
8 Types of CISSP Exam Test Questions You Must Master in 2025
8 Types of CISSP Exam Test Questions You Must Master in 2025
The Certified Information Systems Security Professional (CISSP) exam is widely recognized as a pinnacle certification for IT security leaders. It demands more than just technical recall; it's a rigorous assessment of your ability to apply a managerial mindset to complex security challenges. Success hinges on your capacity to analyze intricate scenarios, prioritize business objectives, and integrate robust security controls effectively.
This guide from MindMesh Academy aims to move beyond simple memorization, targeting the core logic and strategic thinking required to excel. We will dissect the most common types of CISSP exam test questions you are guaranteed to encounter, providing a strategic blueprint for deconstructing them. This listicle breaks down eight critical domains, from risk management to secure software development, equipping you with the practical tools and perspectives to confidently tackle the exam and earn your CISSP certification.
For each category, you'll find a realistic sample question scenario, a detailed rationale for the correct answer, and an essential breakdown of why common distractors are incorrect. This approach is designed to refine your analytical skills, foster critical thinking, and build the "managerial muscle memory" needed for success. Let's dive into the questions.
1. Risk Management Framework Selection
The CISSP exam frequently tests your ability to think like a security manager, and a foundational aspect of that role is selecting the right approach to manage organizational risk. These types of CISSP exam test questions evaluate your understanding of various risk management frameworks and your ability to apply the most appropriate one based on an organization's specific context, strategic goals, and regulatory requirements. This goes beyond rote memorization; it requires a deep comprehension of how different methodologies address risk from both a qualitative and quantitative perspective.
 Figure 1: Understanding and selecting the right risk management framework is crucial for aligning security with business objectives.
Figure 1: Understanding and selecting the right risk management framework is crucial for aligning security with business objectives.
Questions in this area often present a detailed scenario and ask you to choose the most appropriate action or framework. You'll need to accurately distinguish between frameworks like the NIST Risk Management Framework (RMF), which is widely used in U.S. federal agencies; ISO 27005 for international standards alignment; and OCTAVE (Operationally Critical Threat, Asset, and Vulnerability Evaluation) for a more self-directed, asset-focused approach.
Example Scenarios
- Financial Justification: A financial services company needs to justify a multi-million dollar security investment to its board of directors. In this case, a quantitative analysis is best. Calculating the Annual Loss Expectancy (ALE) by determining the Single Loss Expectancy (SLE) and Annualized Rate of Occurrence (ARO) provides concrete financial data to support the decision, making the business impact clear. This approach helps the board understand the return on security investment.
- Regulatory Compliance (Healthcare): A U.S. healthcare provider must ensure compliance with strict HIPAA regulations. The NIST RMF is a highly suitable choice as it provides a structured, repeatable process for managing security and privacy risk that aligns well with federal mandates, offering a robust and auditable approach.
- Global Standardization (Enterprise): A global corporation wants to standardize its risk management practices across all international business units, including its cloud deployments on AWS and Azure. Adopting ISO 27005 provides a globally recognized standard, ensuring consistency, facilitating communication about risk across different regions and cultures, and supporting certification efforts like ISO 27001.
Actionable Exam Tips
To master these questions, focus on the underlying business drivers behind each choice. A crucial part of risk management involves selecting and implementing appropriate cybersecurity risk assessment frameworks, which provide a structured approach to managing digital risk.
- Memorize Key Formulas: Know
ALE = SLE × AROcold. Be ready to calculate it or identify its components in a scenario. - Think Business First: The correct answer will almost always align with business objectives, not just technical perfection. Prioritize what best protects the organization's mission, assets, and reputation.
- Know the Risk Treatments: Be able to identify and differentiate the four primary responses to risk: Accept (acknowledging and tolerating the risk), Mitigate (reducing the risk's impact or likelihood), **Transfer (sharing the risk, e.g., through insurance or outsourcing), and Avoid (eliminating the risk source altogether).
- Qualitative vs. Quantitative: Understand when to use each. Quantitative analysis uses hard numbers and financial metrics (e.g., specific dollar amounts) and is ideal for budget justifications. Qualitative analysis uses subjective scales (e.g., high, medium, low) and is often quicker, used for initial assessments or when precise data is unavailable.
- Reflection Prompt: Consider a recent project you were involved in. How might a formal risk management framework, like NIST RMF or ISO 27005, have improved its security posture or stakeholder communication?
2. Access Control Models and Implementation
A significant portion of CISSP exam test questions revolves around your ability to select and apply the correct access control model. These questions test your comprehension of how different models grant or deny access to resources, forcing you to think like a security architect. The exam requires you to understand the fundamental principles, strengths, and weaknesses of models like Mandatory Access Control (MAC), Discretionary Access Control (DAC), Role-Based Access Control (RBAC), and Attribute-Based Access Control (ABAC). You must be able to justify why one model is superior to another in a given context.
This decision tree infographic helps visualize how to select the appropriate access control model based on an organization's primary security driver.
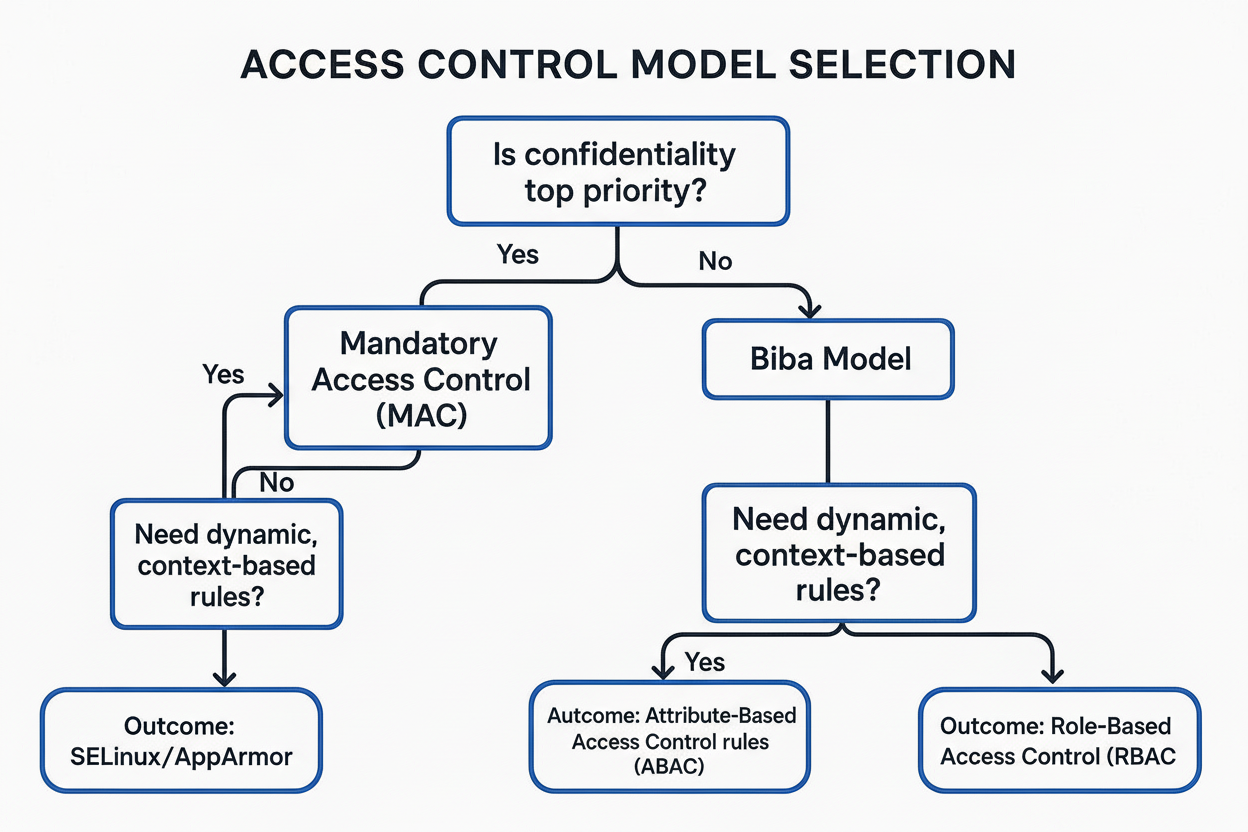 Figure 2: A decision tree illustrating how organizational security priorities guide the selection of appropriate access control models.
Figure 2: A decision tree illustrating how organizational security priorities guide the selection of appropriate access control models.
The visualization illustrates that the choice of an access control model is dictated by core business and security priorities, starting with confidentiality and integrity. Questions in this domain present scenarios where you must align a business need with a specific control framework. You will need to differentiate between theoretical models like Bell-LaPadula (focused on confidentiality) and Biba (focused on integrity) and their practical implementations in modern systems. Understanding these concepts is critical for answering complex situational questions.
Example Scenarios
- High-Security Government System: A top-secret military database requires a system where access is strictly determined by security clearances. Mandatory Access Control (MAC), specifically the Bell-LaPadula model, is the correct choice. It enforces a strict, centrally managed policy based on classification labels (e.g., Top Secret, Secret), preventing users from accessing data above their clearance level ("no read up") or declassifying data ("no write down"), thus ensuring confidentiality.
- Large Enterprise User Management: A large hospital needs to manage system access for thousands of doctors, nurses, and administrative staff across various applications, including electronic health record (EHR) systems. Role-Based Access Control (RBAC) is the most efficient and scalable solution. It simplifies administration by assigning permissions to roles (e.g., "Physician," "Billing Clerk," "Nurse") rather than to individual users, ensuring employees only have the access necessary to perform their specific job functions (least privilege).
- Cloud-Native Dynamic Access: A modern cloud application running on AWS must grant access based on dynamic conditions such as user location, time of day, device compliance, and even the sensitivity of the data being requested. Attribute-Based Access Control (ABAC) is the best fit. It uses policies with multiple attributes (user, resource, and environment) to make highly granular and context-aware access decisions, which is a core tenant of modern Zero Trust architectures.
Actionable Exam Tips
To succeed with these questions, you must grasp the core purpose of each model and the problems they are designed to solve. The exam will test if you can apply these theoretical concepts to practical, real-world security challenges.
- Confidentiality vs. Integrity: Remember this key distinction. Bell-LaPadula is primarily for confidentiality (prevents unauthorized information flow down levels). Biba is for integrity (prevents unauthorized modification, ensuring data trustworthiness). If the scenario emphasizes preventing unauthorized disclosure, think Bell-LaPadula. If it stresses preventing unauthorized modification, think Biba.
- Know the Spectrum: Understand that DAC is the most flexible and decentralized (users control access), MAC is the most restrictive and centralized (system controls access), and RBAC offers a scalable middle ground for most enterprises, combining flexibility with centralized role management.
- Think Centralized: CISSP questions often favor solutions that provide centralized, consistent control in enterprise environments. MAC and RBAC are generally preferred over the decentralized nature of DAC for managing large user bases and complex resources.
- Lattice Structure: Be aware that MAC models often use a lattice-based structure to define the permissible information flows between different security levels, establishing a clear hierarchy.
- Reflection Prompt: Imagine you're designing an access control system for a new HR application. Would you lean towards DAC, RBAC, or ABAC? Why, and what are the trade-offs?
3. Cryptography Algorithm Selection and Application
The CISSP exam places significant emphasis on a candidate's ability to select and apply the correct cryptographic solutions to protect data. These types of CISSP exam test questions probe your understanding of when to use symmetric versus asymmetric encryption, the strengths and weaknesses of various algorithms, and the role of hashing and digital signatures. The goal is to evaluate your practical knowledge in securing data-in-transit, data-at-rest, and ensuring data integrity and authenticity.
 Figure 3: Cryptography provides essential tools for securing data confidentiality, integrity, and authenticity across various states.
Figure 3: Cryptography provides essential tools for securing data confidentiality, integrity, and authenticity across various states.
Questions will often provide a business or technical scenario and require you to choose the most secure and efficient cryptographic method. You will need to differentiate between block ciphers like AES, asymmetric algorithms like RSA and ECC, and hashing functions such as SHA-256 or bcrypt. Understanding the complete cryptographic lifecycle, including robust key management, is essential for a high-level security professional.
Example Scenarios
- Secure Web Transactions: An e-commerce website must secure customer payment transactions, similar to how many online services handle sensitive data. The best implementation is TLS 1.3, which uses a combination of asymmetric encryption (like RSA or ECC) for the initial secure handshake and symmetric encryption (AES-256-GCM) for the bulk data transfer. This ensures both confidentiality (data cannot be read by unauthorized parties) and integrity (data cannot be tampered with).
- Software Authenticity: A software development company, like one distributing an Azure application, needs to ensure that its application updates have not been tampered with and originate from a trusted source. Using a digital signature based on an algorithm like RSA-2048 or higher allows users to verify the software's authenticity and integrity, assuring them that the update is legitimate and untampered.
- Password Storage: An organization needs to securely store user passwords in its database. The correct approach is to use a strong, salted hashing algorithm designed specifically for passwords, such as bcrypt or Argon2. These algorithms are computationally intensive and resistant to brute-force and rainbow table attacks, protecting user credentials even if the database is compromised.
Actionable Exam Tips
To succeed with these questions, you must understand the "why" behind each cryptographic choice, not just the "what." This includes balancing security requirements with performance considerations.
- Know the Standards: AES (Advanced Encryption Standard) is the modern, widely accepted standard for symmetric encryption. For asymmetric keys, remember that RSA 2048-bit is a common minimum, with 3072-bit or Elliptic Curve Cryptography (ECC) recommended for longer-term security and smaller key sizes.
- Symmetric vs. Asymmetric: Understand that symmetric encryption is much faster and ideal for bulk data encryption but presents a key distribution challenge. Asymmetric encryption is slower but solves the key distribution problem, making it perfect for secure key exchange, digital signatures, and establishing trust.
- Hashing vs. Encryption: Remember that hashing is a one-way function used for integrity verification (e.g., verifying file downloads, storing passwords) and cannot be reversed to reveal the original data. Encryption, however, is a two-way process that scrambles data to ensure confidentiality and can be reversed with the correct key. A secure hash function must be collision-resistant.
- Digital Signatures Provide Non-Repudiation: A key concept is that digital signatures use the sender's private key to sign a message hash, providing integrity, authenticity (proof of sender), and non-repudiation (the sender cannot deny sending the message). Crucially, they do not encrypt the message content itself.
- Reflection Prompt: If you needed to send a large, confidential file securely to a colleague over an untrusted network, what combination of cryptographic techniques would you employ and why?
4. Business Continuity and Disaster Recovery Planning
The CISSP exam places significant emphasis on an organization's ability to maintain operations during and after a disruptive event. These types of CISSP exam test questions assess your knowledge of the entire business continuity and disaster recovery (BCP/DRP) lifecycle, from initial analysis to plan testing and ongoing maintenance. You will be expected to demonstrate a firm grasp of key metrics, recovery strategies, and the processes that ensure a business can withstand adversity and minimize downtime.
Questions in this domain require you to apply concepts like the Business Impact Analysis (BIA) to identify critical business functions, their interdependencies, and the financial and operational impact of their disruption. You must understand how the results of a BIA directly influence the selection of appropriate recovery strategies, including the choice of alternate processing sites and data backup methodologies.
Example Scenarios
- Critical Financial Systems: A global financial institution with critical online trading systems requires near-instantaneous recovery to avoid catastrophic financial losses. It would implement a hot site with synchronous data replication across geographically dispersed data centers to meet a very low Recovery Time Objective (RTO) (e.g., minutes) and a near-zero Recovery Point Objective (RPO) (e.g., seconds), minimizing both downtime and data loss.
- Healthcare Data Protection: A healthcare provider must protect electronic patient records from loss due to a system failure or data corruption. Its BIA would mandate a very low RPO, likely 15 minutes or less, necessitating frequent backups (e.g., transactional logging or continuous data protection) or real-time journaling to minimize data loss in a disaster, ensuring patient safety and compliance.
- Manufacturing Firm's DR Validation: A manufacturing firm needs to validate its DR plan's effectiveness for its critical production control systems. It conducts an annual full-interruption test, physically failing over operations to its recovery site. This comprehensive exercise ensures all systems, processes, and personnel are prepared for a real event, identifying any gaps in the plan or team capabilities. This might be a costly exercise but proves operational readiness.
Actionable Exam Tips
To succeed with BCP and DRP questions, you must clearly differentiate between the core metrics and understand their business implications. The BIA is foundational, as it provides the justification for all subsequent planning efforts and expenditures, akin to a project manager defining scope and risk for a PMP certification.
- Differentiate RTO and RPO: Remember RTO (Recovery Time Objective) is about how quickly systems and applications must be restored to an operational state after an outage. RPO (Recovery Point Objective) is about how much data loss is acceptable, defining the maximum permissible data loss.
- Know Your Recovery Sites: A hot site is a fully equipped, mirrored facility ready for immediate use (fastest recovery, most expensive). A warm site has hardware but requires data restoration and configuration. A cold site is just space with basic infrastructure (slowest recovery, cheapest).
- BIA is Business-Focused: The BIA identifies critical business functions, their dependencies, and the impact of their disruption—not just IT systems. Its goal is to determine the impact of an outage on the entire organization, guiding resource allocation for recovery.
- Test, Test, Test: A plan that isn't tested is not a reliable plan. Be familiar with different test types, from simple tabletop exercises (discussion-based) to comprehensive full-interruption tests (simulating a real disaster).
- Understand Backup Types: Know the difference between full (all data), incremental (backs up changes since the last backup of any type), and differential (backs up changes since the last full backup) backups, including their restoration complexity and speed. Full backups are slowest to perform but quickest to restore. Incremental are quickest to perform but slowest to restore. Differential are a middle ground.
- Reflection Prompt: How does understanding RTO and RPO directly influence the choice of cloud recovery strategies (e.g., backup & restore, pilot light, warm standby, hot standby) for a critical application hosted on AWS or Azure?
5. Network Security Architecture and Design
A significant portion of the CISSP exam focuses on your ability to design and evaluate secure network architectures. These types of CISSP exam test questions assess your understanding of core principles like defense in depth, network segmentation, and modern paradigms such as Zero Trust. You will be expected to apply knowledge of the OSI and TCP/IP models, secure protocols, and the roles of various network devices to create resilient and secure network environments that protect organizational assets.
 Figure 4: Effective network security architecture employs multiple layers of defense and strategic segmentation to protect critical assets.
Figure 4: Effective network security architecture employs multiple layers of defense and strategic segmentation to protect critical assets.
Questions in this domain often involve analyzing a network diagram or a scenario description to identify security weaknesses or recommend the best configuration. You'll need to know how to properly implement controls like firewalls, IDS/IPS, and VPNs to minimize the attack surface while ensuring the network remains functional for business operations and meets compliance requirements.
Example Scenarios
- Secure Web Application Deployment: An enterprise is deploying a new web application that needs to be publicly accessible but also secure. A robust, three-tier architecture would involve placing the web servers in a DMZ (Demilitarized Zone), the application servers on a separate internal network segment, and the database servers on a highly restricted segment. Strict firewall rules would control traffic between each tier, limiting lateral movement if one tier is compromised.
- Enhanced Remote Access: A company wants to strengthen its remote access security for employees working from home, similar to how many organizations leverage VPNs. The best practice is to use a VPN concentrator and disable split tunneling, forcing all remote user traffic (including internet-bound traffic) through the corporate security stack for inspection, logging, and policy enforcement, preventing bypass of critical security controls.
- Preventing Lateral Movement: To prevent lateral movement after a potential breach and enforce strict access policies, an organization adopts a Zero Trust model. This requires micro-segmentation, continuous verification of identity and device posture for every access request, regardless of whether the user is on the internal or external network, and leveraging solutions like software-defined networking (SDN) to achieve granular control.
Actionable Exam Tips
To succeed with these questions, you must think in layers and understand how different security components work together to protect data in transit.
- Defense in Depth: This is a crucial concept. The correct answer often involves multiple, overlapping security controls (e.g., a perimeter firewall, an internal firewall, an IPS, and a web application firewall) rather than relying on a single solution. Layers create resilience.
- Know Your Devices: Clearly distinguish between an IDS (Intrusion Detection System), which detects and alerts on suspicious activity, and an IPS (Intrusion Prevention System), which can actively block malicious traffic based on predefined rules or signatures.
- Segment and Isolate: Understand that a DMZ is specifically designed to house public-facing services (e.g., web, email, DNS) to isolate them from the trusted internal network, minimizing the risk if these public services are compromised. Network segmentation, in general, is the primary control to limit the impact and spread of a breach within an internal network.
- Prioritize Secure Protocols: Always choose encrypted and authenticated protocols over their insecure counterparts. For instance, use SSH (Secure Shell, port 22) instead of Telnet (port 23) for remote administration and HTTPS (HTTP Secure, port 443) instead of HTTP (port 80) for web traffic.
- Reflection Prompt: If you were tasked with securing a new Internet of Things (IoT) network within an existing corporate infrastructure, what key architectural decisions would you make to segment it and apply the principle of least privilege?
6. Security Assessment and Testing Methodologies
The CISSP exam emphasizes the practical application of security principles, and a significant portion involves evaluating an organization's security posture. These types of CISSP exam test questions will challenge your understanding of security assessment and testing methodologies. You must know when and why to use different approaches, such as vulnerability assessments, penetration tests, audits, and log reviews, to identify and mitigate weaknesses effectively.
Questions in this domain require you to differentiate between testing strategies like white box, gray box, and black box, and to understand the goals and scope of each. You will be expected to know common frameworks like OWASP for web applications or NIST SP 800-115 for technical testing, and how they guide the assessment process.
*Video: A quick overview of security assessment types, providing context for the methods discussed.*Example Scenarios
- Pre-Launch Exploitable Flaws: An e-commerce company wants to identify exploitable flaws in its payment processing systems before a major product launch. A black box penetration test is most appropriate. This simulates an external attacker with no prior knowledge of the internal system, providing a realistic assessment of the system's resilience to outside threats.
- DevSecOps Integration: A software development team needs to integrate continuous security checks into their CI/CD pipeline, following DevSecOps principles. Implementing Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) tools based on the OWASP Top 10 ensures security is addressed throughout the SDLC, catching vulnerabilities early in development and runtime.
- Enterprise-Wide Resilience: A financial institution must verify its security controls and operational readiness against a sophisticated, persistent adversary. Conducting a red team/blue team exercise provides a comprehensive test of both defensive capabilities (blue team) and detection/response mechanisms against a simulated attack (red team), offering invaluable insights into true organizational resilience.
Actionable Exam Tips
To succeed with these questions, you must grasp the nuances that distinguish one testing method from another. A deep understanding of security assessment and testing methodologies is crucial for identifying the most effective approach in a given scenario.
- Know the Core Difference: Vulnerability scanning is an automated process to find known weaknesses (e.g., missing patches, misconfigurations). Penetration testing is a goal-oriented, manual process that includes attempting to exploit those weaknesses to demonstrate potential impact, providing a deeper, more realistic view of risk.
- "Box" Testing Levels: Remember the levels of knowledge given to the testers: White box (full knowledge of the system's architecture, code, and configurations), gray box (partial knowledge, simulating an insider or a targeted attacker), and black box (no knowledge, simulating an external attacker).
- Get Explicit Permission: The single most important first step before any penetration test (or ethical hacking activity) is obtaining explicit, written authorization from management (often called a "Rules of Engagement" document). Without this, it could be illegal.
- Prioritize Smartly: Remediate vulnerabilities based on risk, which is calculated by combining impact and likelihood (e.g., using CVSS scores or organizational specific criteria). A "critical" technical flaw on an isolated, non-critical system may be a lower business priority than a "medium" flaw on a public-facing, mission-critical server.
- Reflection Prompt: Your organization just had a critical incident. What type of assessment would be most appropriate post-incident to understand the root cause and prevent recurrence, and why?
7. Secure Software Development Lifecycle (SDLC)
CISSP exam test questions frequently evaluate your understanding of integrating security into every phase of software development, rather than treating it as an afterthought. This "shift-left" philosophy is at the core of the Secure Software Development Lifecycle (SDLC). These questions require you to know how security activities align with different development models and to recognize common software vulnerabilities and the principles used to prevent them. You must think proactively, focusing on building security in from the very beginning.
Questions in this domain will present scenarios where you must identify the appropriate security control or practice for a specific SDLC phase. This involves knowing different SDLC models (e.g., Waterfall, Agile, DevOps), the security activities relevant to each phase (e.g., threat modeling in design, code scanning in development, security testing in quality assurance), and foundational secure design principles like least privilege and fail-secure.
Example Scenarios
- Automated Security in DevOps: A SaaS provider wants to automate security checks within its rapid deployment pipeline, characteristic of a modern DevOps environment. Integrating Static Application Security Testing (SAST) tools into the Continuous Integration/Continuous Deployment (CI/CD) pipeline is the best approach to automatically scan source code for vulnerabilities (like SQL injection or buffer overflows) before deployment, catching issues early and efficiently.
- Early Threat Identification: A financial services company is designing a new online banking application. The security team should conduct threat modeling using a framework like STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege) during the design phase. This helps identify and mitigate potential architectural threats and design flaws early, significantly reducing remediation costs later.
- Mobile App Security Best Practices: A development team building a new mobile app needs a standardized way to address common security flaws. Following the OWASP Mobile Security Testing Guide provides a comprehensive framework and checklist for identifying and remediating vulnerabilities specific to mobile platforms, ensuring robust security for the application and its user data.
Actionable Exam Tips
To succeed with these questions, focus on the principle of embedding security throughout the entire lifecycle. Security is not a separate phase; it is an integral part of every stage, from requirements gathering to deployment and maintenance. This aligns with modern ITIL practices that emphasize security as a continuous consideration.
- Shift Security Left: The most effective and cost-efficient time to address a vulnerability is in the requirements and design phases. Remember that security is everyone's responsibility, not just the security team's.
- Know Your Testing Types: Differentiate between SAST, which analyzes static source code for flaws without executing the code, and DAST (Dynamic Application Security Testing), which tests a running application for vulnerabilities from the outside, simulating an attacker.
- Memorize Key Frameworks: Be familiar with the OWASP Top 10 vulnerabilities (e.g., Injection, Broken Authentication, Sensitive Data Exposure, Cross-Site Scripting) and threat modeling methodologies like STRIDE.
- Understand Secure Design Principles: Know concepts like fail-secure (the system defaults to a secure state upon failure, e.g., a locked door), least privilege (granting only the minimum necessary permissions for a user or process to perform its function), and the critical importance of server-side input validation to prevent injection attacks.
- Reflection Prompt: How can a security professional effectively advocate for "shifting left" in an organization that traditionally only tests security at the very end of the development cycle?
8. Governance, Compliance, and Legal/Regulatory Requirements
A significant portion of the CISSP exam evaluates your understanding of the legal and regulatory landscape that governs information security. These types of CISSP exam test questions assess your ability to apply security governance frameworks, adhere to compliance mandates, and navigate complex legal issues. You are expected to demonstrate knowledge of major regulations, the hierarchy of organizational policies, and key legal concepts that form the bedrock of a robust security program.
Questions in this domain often require you to act as a security leader who must align technical controls with business obligations and legal duties. You'll need to understand the distinctions and applications of major regulations like GDPR, HIPAA, PCI-DSS, and SOX, as well as the core principles of due care and due diligence. For robust governance and compliance, understanding various legal and regulatory requirements, including global standards like ISO 27001 for information security management, is crucial for CISSP professionals.
Example Scenarios
- Credit Card Processing Compliance: An e-commerce merchant processing credit cards must achieve PCI-DSS compliance. This involves implementing specific controls across 12 requirements, such as encrypting cardholder data in transit and at rest, maintaining a secure network, and regularly testing security systems and processes. Non-compliance can lead to severe financial penalties and loss of processing privileges.
- International Data Privacy: A multinational corporation handling data of EU citizens, regardless of where the company is based, must comply with GDPR (General Data Protection Regulation). This requires appointing a Data Protection Officer (DPO), implementing "privacy by design" and "privacy by default," obtaining explicit consent for data processing, and ensuring a legal basis for all data processing activities.
- U.S. Healthcare Patient Data: A U.S. healthcare provider is required to protect patient information under the HIPAA Privacy Rule and Security Rule. This means implementing appropriate administrative, physical, and technical safeguards like access controls, encryption of electronic Protected Health Information (ePHI), and regular risk assessments to ensure the confidentiality, integrity, and availability of patient data.
Actionable Exam Tips
To succeed with these questions, you must connect high-level policies and laws to practical security controls. This area is a cornerstone of the exam.
- Know the Policy Hierarchy: Remember that Policies are high-level, mandatory statements outlining management's intent. Standards define specific mandatory requirements or rules (e.g., "all passwords must be 12 characters"). Procedures are step-by-step implementation guides. Guidelines are recommended best practices, which are not mandatory but provide helpful advice.
- Due Care vs. Due Diligence: Due care is the action a reasonable and prudent person would take to protect others or assets (the "doing"). For example, implementing security controls like firewalls and antivirus software. Due diligence is the research and investigation performed beforehand to identify risks and determine the correct course of action (the "thinking"). For example, conducting a BIA or a risk assessment.
- Master Key Regulations: Understand the scope of major laws. GDPR applies globally to any organization processing EU residents' data. PCI-DSS is a contractual standard, not a law, but it's mandatory for anyone storing, processing, or transmitting cardholder data, with severe financial penalties for non-compliance. SOX (Sarbanes-Oxley Act) focuses on financial reporting and internal controls for public companies.
- Classify and Protect: Data classification (e.g., Public, Internal, Confidential, Secret, Top Secret) should directly inform the level of security controls applied. The more sensitive the data, the stronger the protection required, aligning security efforts with business value and risk.
- Reflection Prompt: How would a data breach involving personally identifiable information (PII) on an AWS server impact an organization's compliance obligations under both GDPR and HIPAA, and what immediate steps would a CISSP-certified manager prioritize?
CISSP Exam Topics: 8-Point Comparison Guide
| Topic | Implementation Complexity 🔄 | Resource Requirements ⚡ | Expected Outcomes 📊 | Ideal Use Cases 💡 | Key Advantages ⭐ |
|---|---|---|---|---|---|
| Risk Management Framework Selection | Moderate: Requires understanding multiple frameworks and formulas | Moderate: Knowledge-based, some formula memorization | Effective risk prioritization and treatment decisions | Organizations needing structured risk evaluation and treatment | Aligns with real-world security management; promotes critical thinking |
| Access Control Models and Implementation | Moderate to High: Diverse models, theoretical and practical | Moderate: Understanding various models and controls | Proper access restrictions and security architecture | Environments requiring tailored access control (e.g., military, enterprises) | Clear model distinctions; practical applications in security design |
| Cryptography Algorithm Selection and Application | High: Requires memorizing algorithms, strengths, and lifecycle | Moderate to High: Technical knowledge of cryptographic methods | Strong data protection and secure communication | Scenarios demanding data confidentiality, integrity, and authentication | Clear right/wrong solutions; essential for securing sensitive data |
| Business Continuity and Disaster Recovery Planning | Moderate: Requires knowledge of metrics and testing methods | Moderate: Planning, testing resources, and infrastructure | Enhanced organizational resilience and recovery capabilities | Organizations needing to maintain operations amid disruptions | Practical and metric-driven; applies broadly across industries |
| Network Security Architecture and Design | High: Involves detailed protocol, device knowledge, and design principles | Moderate to High: Network hardware and configuration understanding | Secure network infrastructures minimizing attack surface | Enterprises designing or improving network security | Fundamental for security architecture; leverages visual and practical skills |
| Security Assessment and Testing Methodologies | Moderate to High: In-depth knowledge of tools and testing types | Moderate: Tool usage and interpretation skills | Identification and remediation of vulnerabilities | Mature security programs and compliance testing | Defined methodologies; supports ongoing security posture improvement |
| Secure Software Development Lifecycle (SDLC) | Moderate to High: Integrates security into complex dev processes | Moderate to High: Requires collaboration between dev and security teams | Reduced software vulnerabilities and secure development practices | Organizations adopting DevSecOps or secure coding practices | Prevents vulnerabilities early; cost-effective security integration |
| Governance, Compliance, and Legal/Regulatory Requirements | Moderate to High: Understanding evolving laws and policies | Low to Moderate: Mainly knowledge and policy enforcement | Regulatory compliance and well-governed security programs | Organizations under strict regulatory environments | Essential for strategic roles; frameworks for organizational security |
From Theory to Test Day: Your Next Steps to Certification Success
You've just navigated through a demanding gauntlet of CISSP exam test questions, dissecting everything from foundational Risk Management Frameworks to the nuances of the Secure Software Development Lifecycle. Moving beyond simply knowing the definitions of these concepts is the most critical pivot in your study plan. The real challenge, and where true mastery is demonstrated, lies in applying this knowledge to complex, multifaceted scenarios, just like the ones we've explored.
The journey to CISSP certification is not a sprint; it is a marathon of dedicated, intelligent practice. The goal isn't rote memorization. Instead, it's about building the analytical "muscle memory" required to deconstruct a question, identify the core security principle at stake, eliminate distractors, and select the best possible answer from a list of technically plausible options. This is the "think like a manager" mindset that separates passing candidates from the rest.
Synthesizing Your Knowledge: Key Takeaways
As you move forward, your focus should shift from learning individual topics in isolation to understanding their interconnectedness. Consider these essential takeaways from the questions covered:
- Risk is the Foundation: Notice how risk management principles are the bedrock for decisions in almost every other domain, whether it's selecting an access control model, justifying a budget for a disaster recovery site, or prioritizing vulnerabilities. Your ability to assess and manage risk will be tested repeatedly.
- Context is King: The "right" answer consistently depends on the scenario's specific context. A cryptographic solution perfect for data at rest is often inappropriate for high-volume data in transit. A security control vital for a financial institution might be overkill for a small startup. Always let the business requirements, organizational culture, and regulatory landscape guide your choices.
- Process Over Products: The CISSP exam prioritizes well-defined processes, policies, and governance structures over specific vendor technologies or product names. Mastering frameworks like the BCP/DRP process or the SDLC phases is far more valuable than memorizing specific product features.
- Reflection Prompt: How do the concepts of "due care" and "due diligence" underpin the entire CISSP Common Body of Knowledge (CBK)? Think about specific examples from the domains we covered.
Your Actionable Path to Success
To transform this theoretical knowledge into exam-day confidence, you need a structured and consistent approach. Merely rereading study guides is not enough. Your next steps should involve active, targeted practice that simulates the real testing environment.
- Identify Your Weakest Domains: Go back through the practice questions or any practice tests you've taken. Which domains felt the most challenging? Was it the legal intricacies of compliance or the technical details of network architecture? Acknowledge these areas and allocate extra study time and targeted practice to them.
- Practice Timed Question Blocks: Set a timer and work through blocks of 25, 50, or 100 questions. This builds the mental stamina required for the lengthy exam and helps you manage your time effectively under pressure, mimicking the adaptive format of the CISSP.
- Analyze Every Answer Deeply: For every practice question, whether you got it right or wrong, read the full explanation. Understand why the correct answer is the best choice and, just as importantly, why the other options are incorrect. This deep analysis is what truly solidifies your understanding of core concepts and helps you identify common traps.
Ultimately, your success on the CISSP exam will be a direct reflection of your ability to apply these broad, critical-thinking skills to real-world security challenges. By consistently practicing with high-quality CISSP exam test questions and dissecting the logic behind each answer, you are not just preparing to pass a test; you are preparing to be a competent and effective information security leader.
Ready to elevate your preparation with a structured, data-driven approach? MindMesh Academy provides a comprehensive platform with thousands of realistic CISSP exam test questions, detailed analytics to pinpoint your weak areas, and adaptive learning technology to optimize your study sessions. Stop guessing and start mastering the concepts you need to succeed by exploring our CISSP resources at Mindmesh Academy.

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.