on what is in ethical hacking is a useful companion before you go deeper.
This distinction also matters for your career. A junior learner may start by practicing narrow pentest tasks such as scanning, enumeration, and web exploitation. A more experienced ethical hacker may connect those technical findings to business risk, cloud architecture, user behavior, and remediation strategy. Understanding that difference early helps you choose the right labs, certifications, and entry-level roles instead of treating every security job title as the same thing.
Organizations pay for this work because it answers hard, practical questions. Which weakness is exploitable? How far could an attacker go after the first foothold? Which fixes lower risk fastest? Those are the questions that turn curiosity about hacking into professional security work.
Navigating the Legal and Ethical Boundaries of Hacking
The same technical skill can make you either a trusted professional or a criminal defendant. The dividing line is not the tool. It’s permission, scope, and documentation.
A licensed building inspector and a burglar may both know how doors, locks, alarms, and weak entry points work. One has a contract and a defined assignment. The other does not. Penetration testing works the same way.
The three labels people hear first
Most beginners encounter these terms early, but they deserve plain definitions.
- White hat means authorized security work. The tester has written permission, defined objectives, and a business purpose.
- Grey hat usually refers to someone who acts without clear authorization but may claim good intentions. That's not a professional standard you want to build a career on.
- Black hat means malicious or unauthorized activity. Theft, damage, extortion, covert access, or illegal intrusion all fit here.
The industry hires white hats. Employers want people who can think like attackers without behaving like them.
Why scope matters so much
A professional pentester does not “test everything just in case.” They work inside a carefully defined boundary called the scope.
Scope definition is a critical and often overlooked part of penetration testing. Testers must operate within defined boundaries. Many organizations struggle to set those boundaries well, which can create false confidence if important systems, workflows, or attack paths are excluded, as discussed by the Cloud Security Alliance on ethical hacking and penetration testing.
That point matters more than many learners realize. If a client asks you to test a web app but excludes its API, identity provider, cloud storage, and admin portal, the final report may appear clean while the actual risk remains untouched.
What good rules of engagement usually include
Before any testing begins, professionals want a written agreement that answers practical questions like these:
- What systems are in scope: Specific applications, networks, cloud assets, user roles, and environments.
- What methods are allowed: For example, whether phishing, password spraying, or social engineering are permitted.
- When testing can happen: Some clients allow after-hours testing only because production systems are sensitive.
- Who to contact in an emergency: If a service crashes or a defensive team mistakes the test for a live attack, people need a direct line.
- What success looks like: Some tests aim to validate a security control. Others aim to prove data access or privilege escalation.
Your authorization letter matters as much as your technical skill. If you can't show permission, you're exposed.
Common legal mistakes beginners make
New learners often underestimate how easy it is to cross a line without meaning to.
Practicing on live targets
Curiosity is healthy. Unapproved testing on public websites, cloud accounts, login portals, or company systems is not. Use labs, training platforms, and intentionally vulnerable machines instead.
Going beyond the agreed target
A tester may discover a connected service, subdomain, or third-party integration that looks interesting. If it is not in scope, you stop and ask for clarification.
Confusing disclosure with permission
Finding a bug does not give you the right to exploit it further. Responsible behavior still requires authorization and defined limits.
The most professional sentence in offensive security is often, “This appears outside scope. Please confirm before I proceed.”
Ethics is part of the job, not a side note
Good ethical hackers protect confidentiality, minimize disruption, preserve evidence, and report truthfully. They do not chase drama. They do not inflate findings. They do not hide uncertainty behind jargon.
That mindset is what clients remember. It also shapes your reputation long before your tool skills reach an advanced level.
The Five Phases of a Professional Penetration Test
At 9:00 a.m., a client gives you a standard employee account, a test window, and a clear question: If an attacker starts here, what could they really reach?
That is the heart of a professional penetration test. It is a structured investigation with a beginning, a middle, and an end. For anyone trying to build a career in ethical hacking, these five phases matter for two reasons. They shape real client work, and they map directly to the skills employers expect in junior analyst, pentester, and security consultant roles.
Imagine a regional company asks a tester to assess an internet-facing customer portal and the connected internal pathways reachable from a standard employee account. The client wants to know how far a realistic attacker could go without starting with administrator access.
The engagement unfolds in five recognizable phases.
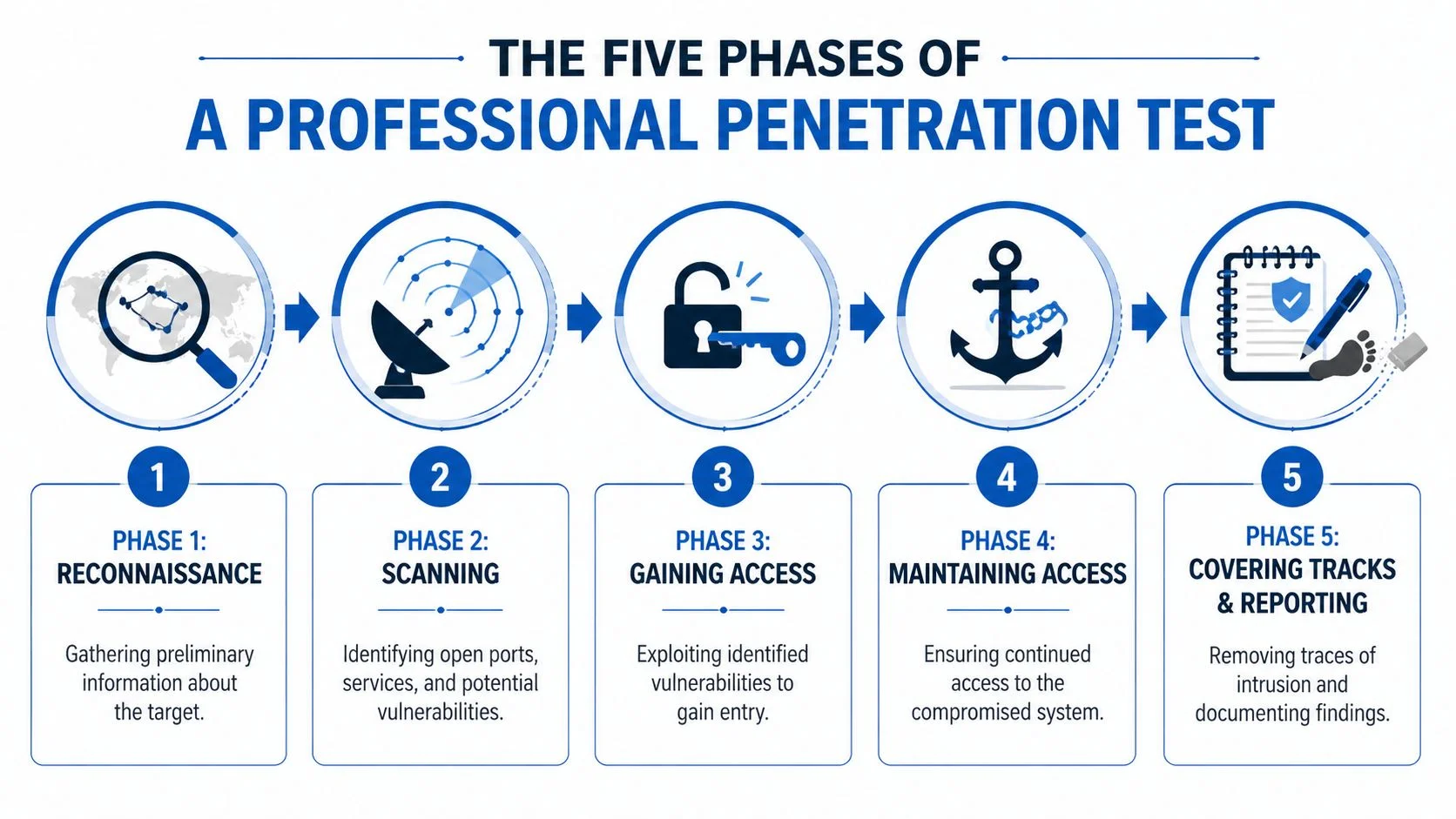
Phase one is reconnaissance
Reconnaissance is the research phase. A skilled tester studies the environment the way an investigator studies a scene before asking hard questions.
This means reviewing the target's public footprint, application structure, authentication flow, exposed technologies, naming patterns, and likely trust relationships. In an internal assessment, it also means understanding what a normal user can already access without doing anything suspicious.
New learners often underestimate this phase because it can look quiet. In practice, good recon saves hours of wasted effort. It helps you choose the attack paths that make sense instead of poking at every visible service.
What the tester is looking for
- Technology clues such as frameworks, cloud services, login methods, and admin interfaces.
- Trust relationships between applications, APIs, internal services, and identity systems.
- Human patterns such as naming conventions, exposed documents, or role descriptions that reveal how the organization operates.
This phase also has career value. Reconnaissance skills show up early in certifications and entry-level work because they teach observation, pattern recognition, and disciplined note-taking. If your long-term goal includes cloud testing, this same habit of mapping services and permissions also supports study for certifications such as the AWS Certified Security Specialty.
Phase two is scanning and enumeration
Now the tester starts checking what is reachable and responsive. Doors, windows, side entrances, and forgotten service accounts all matter.
Scanning and enumeration answer practical questions. Which ports are open? Which services disclose versions? Which pages return unusual errors? Which roles can see functions they should not have? Automation helps collect this data, but the tester still interprets what matters and what is just noise.
During this phase, testers often find ordinary weaknesses that create real business risk. Common examples include server misconfigurations, cross-site scripting, and broken access control, as noted in Zerothreat’s penetration testing statistics overview.
That point matters for beginners. Entry-level pentesters sometimes expect every assessment to involve rare exploits. Professional work is usually more grounded. Many serious findings begin with a simple mistake that nobody verified carefully.
A quick example makes that concrete. Suppose a customer portal exposes administrative actions through predictable requests, but the server fails to verify whether the logged-in user has the right role. The bug is easy to describe. The impact can still be severe.
Here is a plain-language model for this phase:
| Phase task | What it means in plain language |
|---|---|
| Enumeration | Finding what exists |
| Fingerprinting | Learning what technology a target is running |
| Validation | Checking whether a suspicious condition is truly exploitable |
Phase three is gaining access
This is the phase people usually picture first, but professionals treat it as a controlled proof exercise.
The tester takes the most credible weakness from the earlier phases and attempts exploitation within the agreed scope. That might mean abusing weak authorization logic, chaining a misconfiguration with exposed functionality, or showing how unsafe input handling leads to unauthorized actions.
The goal is evidence. If a standard user can read restricted records, reset another user's workflow, or gain higher privileges, the tester has shown the client a real problem they can verify and fix.
This phase is also where career growth starts to separate hobbyists from professionals. Junior testers learn how to prove impact safely. Stronger testers learn how to choose the least disruptive path that still demonstrates risk clearly.
Phase four is maintaining access
A real attacker rarely stops after the first foothold. They try to stay in place, move to connected systems, and reach something more valuable.
A professional pentester simulates that behavior carefully. The question is not how much disruption they can cause. The question is what becomes possible after initial compromise. Can they persist? Can they pivot to another system? Can they reach sensitive data or stronger privileges? Do the organization's logs and alerts show any of it?
Many organizations learn hard lessons here. They may have decent prevention controls but weak detection. A tester who can move undetected from one system to another often exposes problems in monitoring, alerting, and incident response.
A practical walkthrough helps here, and this short video is a useful overview:
Phase five is reporting and analysis
Reporting is where technical findings become work the client can act on.
A mature penetration test report does more than list bugs. It explains what was found, how it was validated, what business process or asset was exposed, and what the defenders should fix first. Security engineers need reproduction steps. Managers need prioritization. Leadership needs a clear statement of risk and likely impact.
A useful report usually includes
- Clear finding descriptions that explain what was wrong and why it mattered.
- Proof of impact showing what access or action was possible.
- Remediation guidance designed for developers, system owners, or infrastructure teams.
- Risk context describing what an attacker could do next if the issue remains unresolved.
This phase often determines how people remember your work. A tester who finds a serious issue but writes a vague report creates friction for everyone else. A tester who explains the issue clearly helps teams fix it faster, builds trust with clients, and shows the communication skills that hiring managers seek in consulting and in-house security roles.
That is why the five phases matter beyond the lab. They are not just the workflow of a test. They are the working habits behind a real penetration testing career.
The Ethical Hacker's Toolkit and Digital Proving Grounds
If the five phases are the workflow, the toolkit helps you move through it. No single tool does the whole job. Professionals carry categories of tools, much like a mechanic carries scanners, wrenches, meters, and specialty equipment.
Tools fit functions
Some names come up constantly because they solve recurring problems.
- Nmap helps map reachable services and supports early network understanding.
- Burp Suite sits between a browser and a web app so a tester can inspect and modify requests, making it central to web assessment work.
- Metasploit helps with exploit development, validation, and controlled proof-of-concept activity in environments where its use is appropriate.
- Wireshark helps analysts inspect traffic behavior and understand what systems are saying to each other.
- Nessus and Qualys are associated with vulnerability identification, especially when teams need broad visibility before deeper manual testing.
The important habit is not memorizing brands. It is learning why a tool belongs in a given phase. Burp Suite makes little sense if you do not understand web request flow. Nmap produces noise if you do not know what you are trying to discover.
Why professionals still need more than automation
Automation is fast and useful, but offensive security is not just about running scanners. Testers often need to verify logic flaws, authorization gaps, chaining opportunities, and cloud misconfigurations that require context.
That is why strong learners build layered skills:
- Networking knowledge to interpret what exposed services imply.
- Web fundamentals to understand sessions, input handling, authentication, and APIs.
- Scripting ability in languages like Python or Bash to automate repetitive tasks and parse results.
- Cloud awareness because modern engagements increasingly touch identity, storage, permissions, and service configuration.
If cloud security is part of your path, a focused guide for the AWS Certified Security Specialty can help you connect offensive testing concepts with defensive cloud design.
Your lab matters as much as your tools
The best place to practice is a controlled environment built for learning.
Use local virtual machines with platforms like VirtualBox or VMware. Work through intentionally vulnerable systems. Spend time on training platforms such as Hack The Box and TryHackMe. Treat them like digital gyms. You are there to build muscle memory, not to impress anyone.
A good home lab teaches habits that transfer to the job:
- Document what you do so you can explain your process later.
- Reset and repeat because repetition builds troubleshooting skill.
- Break your own assumptions by testing multiple approaches, not just the first one that works.
Great pentesters don't start by attacking random live systems. They spend a lot of time in safe labs learning how systems fail.
That is also where confidence becomes competence. You stop thinking in isolated tools and start thinking in workflows.
Forging Your Path with Certifications and Smart Learning
Most aspiring ethical hackers hit the same wall at some point. They open a job board, see a pile of acronyms, and wonder which certification counts. The answer depends on where you are now and what kind of role you want next.
Think of certifications as different licenses. Some prove you are safe on the road. Some show you can operate specialized equipment. Some tell employers you can handle pressure in difficult conditions.
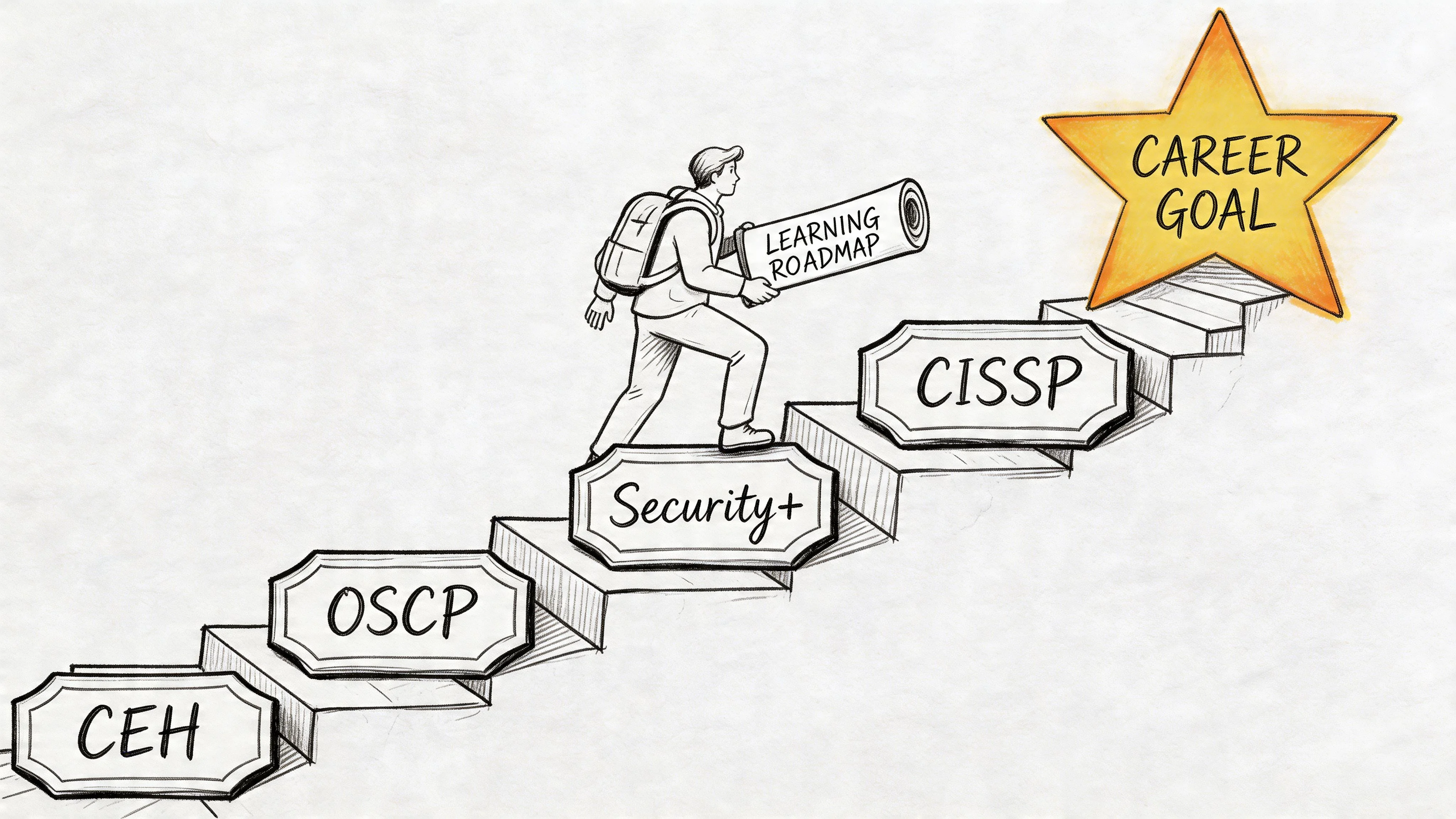
What each certification tends to signal
No certification replaces hands-on skill, but certifications help employers estimate your baseline.
| Certification | Focus Area | Skill Level | Best For |
|---|---|---|---|
| CompTIA Security+ | Security fundamentals, risk, networks, controls | Foundational | Beginners, career changers, junior IT professionals |
| CEH | Ethical hacking concepts, common tools, attack techniques | Early to intermediate | Learners who want broad offensive security exposure |
| OSCP | Practical exploitation, enumeration, persistence, reporting | Intermediate to advanced | Aspiring penetration testers who want hands-on credibility |
| CISSP | Security management, architecture, governance, risk | Advanced | Professionals moving toward leadership or broader security roles |
For many readers, CompTIA Security+ is the right first move because it builds the security language you will use everywhere else. It will not make you a pentester on its own, but it gives structure to concepts that otherwise feel scattered.
A sensible progression
You do not need to copy someone else's exact path, but most successful learners build in layers.
Start with fundamentals
If networking, operating systems, and authentication still feel shaky, start there. Offensive security punishes gaps in the basics. You cannot assess access control well if you do not understand how access control should work.
Add practical labs early
Do not wait until “after the exam” to touch tools. Lab work turns abstract ideas into memory. Even simple tasks, such as tracing requests in Burp Suite or mapping a small lab network in Nmap, teach more than passive reading.
Choose one offensive certification when you are ready
At some point, broad study has to become applied study. That is where a practical offensive certification can focus your effort. It gives you deadlines, a skills blueprint, and a way to prove commitment.
The best certification plan is one that matches your current level, not the one that looks most impressive in a social media bio.
How to study without burning out
Many learners fail because they study cybersecurity like a trivia contest. Penetration testing does not reward cramming. It rewards retention, pattern recognition, and repetition.
Use methods that support that reality:
- Spaced repetition helps you retain command syntax, protocol behavior, security models, and common vulnerability patterns over time.
- Adaptive review helps you spend more time on weak areas instead of rereading what you already know.
- Active recall forces you to explain a concept from memory, which is closer to what you will need in interviews and on the job.
- Lab journaling helps you remember what broke, what worked, and why.
A practical study week often looks better than an ambitious one. Two focused lab sessions, one review session, and one concept session will beat an exhausting plan you abandon after ten days.
What employers usually care about
Hiring managers do not just want certificates. They want signals of readiness.
Those signals often include:
- Evidence of hands-on practice through labs, writeups, personal projects, or capture-the-flag participation.
- Clear communication in reports, notes, or interview explanations.
- Consistency shown by steady learning, not random bursts of enthusiasm.
- Role fit between your certifications and the position you are applying for.
The shortest path into the field usually combines foundational knowledge, a visible practice habit, and one certification that matches your target role.
Building a Career in Ethical Hacking Roles and Realities
You finish your first lab, get a shell, and feel like you have crossed into professional territory. Then you look at actual security jobs and realize the day-to-day work involves client calls, testing notes, screenshots, retesting, and reports that busy engineers can act on. That surprise catches many beginners because ethical hacking as a career is much more than finding a way in.
The public stereotype focuses on hoodies, flashy exploits, and "breaking into stuff." Professional offensive security work looks closer to an investigation mixed with consulting. You test within scope, document what happened, explain why it matters, and help another team fix it. If you want a career, not just a hobby, that distinction matters early.
Some professionals work as dedicated penetration testers. They run scoped assessments, validate vulnerabilities, and write reports. Others work as security consultants, which usually means more client interaction, scoping discussions, remediation advice, and sometimes broader governance work. Some begin in SOC analyst or security analyst roles, where they learn how attacks appear from the defensive side before moving into offensive work. Others participate in bug bounty programs, though that path is less structured and harder to treat as a predictable entry route.
What the job actually rewards
Technical skill helps you get findings. Communication helps those findings matter.
A penetration tester creates value when a company can understand the risk, reproduce the issue, and fix it without confusion. As noted earlier, many findings never get remediated. That is why strong testers learn to write clearly, rank issues responsibly, and explain business impact in plain language. If your report reads like a puzzle, the organization may miss the point even if your technical work was solid.
A good way to picture the role is this: Finding a vulnerability is like diagnosing a fault in a machine. The organization still needs a usable repair note, the likely consequence of leaving it unfixed, and a practical order of operations.
Common roles and what they feel like
Penetration tester
This role fits people who enjoy structured assessments, methodical validation, and detailed documentation. A typical day may include testing windows, evidence capture, retesting, note review, and writing reports that another technical team can follow.
Security consultant
This path suits people who like technical work and also like conversations with clients. You may spend more time defining scope, explaining tradeoffs, prioritizing remediation, and helping stakeholders turn findings into an action plan.
Security analyst or SOC analyst
This is a strong starting point for learners who want to understand the defensive side first. You see alerts, incident patterns, attacker behavior, and operational workflows up close. That experience often makes later offensive work sharper because you already know what defenders notice and what they miss.
Security leadership track
Some professionals eventually move toward architecture, governance, or leadership roles. If that direction interests you, the CISSP (Certified Information Systems Security Professional) often becomes relevant later because it expands your view beyond testing alone.
The best offensive security professionals understand both sides. They know how to find weaknesses, and they know what defenders need in order to fix them.
How to present yourself without overselling
Early-career candidates often hurt themselves by trying to sound senior. Hiring managers can usually tell the difference between "I completed guided labs and wrote my own notes" and "I led enterprise adversary simulations" after one online course.
A stronger resume is specific. Name the lab environments you used, the kinds of vulnerabilities you practiced, the reports you wrote, and the tools you can explain under pressure. If you are struggling to present your experience clearly, tools like an AI resume builder can help you organize projects, labs, and certifications into language that employers can scan quickly. Just make sure the final version still sounds like you.
Most beginners do not expect this part
A large share of the work happens after access is gained. You explain findings to developers. You help infrastructure teams reproduce issues. You answer skeptical questions about severity, exploitability, and business impact. You translate security language into operational decisions.
That is not separate from the craft. It is part of becoming employable.
If you are trying to move from learner to professional, use each stage of your training to build toward a role. Web labs and report writing map well to junior penetration testing work. Blue-team exposure supports analyst and SOC roles. Broader security knowledge supports consulting and leadership paths later. That connection between technical practice, certifications, and job titles is what turns curiosity into a career plan.
Frequently Asked Questions About Ethical Hacking
Is ethical hacking actually legal?
Yes, but only when you have clear authorization.
That authorization should be written, specific, and tied to a defined scope. If you do not have documented permission to test a system, you should assume the activity is unauthorized. Curiosity is not a legal defense. A contract, scope, and rules of engagement are what make the work legitimate.
Do I need to know programming to become a penetration tester?
You do not need to start as a software engineer, but you do need some scripting ability.
A beginner can go far by learning how web requests work, how operating systems behave, and how to write or modify simple scripts. Python is helpful. Bash or PowerShell can be helpful too, depending on the environment. Over time, programming becomes more valuable because it helps you automate tasks, read proof-of-concept code, and understand application behavior more thoroughly.
Can I become an ethical hacker without a college degree?
Yes.
Many employers care more about proof of skill than about a specific academic path. Certifications, labs, home projects, technical writeups, and previous IT experience can all help. A degree can still be useful, especially in larger organizations, but it is not the only route into the field.
What is the hardest part of penetration testing?
For many people, it is not the tooling. It is the combination of constant learning and clear reporting.
The field changes fast. New technologies, cloud models, and app architectures create new attack surfaces. At the same time, clients need precise communication. You have to explain what you found, why it matters, and what should happen next. That combination is what makes the job challenging and rewarding.
Is penetration testing the same as vulnerability scanning?
No.
A vulnerability scanner identifies potential weaknesses. A penetration test evaluates whether those weaknesses can be exploited and what an attacker could accomplish afterward. Scanning is useful. Penetration testing adds validation, context, and attack-path thinking.
What is the best first step if I am brand new?
Start with fundamentals and a safe lab.
Learn networking basics, authentication, operating systems, and common web concepts. Then use legal practice environments such as local virtual machines or training platforms built for hands-on learning. Pair that with a foundational certification path if you want structure.
Do ethical hackers spend all day using hacking tools?
Not even close.
They spend time planning, documenting, validating findings, retesting fixes, communicating with stakeholders, and learning. Tools matter, but judgment matters more. A professional who understands systems well will outperform someone who only knows how to click through tool output.
How do I know if this career fits me?
You will probably like this field if you enjoy problem-solving, structured curiosity, and patient investigation.
People who do well in penetration testing usually like asking how things work, why they fail, and how small weaknesses connect into larger risks. If you prefer clear puzzles, evidence-based thinking, and continuous skill-building, you are looking in the right direction.
If you are ready to turn curiosity into a real study plan, MindMesh Academy is built for that next step. We help you prepare for certifications with structured study guides, evidence-based learning methods like spaced repetition, and a clearer path from fundamentals to job-ready security knowledge.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.