
10 Master CCNA Examination Questions for 2025 Success
Mastering the CCNA: 10 Essential Examination Questions for 2025 Success
Earning your certification by passing the Cisco CCNA 200-301 exam requires more than simple rote memorization of facts. It demands a functional, deep understanding of core networking concepts and their dependencies. Many candidates fail because they drill practice questions without dissecting the logic behind why an answer is correct. This passive method leads to frustration. The current exam evaluates how you apply knowledge to solve actual technical problems rather than focusing on your ability to recall definitions, acronyms, or specific port numbers.
This guide breaks that cycle by analyzing common testing patterns. We deconstruct 10 essential types of CCNA examination questions to show you the logical thinking and real-world application needed to succeed on test day. We analyze each question type and offer clear takeaways to build proficiency in IP addressing, routing protocols, and network security. By the end, you will understand the underlying principles behind various configurations. Developing this skill is vital for passing the test and building a long-term professional career in the technical field.
Our approach mirrors the evidence-based techniques used at MindMesh Academy. We move beyond passive review to turn your study sessions into active, focused learning exercises. This preparation ensures you are ready for the various challenges the current exam presents to students. To diversify your study plan, consider creating your own practice quizzes online to reinforce these complex topics. This article provides the practical skills and insights needed to be well-prepared for the CCNA exam and your future professional networking roles.
1. OSI Model and Network Layer Identification
Thorough knowledge of the Open Systems Interconnection (OSI) model is mandatory for passing the current CCNA exam. Many examination questions test your ability to assign networking devices, protocols, and tasks to the correct OSI layer. You must do more than memorize facts. You need to understand how data moves through the stack. This serves as the baseline for both designing network layouts and fixing connectivity problems.
Why It's a Core Concept
The OSI model splits network communication into seven distinct steps. These range from the Physical Layer 1 at the bottom up to the Application Layer 7 at the top. The CCNA exam requires you to know exactly where hardware like switches and routers operate and why. Understanding these layers helps you grasp encapsulation and de-encapsulation. This is the process where data is wrapped in protocol headers as it moves down the stack and unwrapped as it moves back up at the receiving end. It helps you visualize the path data takes from a local workstation to a remote server.
Example Question and Analysis
Question: At which layer of the OSI model does a standard network switch primarily operate to forward traffic based on hardware addresses?
- A) Layer 1 (Physical)
- B) Layer 2 (Data Link)
- C) Layer 3 (Network)
- D) Layer 4 (Transport)
Correct Answer: B) Layer 2 (Data Link)
Breakdown:
- Layer 1 (Physical): This layer handles the actual physical transmission of bits. It includes hardware like Ethernet cables, fiber optic strands, and hubs. A switch is more intelligent than a hub and does more than just repeat electrical signals to every port.
- Layer 2 (Data Link): This layer organizes bits into frames. It uses Media Access Control (MAC) addresses, which are burned into the hardware, to make forwarding decisions within a local network segment or LAN. A standard switch functions at this layer by maintaining a MAC address table to track devices.
- Layer 3 (Network): This layer manages logical addressing and routing. It uses IP addresses to move data packets between different networks. This is the primary function of a router. While multi-layer switches exist, basic switching is a Layer 2 process.
- Layer 4 (Transport): This layer handles end-to-end communication and ensures data arrives correctly. It manages connection setup, data segmentation, and error checking using protocols like TCP and UDP.
Actionable Study Tips
To prepare for your exam, stop trying to memorize the layers in isolation. Instead, try to connect each layer to a real-world device or protocol to see how they interact.
- Create a Mnemonic: Use a memory aid like "Please Do Not Throw Sausage Pizza Away" to remember the layers in order from 1 to 7 (Physical, Data Link, Network, Transport, Session, Presentation, Application). Many students find this easier than memorizing the list from scratch.
- Build a Protocol Table: Create a chart with columns for the layer number, the name, common devices, and specific protocols. For example, list Layer 3 as the Network layer and associate it with routers and IP. Hand-writing this table often helps with retention.
- Visualize Data Flow: Imagine a user sending an email. Trace that data from the Application Layer on the computer, through the headers added at the Transport and Network layers, into the frames at the Data Link layer, and finally into electrical pulses or light signals.
Reflection Prompt: Think about the top three layers: Application, Presentation, and Session. Can you name one protocol for each? Consider how knowing these layers would help you if a user can ping a server but cannot load a specific web page.
For a more detailed look at this topic, you can read this guide on layered network design. Learn more about the layered network design and the OSI model on mindmeshacademy.com.
2. IP Addressing and Subnetting Calculations
IP addressing and subnetting proficiency is the most technical skill tested on the current CCNA exam. You will face several CCNA examination questions that require you to calculate network addresses, broadcast addresses, and usable host ranges under strict time limits. This is not just a theoretical topic for the test. It is a fundamental requirement for anyone building or fixing modern IP networks.
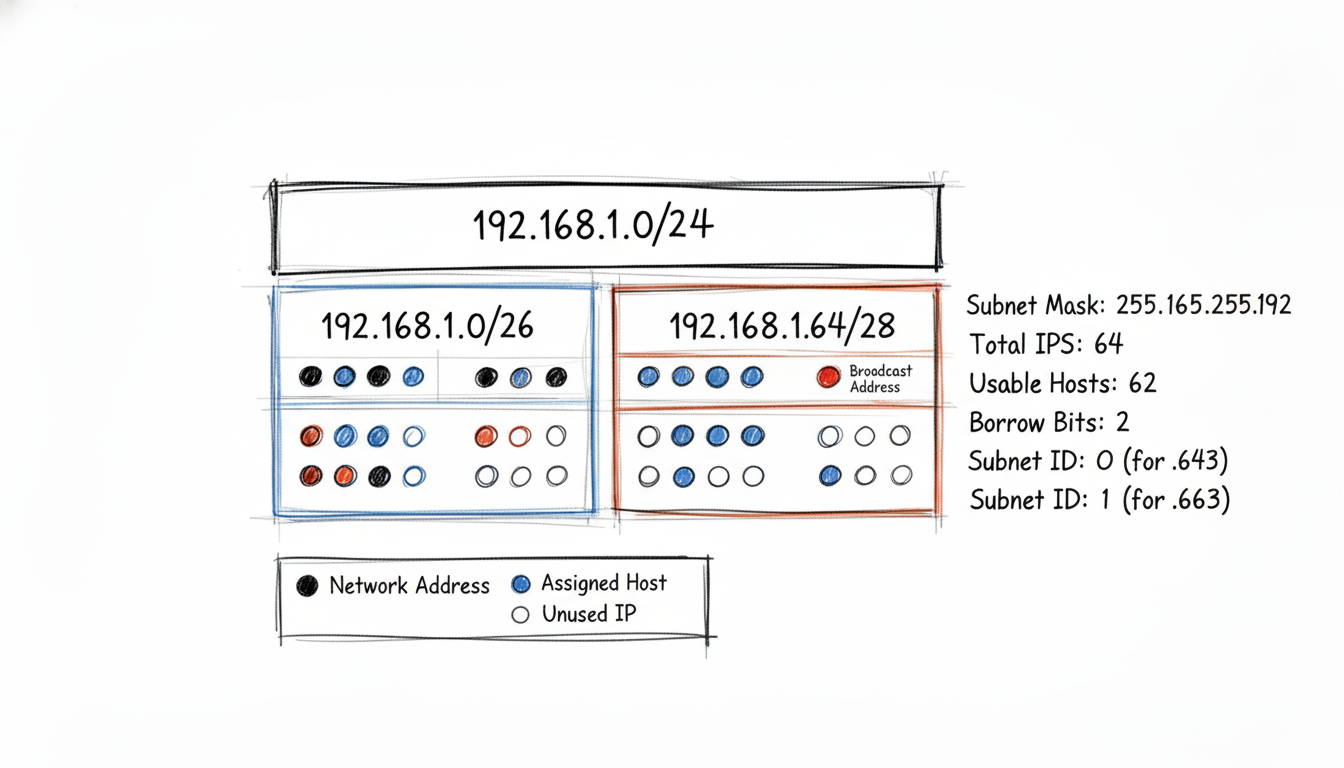
Why It's a Core Concept
Subnetting allows a network administrator to divide a large network into smaller, more efficient segments. This improves security because you can isolate sensitive traffic from the rest of the network. It also increases performance by reducing the size of broadcast domains, which prevents unnecessary traffic from flooding your hardware. When you can segment issues, troubleshooting becomes much faster. Cisco focuses on this skill because it reflects daily configuration tasks on routers and switches. A single error in IP allocation can lead to connectivity failures or security holes. These same principles apply to cloud environments like AWS and Azure just as much as they do to local data centers.
Example Question and Analysis
Question: An administrator needs to configure a new network segment using the IP address 192.168.10.19/28. What is the valid host range for this subnet?
- A) 192.168.10.1 - 192.168.10.14
- B) 192.168.10.16 - 192.168.10.31
- C) 192.168.10.17 - 192.168.10.30
- D) 192.168.10.18 - 192.168.10.29
Correct Answer: C) 192.168.10.17 - 192.168.10.30
Breakdown:
- Identify the Block Size: A /28 mask uses 28 bits for the network portion, leaving 4 bits (32 minus 28) for host addresses. Since 2 to the fourth power is 16, that becomes your block size.
- Find the Network Address: Subnets will increment by 16 in the fourth octet: 0, 16, 32, 48, and so on. The IP address 192.168.10.19 falls into the block that starts at 192.168.10.16. This is the network address for this segment.
- Find the Broadcast Address: The next subnet in the sequence begins at 192.168.10.32. One address before that is 192.168.10.31, which serves as the broadcast address for the 192.168.10.16 network.
- Determine the Host Range: Usable host addresses are the IPs sitting between the network address and the broadcast address. This results in the range from 192.168.10.17 to 192.168.10.30.
Actionable Study Tips
Speed and precision are vital for answering subnetting questions during the exam. Consistent practice is the only way to build the muscle memory required to pass with confidence.
- Learn the "Magic Number" Method: For fast calculations in the modified octet, subtract the decimal value of the subnet mask from 256. With a /28 mask (255.255.255.240), the calculation is 256 - 240. The result, 16, is your block size and increment.
- Practice Daily: Spend 20 minutes every day solving random subnetting problems to build speed. Move beyond Class C and practice Class B and Class A scenarios where the subnetting occurs in the second or third octets. Focus on identifying the network address and host range without writing out long binary strings.
- Write It Down: As soon as the exam begins, use your provided scratchpad or whiteboard to list the powers of 2 (128, 64, 32, 16, 8, 4, 2, 1) and their decimal mask equivalents. This visual reference helps you avoid simple math errors when you are dealing with the pressure of the clock.
Reflection Prompt: Consider a scenario where you are given a /27 network. How many usable hosts can it support, what would be the block size, and why is knowing this immediately beneficial when planning an AWS VPC subnet?
3. Routing Protocols Comparison (RIP, OSPF, EIGRP)
Many CCNA examination questions focus on your ability to distinguish between major Interior Gateway Protocols like RIP, EIGRP, and OSPF. The exam goes beyond basic definitions. You must compare their metrics, convergence speeds, scalability, and administrative distances. Understanding these trade-offs is necessary for designing and repairing networks. Study how these protocols handle routing updates and affect router CPU and memory.
Why It's a Core Concept
Routing protocol selection is a primary design choice. The current exam confirms your understanding of distance-vector, hybrid, and link-state protocols. This knowledge determines how routers share information and calculate the fastest paths to a destination. It also dictates how a network reacts when a link goes down. In a production environment, your choice affects network stability and how efficiently the hardware uses its resources. Poor protocol selection can limit growth as the organization expands.
Example Question and Analysis
Question: A network administrator is configuring a router that has learned the same route to a destination network via both OSPF and EIGRP. Assuming default configurations, which routing protocol's path will be installed in the routing table?
- A) OSPF, because it is an open standard.
- B) EIGRP, because it has a lower default administrative distance.
- C) Both routes will be installed and used for load balancing.
- D) The router will prompt the administrator to choose one.
Correct Answer: B) EIGRP, because it has a lower default administrative distance.
Breakdown:
- Administrative Distance (AD): This integer value from 0 to 255 ranks the reliability of a routing source. A lower value indicates a more trusted source and is always the preferred choice for the routing table.
- EIGRP's AD: The standard administrative distance for internal EIGRP routes is 90. This value makes it more preferable than most other interior gateway protocols.
- OSPF's AD: The standard administrative distance for OSPF routes is 110. While OSPF is widely used, Cisco hardware treats it as less reliable than EIGRP by default.
- Conclusion: Since 90 is less than 110, the router trusts the EIGRP-learned route more. It installs the EIGRP path in the routing table and ignores the OSPF route for that specific destination.
Actionable Study Tips
To master these comparisons, focus on protocol differences and memorize the values routers use for decision-making.
- Create a Comparison Chart: Build a table comparing RIP, EIGRP, and OSPF. Include columns for Protocol Type, Default AD, and Metrics like hop count, bandwidth, delay, or cost. Track the specific algorithms used, such as Bellman-Ford, DUAL, or SPF. Note the scalability limits and how fast each protocol recovers after a network change.
- Memorize Administrative Distances: Use flashcards for AD values. You must recall the defaults for connected networks (0), static routes (1), EIGRP (90), OSPF (110), RIP (120), and external EIGRP (170) without pausing. Knowing these numbers is vital for interpreting routing tables.
- Understand the "Why": Do not just learn that OSPF handles large networks better than RIP. Study how link-state protocols give each router a map of the whole network. This avoids the 15-hop limit and slow convergence times found in distance-vector protocols like RIP. This logic ensures you pass with confidence.
Reflection Prompt: If you had to choose between OSPF and EIGRP for a large network with equipment from many different vendors, which would you pick and why? What are the key considerations for such a decision in a multi-vendor environment, similar to what you might encounter in a large Azure deployment?
4. VLAN Configuration and Inter-VLAN Routing
Virtual Local Area Networks (VLANs) provide the primary method for segmenting local area networks at Layer 2. The current exam evaluates your practical skill in configuring and managing these logical segments. These questions go beyond basic definitions. You must demonstrate a clear grasp of command syntax for creating VLANs, assigning specific ports, setting up trunk links, and enabling communication between separate VLANs. Proficiency in these tasks allows you to build secure and efficient networks that remain manageable as an organization grows.
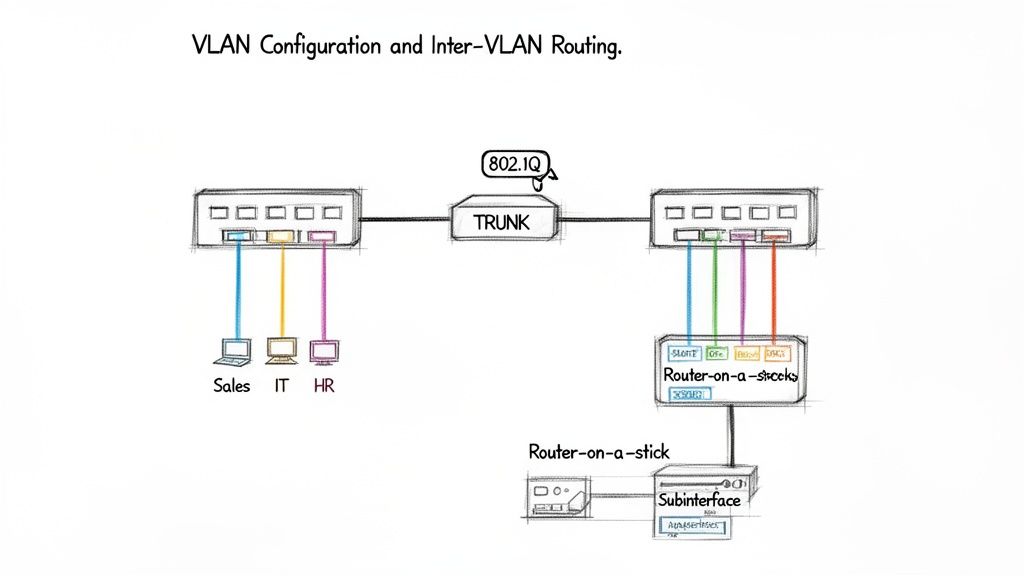
Why It's a Core Concept
Administrators use VLANs to group devices logically, even if those devices connect to different physical switches. This approach strengthens security by isolating sensitive traffic from the rest of the network. It also improves performance by limiting the size of broadcast domains. This prevents unnecessary traffic from flooding the entire infrastructure. The current exam verifies that you can implement this segmentation by testing your ability to configure access ports for single devices and trunk ports to carry traffic for multiple VLANs. You will need to understand VLAN tagging using the IEEE 802.1Q standard. This standard identifies which frame belongs to which VLAN as it moves across a trunk link. This skill is required for everything from small office branch setups to complex data center architectures.
Example Question and Analysis
Question: A network administrator needs to configure interface GigabitEthernet0/1 on a switch to carry traffic for VLAN 10, VLAN 20, and VLAN 30 between two switches. Which command sequence correctly achieves this?
- A)
interface gi0/1,switchport mode access,switchport access vlan 10,20,30 - B)
interface gi0/1,switchport mode trunk - C)
interface gi0/1,switchport mode trunk,switchport trunk allowed vlan 10,20,30 - D)
interface gi0/1,vlan 10,vlan 20,vlan 30
Correct Answer: C) switchport mode trunk, switchport trunk allowed vlan 10,20,30
Breakdown:
- A)
switchport mode access: This command configures the port for a single VLAN. It is used for connecting end devices like PCs or printers that belong to one segment. An access port cannot carry traffic for multiple VLANs. - B)
switchport mode trunk: This command sets the port as a trunk correctly. By default, a Cisco trunk allows all active VLANs. While this might transport the traffic for VLANs 10, 20, and 30, it is less specific than the requirement and poses a security risk by allowing unnecessary traffic. - C)
switchport mode trunk,switchport trunk allowed vlan...: This sequence is the most accurate. It sets the port to trunk mode and then explicitly defines which VLANs are permitted to cross the link. This method is secure and helps manage bandwidth by filtering out broadcast traffic from other VLANs. - D)
vlan 10...: These commands are used in global configuration mode to create the VLAN database entry. They do not configure an interface to act as a trunk or an access port.
Actionable Study Tips
To understand VLANs, move from reading documentation to practical command implementation. Hands-on practice with the Cisco CLI is the best way to prepare for these types of exam items.
- Differentiate Port Modes: Understand the difference between an access port and a trunk port. Access ports carry traffic for one VLAN. Trunk ports use 802.1Q tags to transport traffic for many VLANs across a single cable.
- Practice Inter-VLAN Routing: Build a Router-on-a-Stick (ROAS) configuration in a lab tool like Cisco Packet Tracer or GNS3. You must create subinterfaces on a router’s physical port and assign the correct encapsulation type to each.
- Learn the Native VLAN: Study how the native VLAN works on a trunk. This VLAN sends traffic without a tag. Misconfigurations here can lead to security risks like VLAN hopping. You should know how to change the native VLAN from the default.
- Use Command Drills: Practice the syntax until it becomes second nature. Focus on creating VLANs, assigning access ports, and modifying trunks using
switchport trunk allowed vlan add.
Reflection Prompt: Imagine a small office with three departments: Sales, Marketing, and IT. Each department needs its own logical network for privacy. How would VLANs help this setup reduce broadcast traffic? What is the main security risk if you leave all your trunk ports set to allow all VLANs by default?
5. Access Control Lists (ACL) Configuration and Filtering
Configuring and troubleshooting Access Control Lists (ACLs) is a fundamental skill frequently tested in CCNA examination questions. These items evaluate your ability to filter network traffic based on specific criteria like source IP addresses, destination IP addresses, or port numbers. Mastering ACLs is mandatory for network security and traffic management. This makes them a vital part of the current exam requirements and a necessary skill for any professional working with Cisco hardware.
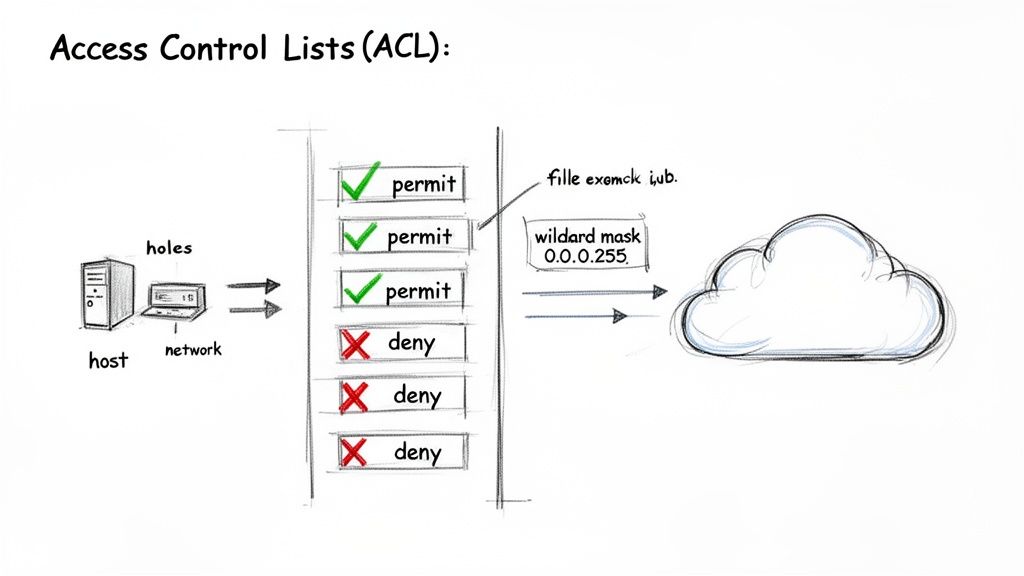
Why It's a Core Concept
ACLs are the primary tool on Cisco routers and switches for packet filtering, providing a direct method of network security. They offer control over exactly what traffic enters or exits an interface. To succeed on the CCNA exam, you must distinguish between standard and extended ACLs, grasp top-down rule processing, and apply these lists to interfaces to meet security goals. Understanding ACL logic is a fundamental part of a defense-in-depth security strategy. This logic is similar to how you use security groups and network ACLs to manage traffic in cloud environments like AWS.
Example Question and Analysis
Question: A network administrator needs to prevent all hosts from the 192.168.10.0/24 network from accessing a specific server at 10.1.1.5. The administrator applies an ACL to the router interface connected to the 192.168.10.0/24 network. Which command is most appropriate to achieve this goal?
- A)
access-list 1 deny 192.168.10.0 255.255.255.0 - B)
access-list 101 deny ip 192.168.10.0 0.0.0.255 host 10.1.1.5 - C)
access-list 101 permit ip 192.168.10.0 0.0.0.255 host 10.1.1.5 - D)
access-list 1 deny host 10.1.1.5
Correct Answer: B) access-list 101 deny ip 192.168.10.0 0.0.0.255 host 10.1.1.5
Breakdown:
- Option A: Incorrect. This command uses a standard ACL (ranges 1-99 or 1300-1999). Standard ACLs only filter based on the source IP address and cannot identify a specific destination server. Also, 255.255.255.0 is a subnet mask; ACLs require a wildcard mask to function correctly.
- Option B: Correct. This uses an extended ACL (ranges 100-199 or 2000-2699). Extended ACLs filter based on source, destination, protocol, and port. It correctly identifies the source network (192.168.10.0 with wildcard 0.0.0.255) and the destination host (10.1.1.5). The "deny ip" action meets the requirement perfectly.
- Option C: Incorrect. This command would permit the traffic instead of blocking it. Using this would allow the network to access the server, which is the opposite of the administrator's goal.
- Option D: Incorrect. This is a standard ACL that would deny traffic coming from the server at 10.1.1.5. It does not stop traffic sent from the 192.168.10.0/24 network toward the server.
Actionable Study Tips
To master ACLs for your CCNA exam, focus on the logic behind the rules and how they behave in real-world scenarios.
- Memorize ACL Ranges: Committing the numerical ranges to memory is vital. Standard ACLs use 1-99 and 1300-1999, while extended lists use 100-199 and 2000-2699. Knowing these by heart helps you quickly determine what criteria can be filtered during the test.
- Master Wildcard Masks: You must perform these calculations rapidly. The easiest method is to subtract the subnet mask from 255.255.255.255. For instance, a /24 subnet mask (255.255.255.0) results in a wildcard mask of 0.0.0.255. Understanding this logic prevents simple errors.
- Visualize the Logic: Cisco hardware evaluates ACLs sequentially from top to bottom. The first rule that matches a packet is the only one applied; the router ignores every line after that. Always account for the "implicit deny any" at the end of every list, as it can block all traffic if you forget to include permit statements.
Reflection Prompt: Think about the "implicit deny any" at the end of every ACL. Why is this a dangerous aspect of configuration during troubleshooting? Compare this to the behavior of an AWS Security Group, which denies all traffic by default until you add an allow rule.
For a deeper understanding of network filtering principles, you can review this guide to AWS security groups and network ACLs. You can learn more about network security and ACL principles on mindmeshacademy.com.
6. Network Address Translation (NAT) Implementation
The current CCNA exam evaluates your proficiency with Network Address Translation (NAT) configuration and troubleshooting. This technology remains a standard method for preserving the limited supply of public IPv4 addresses while shielding internal network architectures from external view. Exam questions typically evaluate your understanding of Static NAT, Dynamic NAT, and Port Address Translation (PAT). You must identify which method fits a specific business requirement or network topology. Mastering these variations is essential for any technician managing a network perimeter.
Why It's a Core Concept
NAT allows devices using private, non-routable IP addresses to reach external networks like the internet. To succeed on the exam, you must grasp the translation sequence and the four address types. An inside local address is the private IP assigned to a device on the internal network. The inside global address is the public IP that represents one or more inside local addresses to the outside world. Conversely, the outside global address is the IP assigned to a host on the external network. The outside local address is how that external host appears to the internal network. Managing these mappings is a daily task for network engineers trying to stretch IPv4 resources while maintaining security at the network edge, especially as public addresses become harder to acquire.
Example Question and Analysis
Question: A network administrator needs to allow multiple internal hosts using private IP addresses from the 192.168.10.0/24 range to access the internet using a single public IP address assigned to the router's external interface. Which command is essential for this configuration?
- A)
ip nat inside source static 192.168.10.5 203.0.113.50 - B)
ip nat pool PUBLIC_IPS 203.0.113.10 203.0.113.20 netmask 255.255.255.0 - C)
ip nat inside source list 1 interface GigabitEthernet0/1 overload - D)
ip nat outside
Correct Answer: C) ip nat inside source list 1 interface GigabitEthernet0/1 overload
Breakdown:
- Static NAT: The command in option A creates a permanent, one-to-one entry in the translation table. This means only one specific internal host, 192.168.10.5, can use the specific public IP 203.0.113.50. This fails the requirement because it does not allow multiple internal hosts to share the single available public address.
- Dynamic NAT Pool: Option B defines a group of public addresses. This method allocates a public IP to an internal host from the pool on a first-come, first-served basis. If the question required a many-to-many mapping where you had a range of public IPs, this would be relevant. However, the scenario specifically limits the administrator to using one single public IP.
- PAT (Port Address Translation): The
overloadparameter in option C is the defining characteristic of Port Address Translation. By appending unique source port numbers to the single public IP address, the router can track thousands of individual sessions for different internal hosts at the same time. This approach provides the highest level of IP address conservation. Thelist 1portion identifies the internal traffic permitted for translation via a standard access control list. - Interface Command: Option D tells the router which interface connects to the internet or external provider. While this is a mandatory step in any NAT setup, it does not define the translation logic itself. You would also need an
ip nat insidecommand on the internal interface for the translation to function correctly.
Actionable Study Tips
To prepare for NAT questions on the current exam, focus on the specific application for each type and the exact syntax required to implement them in Cisco IOS.
- Understand the Use Case: You should quickly identify the appropriate NAT type based on the scenario requirements. Use Static NAT for servers that must be reachable from the outside using a consistent IP address, such as a mail server. Use Dynamic NAT when you have a small block of public IPs and a larger group of users, provided they do not all need simultaneous external access. Use PAT (overload) for the most common implementations, as it allows almost unlimited internal devices to reach the internet using just one public IP address.
- Trace the Packet: Practice by sketching a network diagram. Mark the source and destination IPs as a packet moves from a laptop on the LAN, through the NAT router, and out to a web server. Clearly label the inside local and inside global addresses at the moment of translation to ensure you understand how the IP header changes.
- Build the Configuration: Use Cisco Packet Tracer to build these configurations. Start by creating an access list to identify your internal traffic. Then, apply the
ip nat insideandip nat outsidecommands to the correct interfaces. Finally, write the translation command and verify it. Checking the NAT translation table with theshow ip nat translationscommand will show the logic in action.
Reflection Prompt: If you needed to host a web server (e.g., a customer portal) on your internal network that must be accessible from the internet, which type of NAT would you configure and why? How would this scenario differ from giving all internal employees outbound internet access?
To improve your understanding of how address translation works in various network environments, you can explore this guide on NAT. Learn more about the implementation of NAT gateways on mindmeshacademy.com.
7. Spanning Tree Protocol (STP) and RSTP
Spanning Tree Protocol (STP) is an essential Layer 2 protocol that prevents broadcast storms and logical loops in switched networks containing redundant links. Because STP is vital for network stability and high availability, the CCNA exam tests your knowledge of its operations. You will need to understand root bridge election, port roles, and convergence states. Mastering these concepts allows you to build and troubleshoot resilient local area networks.
Why It's a Core Concept
Redundant switched topologies provide backup paths, but they also create broadcast storms and MAC address table instability. STP solves this by logically blocking specific redundant paths to create a single, loop-free topology. It still allows physical redundancy for fault tolerance if a primary link fails. The current exam requires a clear understanding of how switches exchange Bridge Protocol Data Units (BPDUs) to elect a root bridge. You must also understand the transition to Rapid STP (RSTP). RSTP improves convergence times, which helps maintain performance and uptime in modern networks.
Example Question and Analysis
Question: In a network of three switches, Switch A has a priority of 32768, Switch B has a priority of 24576, and Switch C has a priority of 36864. Assuming all switches are in the same VLAN and have default settings otherwise, which switch becomes the root bridge?
- A) Switch A
- B) Switch B
- C) Switch C
- D) The switch with the highest MAC address
Correct Answer: B) Switch B
Breakdown:
- Root Bridge Election: The election process uses the lowest bridge ID to select the root bridge. This ID includes a configurable bridge priority and the unique MAC address of the switch. A lower numerical value for the priority gives the switch a better chance of becoming the root.
- Switch A (Priority 32768): This is the default priority for Cisco switches. It is a baseline value but does not win if a lower value exists in the network.
- Switch B (Priority 24576): This value is lower than both Switch A and Switch C. Because it is the lowest numerical value among the three, Switch B becomes the root bridge.
- Switch C (Priority 36864): This is the highest numerical value in the set, giving it the lowest preference in the election.
- MAC Address Tiebreaker: Switches only use the MAC address as a tiebreaker if the bridge priorities are identical. Since Switch B has a unique, lowest priority of 24576, the switches do not need to compare MAC addresses in this scenario.
Actionable Study Tips
To pass with confidence, you must learn the election process and port states until they become second nature.
- Master the Election Process: Focus on the two-step rule. First, the switch with the lowest Bridge Priority wins the election. Second, if the priorities match, the switch with the lowest MAC address wins the tiebreaker.
- Learn Port States and Roles: Memorize the classic STP states: Blocking, Listening, Learning, and Forwarding. Note that RSTP simplifies these into Discarding, Learning, and Forwarding. You should also be able to identify Root ports, Designated ports, and Alternate ports in a diagram.
- Use Labs for Visualization: Hands-on practice is the best way to learn. Use Cisco Packet Tracer to build a small network with redundant links. Change the priority values on different switches to see how the topology reacts. Observe how ports move through different states and which ones eventually enter a blocked state to stop loops.
Reflection Prompt: Without STP, what common network issue would immediately arise in a switched network with redundant links, and how would it impact performance or cause an outage?
For practical experience, examine MindMesh Academy's interactive labs. These labs focus on STP topology changes and network convergence to help you prepare for the current exam.
8. DHCP Server Configuration and Operation
Automating IP address assignment is a requirement for modern networking, and the Dynamic Host Configuration Protocol (DHCP) is the service that makes it happen. The current exam evaluates your ability to configure, verify, and troubleshoot DHCP on Cisco IOS routers. This skill involves more than memorizing syntax; you must understand the entire lifecycle of an IP address lease.
Why It's a Core Concept
Manual IP address configuration causes errors and configuration drift in networks of any significant size. DHCP automates this by providing clients with IP addresses, subnet masks, default gateways, and DNS server information. This reduces administrative overhead and makes it easier to scale the network. You must know how to set up a router to act as a DHCP server, reserve addresses for specific devices, and trace the DORA process. DORA stands for Discover, Offer, Request, and Acknowledgment. This four-step sequence defines how a client obtains its configuration. It is a vital service in environments ranging from small offices to enterprise data centers.
Example Question and Analysis
Question: A network administrator needs to configure a DHCP pool on a router for the 10.10.20.0/24 network. The first 15 usable IP addresses within this subnet must be reserved for static assignment to servers. Which command correctly excludes these addresses from being leased by DHCP?
- A)
ip dhcp excluded-address 10.10.20.0 10.10.20.15 - B)
ip dhcp excluded-address 10.10.20.1 10.10.20.15 - C)
ip dhcp pool exclude 10.10.20.1-10.10.20.15 - D)
no ip dhcp pool 10.10.20.1 10.10.20.15
Correct Answer: B) ip dhcp excluded-address 10.10.20.1 10.10.20.15
Breakdown:
- The Goal: You must prevent the DHCP server from leasing host addresses 10.10.20.1 through 10.10.20.15. These are intended for servers or printers requiring static IPs.
- Command Structure: The correct Cisco IOS global configuration command is
ip dhcp excluded-address [start-ip] [end-ip]. This command is entered in global configuration mode, usually before you define the DHCP pool. - Address Range: In a 10.10.20.0/24 subnet, the network ID is 10.10.20.0 and the broadcast address is 10.10.20.255. Usable host addresses range from .1 to .254. The "first 15 usable" addresses start at .1 and end at .15. Option A is incorrect because 10.10.20.0 is the network identifier.
- Incorrect Syntax: Options C and D use incorrect syntax. The
ip dhcp poolcommand begins pool configuration but does not handle address exclusions.
Actionable Study Tips
To prepare for the current exam, move beyond simple configuration. Focus on protocol operation and fixing common issues.
- Practice the Full Sequence: Build a DHCP pool in a lab. Use the following command sequence:
ip dhcp pool [name],network [network-address] [subnet-mask],default-router [gateway-ip], anddns-server [dns-ip]. Verify your results withshow ip dhcp bindingto see assigned addresses. - Memorize DORA: Trace the Discover, Offer, Request, and Acknowledgment steps. Discover and Request messages are sent as broadcasts because the client lacks an IP and the server's identity. Offer and Acknowledgment are typically unicast, depending on the implementation.
- Understand DHCP Relay: Review the
ip helper-addresscommand. This is used on a router interface to forward DHCP broadcasts to a server located on a different subnet. The router acts as a relay agent, converting the broadcast to a unicast directed at the server. This is common in enterprise networks where servers are centralized.
Reflection Prompt: What is the primary benefit of configuring DHCP relay (ip helper-address) on a router, and in what specific network design would it be a requirement for client connectivity?
9. Basic Switch and Router Configuration (IOS Commands)
Performance-based labs make up a significant part of the CCNA exam. These labs test your ability to navigate the Cisco Internetwork Operating System (IOS) to perform basic device setup. When you face CCNA examination questions on this topic, you must show that you know the exact command-line interface (CLI) syntax for configuring switches and routers. You must move beyond theory to demonstrate practical, real-world competence with Cisco hardware.
Why It's a Core Concept
Mastering basic IOS commands is as fundamental as learning the alphabet before writing a technical report. Every advanced task, from setting up routing protocols and VLANs to applying security policies, depends on your ability to navigate configuration modes. You must know how to assign IP addresses, configure passwords, and secure device access. The current exam verifies that you possess the skills required to manage Cisco hardware effectively. These configuration tasks form the base for almost every networking job you will perform in the field.
Example Question and Analysis
Question: A network administrator needs to configure a new router. After connecting via the console port, which sequence of commands correctly sets the hostname to "R1" and assigns the IP address 10.10.1.1/24 to the GigabitEthernet0/0 interface, while also activating it?
- A)
enable->hostname R1->interface gi0/0->ip address 10.10.1.1 255.255.255.0 - B)
configure terminal->hostname R1->interface gigabitethernet0/0->ip address 10.10.1.1 255.255.255.0->shutdown - C)
enable->configure terminal->hostname R1->interface gigabitethernet0/0->ip address 10.10.1.1 255.255.255.0->no shutdown - D)
config t->interface gi0/0->ip address 10.10.1.1 255.255.255.0->no shutdown->hostname R1
Correct Answer: C) enable -> configure terminal -> hostname R1 -> interface gigabitethernet0/0 -> ip address 10.10.1.1 255.255.255.0 -> no shutdown
Breakdown:
enable: You use this command to move from user EXEC mode, which uses theRouter>prompt, to privileged EXEC mode, which uses theRouter#prompt. This step is necessary to gain the authority to enter configuration modes.configure terminal(orconfig t): This command enters global configuration mode, indicated by theRouter(config)#prompt. You must be in this mode to make changes that affect the entire device or to enter sub-modes for specific ports.hostname R1: This command sets the identification name of the router to R1. Using unique hostnames is a standard practice for identifying devices within a larger network.interface gigabitethernet0/0(orint gi0/0): This command enters the configuration mode for a specific interface. The prompt changes toRouter(config-if)#, meaning your commands will now only affect this specific port.ip address 10.10.1.1 255.255.255.0: This assigns both the IP address and the subnet mask to the interface. Both parts are required for the interface to function on the network.no shutdown: Cisco router interfaces are disabled by default. Theshutdowncommand is applied to all ports to prevent security risks. Runningno shutdowntells the router to enable the interface.
Actionable Study Tips
To build the muscle memory required for the current exam, you need to practice these commands until they become second nature.
- Learn Mode Hierarchy: Internalize the flow between configuration levels. You start in User EXEC (
>), move to Privileged EXEC (#), then Global Configuration ((config)#), and finally reach specific sub-modes like Interface ((config-if)#), Line ((config-line)#), or Router ((config-router)#). Knowing your current location in the CLI is vital. - Embrace Command Abbreviation: Practice using shortcuts to save time. Use
conf tforconfigure terminal,int gi0/0forinterface gigabitethernet0/0, andwrforwrite memoryto save your work. These shortcuts are standard in the industry and helpful during the timed exam. - Use the
?Command: The context-sensitive help tool is your most useful resource in the IOS. If you are unsure of a command or the required parameters, type?to see a list of available options without leaving your current mode. - Practice in a Lab Environment: Use a simulator like Cisco Packet Tracer or virtual labs like GNS3 and EVE-NG. Repeatedly practice configuring devices from scratch. Focus on setting passwords, assigning IP addresses, and saving the configuration with the
copy running-config startup-configcommand. This repetition helps you pass with confidence.
Reflection Prompt: Why is saving your configuration using
copy running-config startup-configcritical after you modify a device in a live environment? What are the potential consequences if the router reboots before this command is executed?
10. Troubleshooting Network Connectivity Issues
The ability to troubleshoot systematically is a basic requirement for network engineers, and advanced CCNA questions will test this skill. These questions move past simple configuration and require you to interpret command outputs, diagnose failures across different OSI layers, and identify the root cause of a connectivity problem. Developing a structured troubleshooting methodology is helpful for both the current exam and real-world network administration.
Why It's a Core Concept
Networks eventually experience issues. The CCNA certification validates that you have the skills to identify the cause of failure quickly. Exam scenarios often present a broken network topology and expect you to use diagnostic tools like ping, tracert (or traceroute), and various show commands to isolate the fault. This tests your practical understanding of how Layer 1 (Physical), Layer 2 (Data Link), and Layer 3 (Network) interact. You must understand how issues at the physical level can stop processes at the network level. A methodical troubleshooting approach, similar to those used in standard problem management frameworks, is the best way to handle these scenarios.
Example Question and Analysis
Question: A user on PC1 (192.168.1.10) cannot ping the server at 192.168.2.10. A traceroute command from PC1 successfully reaches the default gateway router, R1 (192.168.1.1), but then stops responding. The output of show ip route on R1 does not show an entry for the 192.168.2.0/24 network. What is the most likely cause of the issue?
- A) A faulty cable is connecting PC1 to the switch.
- B) An access control list (ACL) on R1 is blocking ICMP traffic.
- C) The server at 192.168.2.10 is powered off.
- D) R1 is missing a route to the destination network.
Correct Answer: D) R1 is missing a route to the destination network.
Breakdown:
- A) Faulty cable (Layer 1): If the cable connecting PC1 to the switch were faulty, PC1 would not reach its default gateway, R1. The
tracerouteoutput indicates success up to the gateway, which means the local physical connection is functioning. - B) ACL blocking ICMP: An ACL that blocks ICMP traffic on R1 would typically cause the
tracerouteto show responses such as "!" (host unreachable) or "U" (administratively prohibited) from R1. It would not simply stop responding after the first hop. The missing routing table entry is a more direct explanation for the failure. - C) Server powered off: If the server at 192.168.2.10 were powered down, the
traceroutewould likely complete its path to the specific router responsible for the 192.168.2.0/24 subnet. Only then would it time out while trying to reach the host. The problem in this scenario occurs at R1, which is further back in the path. - D) Missing route (Layer 3): The
show ip routecommand output explicitly stating that there is no entry for the 192.168.2.0/24 network is the main evidence. If R1 has no route for the destination network, it does not know where to forward the packet. The router will drop the packet, which explains why thetraceroutestops at R1. This is a standard Layer 3 routing issue.
Actionable Study Tips
To perform well on troubleshooting questions, use a methodical approach that mirrors professional best practices.
- Follow the OSI Model (Bottom-Up): Start troubleshooting at the physical layer and work up the stack. Check Layer 1 first to see if the interface is in an
up/upstate and that cables are seated correctly. Then move to Layer 2 to check VLAN assignments and MAC address tables before investigating Layer 3 IP addressing and routing protocols. This avoids wasting time on complex configuration checks when a simple physical issue exists. - Master Key
showCommands: You should know exactly what information these commands provide:show interfaces: Use this for Layer 1 and Layer 2 status, checking for input errors, CRC errors, duplex mismatches, and speed settings.show ip interface brief: Use this for a quick summary of interface IP addresses and their current status.show ip route: Use this to verify Layer 3 forwarding logic and to see how the router learned its routes.show cdp neighbors: Use this to find directly connected Cisco devices and verify Layer 2 connectivity.show access-lists: Use this to verify that security policies are not accidentally blocking legitimate traffic.
- Use a Process of Elimination: Look at the symptoms to rule out what is working. If you can successfully ping your gateway, you know that Layers 1, 2, and 3 are working on the local segment. This allows you to focus your search on the remote network or the intermediate routers.
- Practice in a Lab: Hands-on experience is necessary. Use network simulators or the MindMesh Academy simulation environment to break and fix network configurations. Repeatedly fixing common errors builds the intuition needed to solve problems quickly during the exam.
Reflection Prompt: Describe a common troubleshooting scenario where starting at Layer 1 (Physical) first would save significant time compared to looking at Layer 3 (Network) issues. For example, what would be the first thing you check if a brand-new PC can't get an IP address via DHCP?
CCNA Examination Questions — 10-Topic Comparison
| Topic | Implementation Complexity | Resource Requirements | Expected Outcomes | Ideal Use Cases | Key Advantages |
|---|---|---|---|---|---|
| OSI Model and Network Layer Identification | Low — requires memorizing the seven layers and their specific functions. | Minimal — use standard study guides, posters, and technical diagrams. | Clear understanding of layer responsibilities from physical to application layers. | Foundations, theory review, interview prep, and isolating network problems. | Simplifies troubleshooting by using a standardized architectural model for communication. |
| IP Addressing and Subnetting Calculations | Medium — requires consistent practice and high mathematical accuracy. | Calculators for verification and practice lab workbooks. | Accurate IP plans and correct host ranges for subnets. | IP planning, VLAN sizing, exam simulations, and network segmentation. | Enables efficient address allocation and prevents design-related network problems. |
| Routing Protocols Comparison (RIP, OSPF, EIGRP) | Medium–High — involves understanding protocol behaviors and specific tuning. | Lab environments, simulators, and official protocol documentation. | Informed protocol selection and optimized routing across the network. | Multi-site design, protocol migration decisions, and scaling enterprise networks. | Guides protocol choice based on scale, convergence speed, and vendor fit. |
| VLAN Configuration and Inter-VLAN Routing | Medium — involves multi-device configuration across switches and routers. | Physical switches, routers, or network simulators like Packet Tracer. | Segmented networks and successfully routed inter-VLAN traffic flow. | Network segmentation, security zones, and broadcast traffic reduction. | Improves security and performance by isolating traffic to specific groups. |
| Access Control Lists (ACL) Configuration & Filtering | Medium — rule logic is sensitive and requires careful ordering. | Packet examples, lab simulators, and standard ACL templates. | Controlled traffic flow and the ability to enforce security policies. | Perimeter filtering, subnet protection, and basic network security. | Provides granular traffic control and enhanced protection for internal resources. |
| Network Address Translation (NAT) Implementation | Medium — includes configuring static, dynamic, and PAT modes. | Public IP pools, NAT-capable devices, and topology diagrams. | Connectivity between private networks and the public internet. | Internet access for private networks and server publishing. | Conserves IPv4 space while hiding internal addresses from external users. |
| Spanning Tree Protocol (STP) and RSTP | Medium — configuration is highly dependent on the physical topology. | Multiple switches, topology diagrams, and simulation software. | A loop-free Layer 2 topology that maintains path redundancy. | Redundant switch networks and high availability in campus designs. | Prevents loops while allowing redundancy; RSTP provides much faster convergence. |
| DHCP Server Configuration and Operation | Low–Medium — configurations are straightforward but require attention. | DHCP servers, network segments, and relay agent configurations. | Automated IP assignments and efficient management of client leases. | Dynamic host environments and scaling across multiple VLANs. | Reduces manual IP errors and simplifies the provisioning of devices. |
| Basic Switch and Router Configuration (IOS Commands) | Low — requires familiarity with the command-line interface. | Access to Cisco devices or software emulators like GNS3. | Functional initial device configurations and saved setup files. | Initial device bring-up, lab practice, and basic administration. | Essential hands-on skills required for all advanced network configurations. |
| Troubleshooting Network Connectivity Issues | High — an integrative skill drawing from all other exam topics. | Diagnostic tools like ping, plus access to live devices. | Root-cause identification and effective remediation of network failures. | Production incident resolution, support roles, and network monitoring. | Critical skill that improves network uptime and professional career growth. |
Your Strategic Path to CCNA Certification
You have just finished working through these ten CCNA examination questions. We covered the OSI model, subnetting calculations, and the configuration of access control lists and NAT. We focused on the logic behind each answer to move beyond simple memorization toward technical fluency. This guide provides a clear blueprint for understanding how the exam is structured and how its technical requirements function. It helps you see the logic behind the questions so you can build a more solid understanding of the material.
Success on the CCNA exam depends on how well you can connect different concepts into a single workflow. Knowing specific commands to configure a VLAN is not enough. You must understand how that VLAN interacts with routing protocols, security lists, and DHCP services to solve a business problem. The current exam measures your ability to link information across different network domains rather than testing facts in isolation.
Synthesizing Knowledge into Exam Readiness
Your preparation needs to be intentional. Reading through questions offers fewer benefits if you are not actively working with the material. You need a specific strategy for your review sessions to ensure you are ready for the testing center. A passive approach will not help you retain the details required for high-level certification.
Follow these principles to improve your study habits:
- Identify Your Gaps: Look back at topics like IP addressing and troubleshooting. Determine which areas were the most difficult for you. Be honest about your performance and make those domains your priority for study. A single weak link in your technical knowledge can lead to mistakes and lower your confidence when you sit for the test.
- Embrace Active Recall: Avoid just reading through the technical explanations. Cover the text and try to explain the solution from memory. Walk through the logic step-by-step. This active recall builds stronger mental connections than passive reading. It makes it easier to remember technical details when you are under the pressure of the actual exam.
- Contextualize Every Command: Whenever you learn a new Cisco IOS command, answer three questions. What problem does this command fix? What are common configuration errors? How does it fit into the overall network design? This moves you beyond syntax and prepares you for the scenario-based questions that Cisco often includes in the certification.
The Power of Strategic Practice
The CCNA is a long-term project. The amount of information is significant, and it is easy to forget older topics as you move forward. A methodical practice strategy is the best way to handle this volume. Consistency is more important than the total number of hours you spend in one day.
Spaced repetition is a proven technique for keeping information in long-term memory. This method involves reviewing specific topics at set intervals, usually right as you are about to forget them. This prevents the need for cramming. Instead, you build technical knowledge that remains available to you during the exam and in your professional career.
Strategic Insight: The current exam evaluates your accuracy and speed. You must apply what you know quickly. Spaced repetition creates the instant recall needed to handle complex network scenarios without second-guessing yourself. This method is also effective for certifications like the PMP or ITIL, where being able to recall a wide range of information is a requirement.
By using this guide and a structured practice plan, you can pass with confidence. You will be ready for a professional role in networking. You will stop being a student who answers questions and become a practitioner who can manage complex network challenges.
If you want a specific path to certification, MindMesh Academy can help. We use spaced repetition and adaptive quizzes that focus on your weak areas. This ensures every minute of your study time is efficient. Find our complete CCNA prep course and start your path to success at MindMesh Academy.
Ready to Pass the CCNA?
Study with expert guides, practice exams, and spaced repetition flashcards at MindMesh Academy. These help pass the current exam with confidence:
- CCNA Study Guide – Thorough prep for the Cisco CCNA certification

Written by
Alvin Varughese
Founder, MindMesh Academy
Alvin Varughese is the founder of MindMesh Academy and holds 15 professional certifications including AWS Solutions Architect Professional, Azure DevOps Engineer Expert, and ITIL 4. He's held senior engineering and architecture roles at Humana (Fortune 50) and GE Appliances. He built MindMesh Academy to share the study methods and first-principles approach that helped him pass each exam.